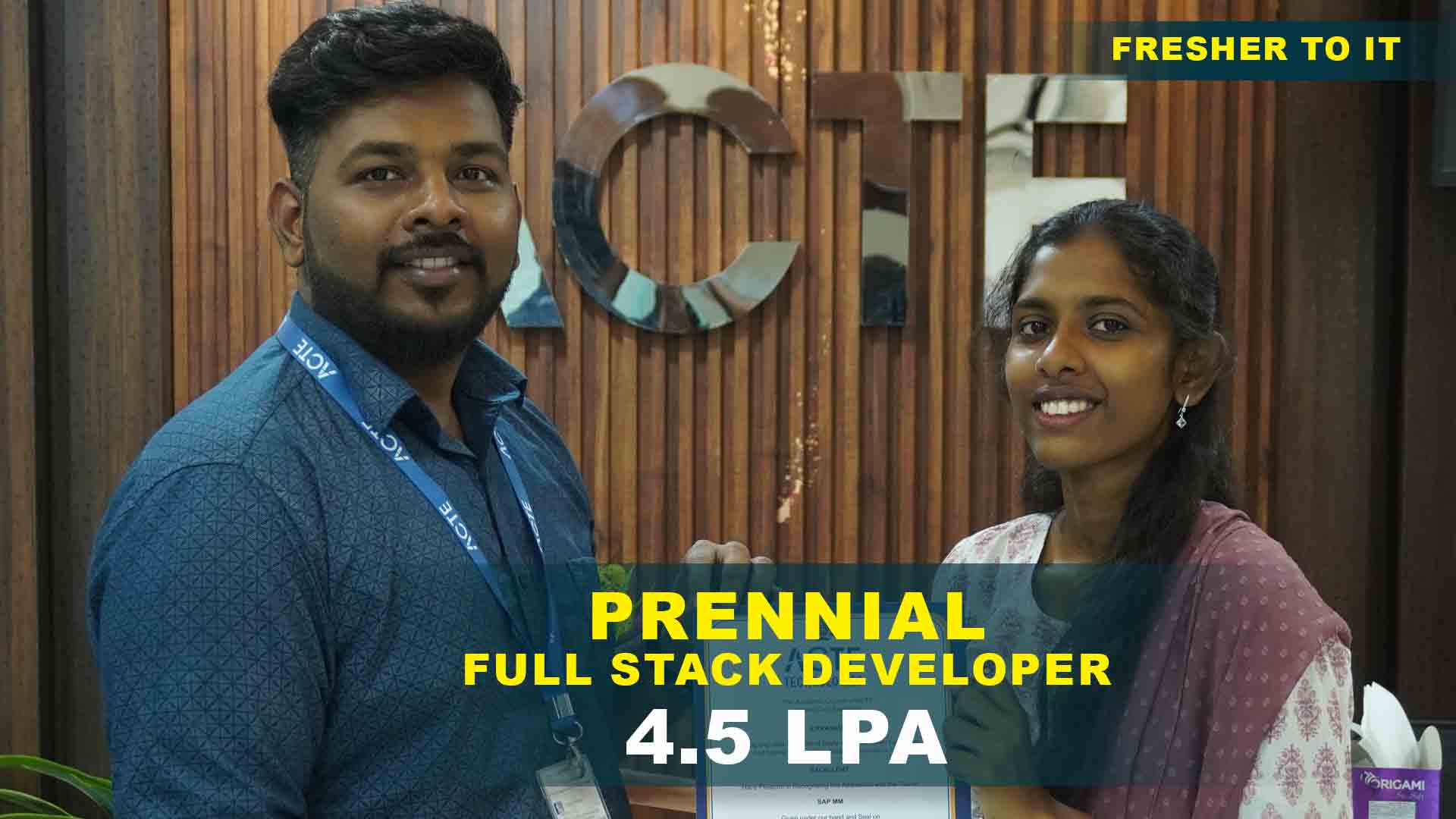
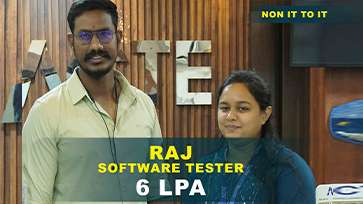
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculam Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
- Basics of networking and cyber threats
- Types of networks and protocols
- Cybersecurity fundamentals
- Threat landscape and attack vectors
- Security policies and compliance standards
- Overview of network devices and firewalls
- Layered architecture of networking models
- Functions of each OSI layer
- TCP/IP communication principles
- Routing and switching basics
- Subnetting and IP addressing concepts
- Operating system security principles
- User account and permissions management
- File system security in Linux and Windows
- Firewall configuration basics
- Firewalls, IDS, and IPS concepts
- Packet filtering and NAT basics
- Secure network design strategies
- Monitoring traffic and detecting anomalies
- VPN and encryption protocols
- Wireless network security best practices
- Footprinting and reconnaissance techniques
- Vulnerability scanning and analysis
- Exploitation and privilege escalation methods
- Password cracking and social engineering
- Penetration testing methodology
- Common web vulnerabilities (OWASP Top 10)
- SQL Injection, XSS, and CSRF attacks
- Directory traversal and session hijacking
- Web application firewall deployment
- Wireless protocols and encryption methods
- Wi-Fi hacking and protection techniques
- Mobile OS security essentials
- Rogue AP and evil twin attack scenarios
- IoT device security basics
- Network traffic analysis tools
- Intrusion detection systems and alerts
- Threat intelligence gathering
- Event correlation and SIEM overview
- Incident response strategies
- Real-time monitoring simulations
- Malware analysis and reverse engineering
- Security auditing and compliance testing
- Advanced penetration testing frameworks
- Incident response planning and execution
Networking & Cyber Security Training Projects
Become a Networking & Cyber Security Training in Maraimalai Nagar Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Password Strength Analyzer
Build a simple tool to evaluate password complexity. Understand hashing techniques and weak-password patterns.
