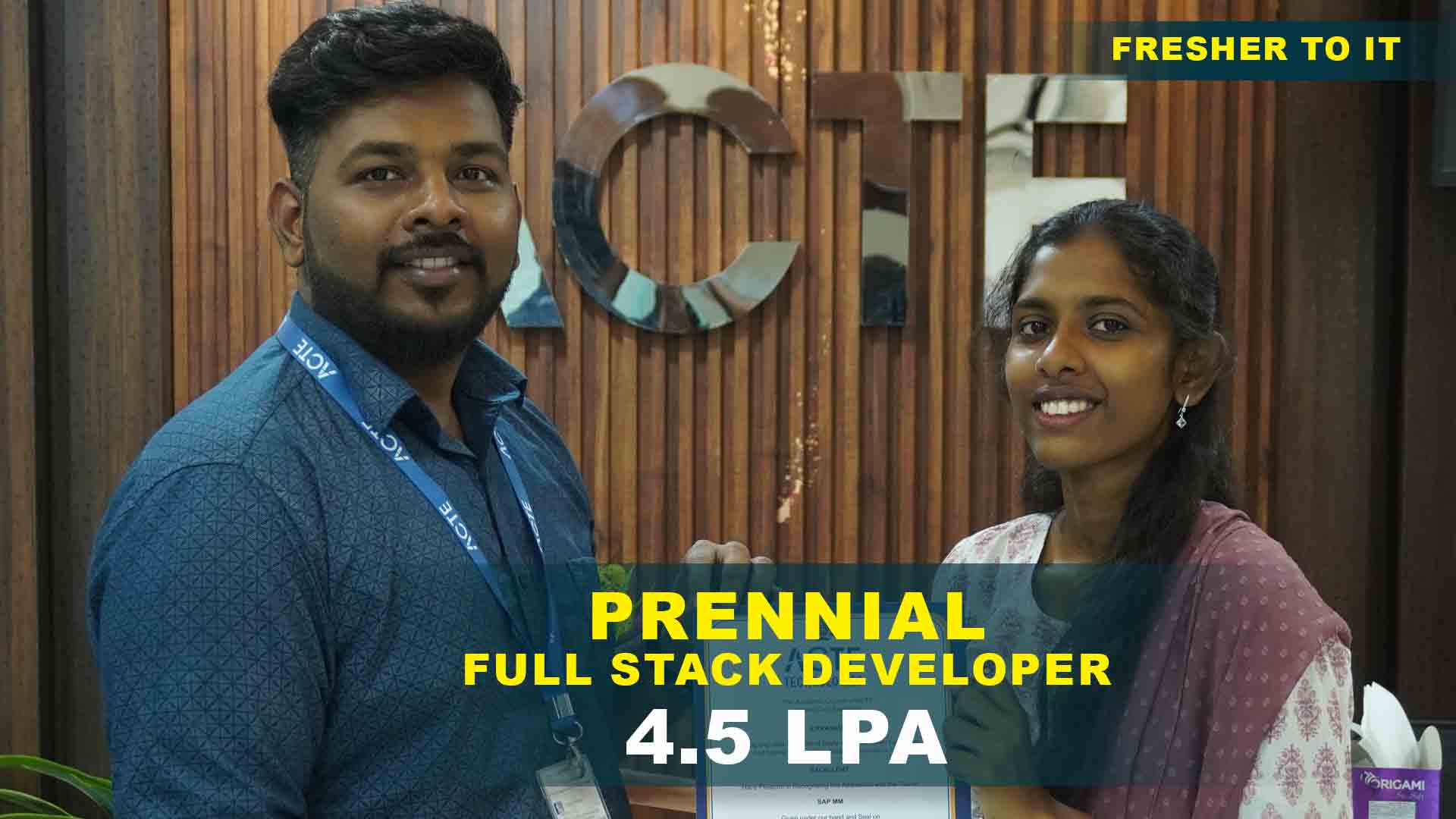
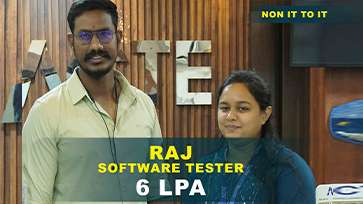
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculum Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
Networking & Cyber Security Program Training Projects
Become a Networking & Cyber Security Program Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Basic Network Setup
Configure routers, switches, and IP addressing. Understand network fundamentals.
