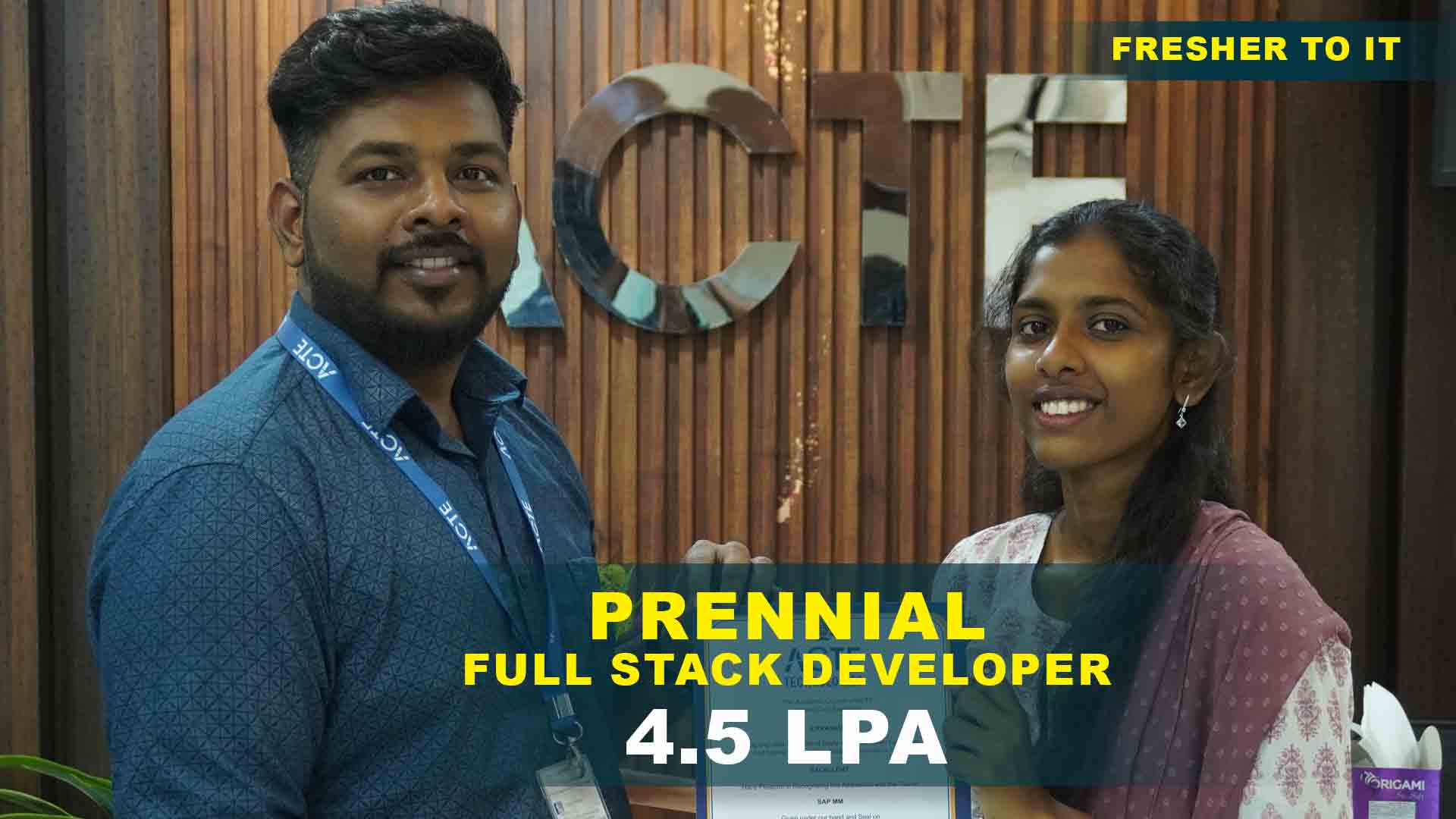
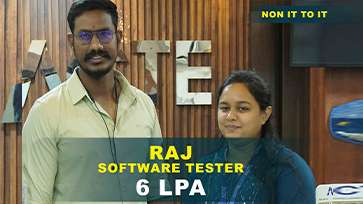
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculum Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
Ethical Hacking Training Projects
Become a Ethical Hacking Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Network Footprinting and Reconnaissance
Practice techniques like WHOIS lookups, DNS enumeration, and email harvesting to gather information about a target system. Understand passive.
Basic Vulnerability Scanning with Nmap
Use Nmap to perform port scans, service identification, and OS detection. Learn how to interpret scan results to find vulnerabilities in a target network.
Password Cracking Simulation
Perform brute-force and dictionary attacks using tools like Hydra or John the Ripper. Understand password strength metrics.