Basic Port Scanner
Create a scanner to check open ports on a target system. Learn network fundamentals and scanning principles.
Wi-Fi Network Monitor
Develop a script to detect nearby Wi-Fi networks and signal strength. Introduces wireless scanning and basic security checks.
Vulnerability Assessment Tool
Build a tool to identify outdated software and weak configurations. Strengthen skills in system auditing and enumeration.
Web Application Penetration Tester
Implement a tool to check XSS, SQLi, and other vulnerabilities. Practice web security testing techniques effectively.
Secure File Encryption System
Create a tool to encrypt/decrypt files with strong algorithms. Learn practical cryptography implementation and secure data handling.
Custom Intrusion Detection System (IDS)
Design an IDS to detect suspicious traffic patterns in real-time. Focus on advanced threat monitoring and analysis techniques.
Automated Exploit Framework
Build a framework to automate recon, scanning, and exploitation. Gain deep insight into exploit development and scripting.
Advanced Malware Analysis Sandbox
Develop an isolated system for malware behavior analysis. Master reverse engineering and threat detection.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Networking & Cyber Security Overview
Goals Accomplished by Networking & Cyber Security Training in Maraimalai Nagar
Networking & Cyber Security Training in Maraimalai Nagar equips learners with strong foundations in network infrastructure, security protocols, threat mitigation techniques, real-world networking environments including LAN, WAN, routing, and switching concepts, hands-on exposure to securing networks against malware, phishing, ransomware, intrusion attacks, firewall configuration, vulnerability assessment, penetration testing practices, monitoring network traffic, identifying security breaches, troubleshooting, incident response capabilities, compliance standards awareness, secure network architecture design for enterprises, and industry-aligned projects that enhance job readiness and confidence while bridging theoretical knowledge with real-time cyber security implementation.
Future Career Opportunities Emerging from Networking & Cyber Security Course in Maraimalai Nagar
- Network Security Engineer: Network Security Engineers design, implement, and manage secure network infrastructures.They configure firewalls, IDS/IPS systems, and VPNs to protect enterprise data.The role involves monitoring threats and responding to security incidents.Professionals work closely with IT teams to strengthen network defenses.This role is highly demanded across IT, banking, and telecom sectors.
- Cyber Security Analyst: Monitor systems for suspicious activity and cyber threats.Cyber Security Analysts monitor systems for suspicious activity and cyber threats. They analyze security logs and investigate breaches to prevent future attacks. Analysts perform vulnerability assessments and risk analysis. They help organizations comply with security policies and standards. This role offers strong career growth in security operations centers (SOC).
- Network Administrator: Network Administrators manage daily network operations and ensure uptime.They handle routing, switching, and network troubleshooting.Security patching and access control are key responsibilities. Admins ensure reliable and secure data communication. This role is ideal for professionals starting a networking career.
New Frameworks Introduced in Networking & Cyber Security Certification in Maraimalainagar
Networking & Cyber Security courses introduce modern security frameworks aligned with enterprise needs including layered security architecture models, zero-trust frameworks, defense-in-depth strategies, network monitoring and incident response frameworks, vulnerability management and penetration testing frameworks, security governance and compliance models for audit readiness, automation frameworks using scripts and tools to enhance response speed, risk assessment and threat modeling frameworks, cloud and hybrid network security frameworks, secure configuration baselines practice, helping learners implement scalable and resilient security solutions.
Trends and Essential Skills Related to Networking & Cyber Security Training Placement in Maraimalai Nagar
- Rising Cyber Threat Landscape: Increasing cyberattacks have raised demand for skilled security professionals. Organizations face sophisticated ransomware, phishing, and DDoS attacks daily. Training provides essential threat detection and mitigation skills.
- Cloud Security: Securing cloud and hybrid networks is a key requirement. AWS, Azure, and GCP environments need specialized security configurations. Multi-cloud strategies demand comprehensive protection expertise.