Firewall Configuration
Set simple firewall rules to control traffic. Implement basic security policies.Devices connected via router, switch .
Wi-Fi Security
Set up and secure wireless networks. Protect wireless communications.Provides mobility and convenience.
VPN Setup
Configure site-to-site and remote-access VPNs. Enable secure remote connectivity.
Intrusion Detection
Deploy IDS/IPS solutions to monitor threats. Detect and prevent attacks and monitoring activities.
Security Auditing
Perform vulnerability assessments and penetration tests. Identify security weaknesses.
SIEM Integration
Use Security Information and Event Management tools. Centralize and analyze security events.
Incident Response
Develop and test response plans for cyber incidents. Prepare for security breaches.
Advanced Threat Protection
Implement endpoint security and threat intelligence. Defend against sophisticated cyber attacks.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Networking & Cyber Security Training Overview
Uses of Networking and CyberSecurity Training in Omr
Networking and CyberSecurity certification in Omr equips professionals with the knowledge to protect digital infrastructure, secure data, and defend against cyber threats. It is ideal for careers in ethical hacking, network defense, and security auditing. With growing demand from IT, banking, and eCommerce industries, this training provides practical insights into configuring firewalls, monitoring threats, and managing security protocols in real-time environments.Pune is ideal for cybersecurity learning due to its booming IT ecosystem, presence of startups, and numerous training communities.Courses often include practical labs, cyber-range simulations, and attack–defense scenarios, giving students hands-on exposure to real threats.
Industry Projects of Networking and CyberSecurity Course in Omr
- Firewall Configuration Project: Set up, manage, and monitor firewalls using pfSense and Cisco ASA to secure internal networks. Implement and configure IDS/IPS tools such as Snort or Suricata to detect.
- Vulnerability Assessment Lab: Use tools like Nessus and OpenVAS to identify and report security flaws in a simulated corporate environment.Use tools like Nessus and OpenVAS to identify and report security flaws.
- Wi-Fi Security Implementation: Configure WPA3 and RADIUS authentication in an enterprise Wi-Fi network to prevent unauthorized access.Deploy and configure tools like Splunk or ELK Stack to collect, analyze, and correlate security logs.
- Phishing Attack Simulation: Design and detect simulated phishing attacks using tools like Gophish, analyzing user response and improving awareness.Configure WPA3 and RADIUS authentication in an enterprise.
- SIEM and Log Analysis Project: Deploy Splunk or ELK Stack to collect and analyze logs for detecting unusual behavior and potential threats.Simulate a cyberattack scenario and practice containment.
What About Networking and CyberSecurity placement in Omr
Networking and CyberSecurity Training in Omr provides comprehensive knowledge of network protocols, cyber laws, encryption methods, and threat detection strategies. It’s designed to meet the increasing need for security in organizations and infrastructure. Learners are trained on both theoretical and hands-on aspects, ensuring job readiness in roles like Security Analyst, Penetration Tester, or SOC Engineer. The course is aligned with certifications like CEH and CompTIA Security+.Configuring routers, switches, and Wi-Fi networks.Configuring pfSense, Cisco ASA, and UTM devices.Using IDS/IPS tools to detect malicious traffic.Handling cyber incidents and performing digital investigations.
How to Improve Skills in Networking and CyberSecurity training Course?
- Certify with Industry Standards: Networking and cybersecurity training with placement can pursue global certifications such as CEH, CISSP, or CCNA Security to validate your skills.Roles like Network Engineer, SOC Analyst, Ethical Hacker, Penetration Tester.
- Practice in Simulated Labs: Use platforms like TryHackMe, Hack The Box, or Cyber Ranges for real-world attack and defense exercises.Professionals can secure enterprise networks and prevent data breaches.
- Stay Updated with Threat Intelligence: Follow security bulletins, CVE databases, and forums like Krebs on Security or ThreatPost.Opportunities in IT companies, banks, government, defense, and multinational organizations.
- Participate in Capture the Flag (CTF): Join ethical hacking competitions and challenges to apply knowledge in a timed, practical environment.Pursue global certifications such as CEH, CISSP, or CCNA Security to validate your skills.