- Automation Skills: Scripting and security automation tools are essential. Python, Bash, and PowerShell streamline incident response processes. SOAR platforms reduce manual intervention significantly.
- Compliance Knowledge: Understanding security regulations and standards is critical. GDPR, HIPAA, PCI-DSS, and ISO 27001 compliance is mandatory. Audit preparation skills ensure regulatory adherence.
- Hands-on Expertise: Employers prefer candidates with lab and project experience. Virtual labs simulate real enterprise environments effectively. Practical projects demonstrate applied knowledge to recruiters.
- Troubleshooting: Real-time troubleshooting skills are highly valued. Network packet analysis identifies attack patterns quickly. Log correlation reveals complex security incidents accurately.
- Certification Value: Industry certifications significantly boost employability. CompTIA Security+, CEH, and CISSP validate professional competence. Certified professionals command higher salary brackets consistently.
- Continuous Learning: Staying updated with evolving threats is essential. New vulnerabilities emerge daily requiring constant awareness. Threat intelligence feeds provide real-time attack information.
Applications and Uses of Networking & Cyber Security Certification in Maraimalainagar
Networking & Cyber Security Training prepares learners to secure enterprise networks and IT infrastructure, protect systems from cyberattacks and data breaches, implement firewalls, VPNs, intrusion detection systems, monitor network traffic, respond to incidents effectively, conduct vulnerability assessment and penetration testing, ensure secure data transmission across networks, support compliance with security regulations, and is widely applied in IT services, banking, healthcare, telecom industries where automation skills improve security operations efficiency to enable robust, secure, and reliable network environments.
Career Opportunities After Networking & Cyber Security Training
Node.js Developer
Node.js Developers build scalable server-side applications using Node.js. They design backend logic, APIs, and microservices, collaborating with front-end developers. They manage asynchronous operations.
Backend Developer
Backend Developers focus on server-side logic, database management, and API development. They create RESTful or GraphQL APIs, design efficient database schemas, and optimize queries for performance.
Full-Stack Developer
Full-Stack Developers handle client-side and server-side development. They integrate Node.js backend services with front-end frameworks, design RESTful APIs, and manage database operations.
API Developer
API Developers design and develop RESTful or GraphQL APIs for client-server communication. They work with Node.js frameworks, define endpoints, and ensure APIs are scalable and secure.
DevOps Engineer (Node.js focus)
DevOps Engineers manage deployment pipelines, cloud infrastructure, and CI/CD workflows for Node.js applications. They automate builds, tests, and deployments, and monitor server performance.
Real-Time Application Developer
Real-Time Application Developers build collaborative applications using Node.js and WebSockets. They manage concurrent users and handle low-latency communication. These developers ensure scalability.
Skills To Master
Penetration Testing
Network Security
Vulnerability Assessment
Web Application Security
Cryptography
Malware Analysis
Linux & Shell Scripting
Wireless Security
Reverse Engineering
Threat Intelligence
Incident Response
Security Auditing
Tools To Master
Nmap
Metasploit
Burp Suite
Wireshark
John the Ripper
Hydra
Nikto
Aircrack-ng
Nessus
OWASP ZAP
Hashcat
Kali Linux
Learn from certified professionals who are currently working.

Training by
Vanathi, having 15 years of experience
Specialized in: Networking & Cyber Security Training: Expert in penetration testing, ethical hacking, network defense, and incident response.
Note: Vanathi is recognized for her deep knowledge of network security, ethical hacking techniques, and practical threat analysis.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Networking & Cyber Security TrainingCertification

Networking and Cyber Security Training is indeed a high-paying job, with cybersecurity roles being among the highest-paying in IT due to increasing demand for security experts.
- IT professionals seeking security specialization
- Students aspiring for cybersecurity roles
- Ethical hacking enthusiasts
- System/network administrators
- Industry recognition and credibility
- Job opportunities in IT security
- Validation of practical skills
- Higher earning potential
- Compliance with industry standards
- CEH (Certified Ethical Hacker)
- CompTIA Security+
- OSCP (Offensive Security Certified Professional)
- CISSP (Certified Information Systems Security Professional)
- CCNA Security
- Ethical Hacker
- Penetration Tester
- SOC Analyst
- Security Consultant
- Cybersecurity Analyst
- Malware Analyst
Yes, stacking certifications enhances skills and career versatility.
Hands-on labs and projects during training also prepare learners effectively.
- High-paying roles
- Industry demand growth
- Career stability
- Continuous skill enhancement
Frequently Asked Questions
- No, basic computer knowledge is sufficient.
- Network security, ethical hacking, penetration testing, vulnerability assessment, incident response, and malware analysis.
- Projects are assigned in labs and virtual environments for real-time simulation.
- Yes, a globally recognized certificate is provided after course completion.
- IT professionals
- Students aiming for cybersecurity careers
- Network administrators
- Aspiring ethical hackers
- Ethical Hacker
- Cybersecurity Analyst
- SOC Engineer
- Penetration Tester
- Security Consultant
)