Company Role Opportunities in Networking and CyberSecurity Placement in Omr
Networking and CyberSecurity Course in Omr ,Graduates can enter roles such as Network Security Engineer, SOC Analyst, Cybersecurity Consultant, or Incident Responder. Companies in Pune, especially in finance, telecom, and IT services, are actively recruiting cyber talent. Government sectors and defense contractors are also expanding their cybersecurity workforce. With increasing ransomware threats and data breaches, the job market remains resilient and rapidly growing.Design, implement, and manage LAN/WAN/Wi-Fi networks.Monitor network performance and troubleshoot connectivity issues.Monitor and analyze security events using SIEM tools (Splunk, ELK).Detect and respond to network intrusions and threats.
Career Opportunities After Networking & Cyber Security Training
Cyber Security Analyst
A Cyber Security Analyst is responsible for monitoring, analyzing, and responding to security incidents across networks and systems. They work proactively to identify vulnerabilities, implement security measures like firewalls and encryption and ensure compliance with data protection.
Network Security Engineer
A Network Security Engineer designs and implements secure network architectures to protect internal networks from unauthorized access, data breaches, and attacks. Their job includes configuring firewalls, VPNs, intrusion detection/prevention systems (IDS/IPS).
Ethical Hacker
Ethical Hackers, also known as Penetration Testers, are cybersecurity professionals hired to simulate real-world attacks on an organization’s systems. Their goal is to identify weak points before malicious hackers can exploit them. They use tools and techniques.
Information Security Manager
An Information Security Manager oversees a company’s entire cybersecurity framework. They develop and enforce policies, manage teams, and align security initiatives with business goals. Their responsibilities include supervising risk assessments, leading incident response efforts.
SOC
A SOC Analyst works in a centralized cybersecurity team that continuously monitors an organization’s IT infrastructure. They are responsible for detecting, analyzing, and responding to security threats in real-time. Using tools like SIEM (Security Information and Event Management).
Cloud Security Specialist
A Cloud Security Specialist focuses on protecting data, applications, and infrastructure within cloud platforms such as AWS, Azure, or Google Cloud. They implement and manage cloud-native security tools, enforce identity and access management (IAM) and ensure compliance with cloud security.
Skill to Master
Network Configuration & Troubleshooting
Cyber Threat Analysis
Ethical Hacking & Penetration Testing
Risk Assessment & Management
Mastery of Security Tools
Incident Response & Forensics
Identity & Access Management
Cloud Security
Encryption & Cryptography
Operating System Security
Cybersecurity Compliance & Policies
Analytical & Problem-Solving Skills
Tools to Master
Wireshark
Nmap
Metasploit Framework
Kali Linux
Nessus
Snort
John the Ripper
Splunk
Netcat
Burp Suite
Autopsy
Cloud Security Tools
Learn from certified professionals who are currently working.

Training by
Mahesh, having 7 yrs of experience
Specialized in: Network Infrastructure Design, Firewall Configuration, Ethical Hacking, and Cyber Threat Analysis.
Note: Mahesh is renowned for his hands-on teaching style and his deep knowledge of security compliance frameworks like ISO 27001 and NIST. He’s mentored over 1,000 students into successful cybersecurity careers.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Networking & Cyber SecurityCertification

Yes, Networking and cybersecurity training course offered various categories of cybersecurity certifications are offered including CEH, CISSP, CompTIA Security+, and CISM.
Absolutely. Many professionals pursue layered certifications to specialize in different areas like penetration testing, compliance, or cloud security.
Yes, there is a possibility to complete the cybersecurity exam remotely many global certification bodies such as such as EC-Council (CEH), ISC² (CISSP), offer online proctored exams.
Networking and cybersecurity course certification not always, but hands-on labs and project exposure significantly improve understanding and job-readiness..
Frequently Asked Questions
- You will learn about firewalls, intrusion detection, ethical hacking, vulnerability assessment, and tools like Wireshark, Metasploit, and Nmap.
- Tools Covered in Wireshark, Metasploit, Nmap, Nessus, OpenVAS, Snort, Splunk/ELK Stack, and Gophish.
- Networking and cybersecurity course certification no need experience is required; the course is beginner-friendly and gradually moves to advanced topics.
- ACTE guides you through real-time projects and provides mentorship to build a strong portfolio that showcases your practical skills.
- Yes,ACTE will issue a recognized course completion certificate.The certificate can be used to validate your skills for job applications, career growth, and eligibility for global certifications.
- Yes, there’s a high demand for cybersecurity professionals. ACTE’s networking and cybersecurity training with placement support helps you land roles like Security Analyst, Network Administrator.
)