System Exploitation with Metasploit
Use the Metasploit framework to exploit known vulnerabilities on a test machine. Simulate privilege escalation and create reverse shells for access.
Web Application Attack Lab
Conduct simulated attacks like SQL Injection, Cross-Site Scripting (XSS), and Command Injection on a vulnerable web app (e.g., DVWA). Learn how to identify and patch web security flaws.
Wireless Network Penetration Testing
Capture wireless packets and crack WEP/WPA keys using tools like Aircrack-ng. Explore rogue AP creation and wireless sniffing.
Bypassing Firewalls and IDS Systems
Develop evasion strategies to bypass firewalls or intrusion detection systems using packet crafting, tunneling, and encoding techniques
Advanced Persistent Threat (APT) Simulation
Simulate a multi-stage attack mimicking real-world APT tactics. Use command-and-control servers, privilege escalation, and data exfiltration.
Incident Response and Forensics Challenge
Analyze logs, identify malicious activity, and trace attacker footprints after a simulated breach. Document steps taken in detection, containment, and recovery.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Ethical Hacking Overview
Ethical Hacking Training in Siruseri Chennai with Career Opportunities
As cyber threats continue to evolve, the need for certified ethical hackers is surging across industries like IT services, fintech, e-commerce, healthcare, and government. Ethical Hacking Training Institute in Siruseri equips learners with practical skills in vulnerability assessment, penetration testing, social engineering, and network defense using tools like Kali Linux, Metasploit, Burp Suite, and Wireshark. Entry-level professionals can begin their careers as Security Analysts, SOC Trainees, or Junior Pen Testers. With experience, they can progress into roles like Cybersecurity Consultants, Red Team Specialists, or Threat Intelligence Analysts. This Ethical Hacking course prepares learners for job-ready cybersecurity roles in both enterprise IT and freelance domains. Enrolling in a certified Ethical Hacking Training with Placement program offers a strategic path to a high-demand, future-proof cybersecurity career.
Prerequisites for Ethical Hacking Certification course in Siruseri
- Basic Networking Concepts: Understanding of IP addressing, ports, TCP/IP stack, and routing.
- Familiarity with Operating Systems: Knowledge of Windows and Linux command-line usage is essential.
- Understanding of Security Fundamentals: Basic grasp of firewalls, VPNs, antivirus, and malware types.
- Scripting Knowledge (Optional): Familiarity with Python or Bash aids in writing custom scripts.
- Problem Solving & Curiosity: A keen interest in exploring systems and uncovering security flaws.
Why Enroll in Ethical Hacking Training with Placement
Ethical Hacking training with Certification is a core pillar of modern cybersecurity strategies. This Ethical Hacking course helps students and professionals master key techniques like footprinting, scanning, exploitation, and post-exploitation with real-time scenarios and lab simulations. Learners are guided through Red Team tactics, bug bounty workflows, and defense mechanisms for secure system design. Ethical Hacking Training with Placement support includes interview coaching, resume reviews, and direct referrals to cybersecurity firms, MSSPs, and startups. With cybercrime on the rise, companies actively seek certified professionals—making this course a powerful career launchpad.
Modern Techniques Taught in Ethical Hacking Training with Certification
- Reconnaissance & Footprinting: Use tools like Nmap, Maltego, and Google Dorking for intelligence gathering.
- Scanning & Vulnerability Assessment: Perform network and web scans using Nessus, Nikto, and OpenVAS.
- Exploitation & Payload Delivery: Gain hands-on experience with Metasploit and custom shellcode injection.
- Social Engineering Attacks: Learn phishing tactics, credential harvesting, and human-based exploitation.
- Post-Exploitation & Privilege Escalation: Understand maintaining access, covering tracks, and lateral movement.
Latest Tools Covered in Ethical Hacking course
The training includes tools like Kali Linux, Burp Suite, Metasploit Framework, Wireshark, Hydra, and John the Ripper. Learners also get introduced to OWASP ZAP, Aircrack-ng, Ettercap, and Nmap, ensuring they are proficient with both offensive and defensive tools. Simulated lab environments and Capture-the-Flag (CTF) exercises give learners practical exposure to Ethical Hacking training with Certification scenarios. This hands-on learning ensures you're fully prepared for CEH certification and real-world cybersecurity challenges.
Career Opportunities After Ethical Hacking Training
Ethical Hacker / Penetration Tester
Perform authorized tests on systems to uncover security flaws and help fix them before they’re exploited by real-world attackers.
Cybersecurity Analyst
Watch over networks, identify abnormal activity, and respond to threats with reports and actions that strengthen digital defense.
Security Consultant
Guide businesses in setting up strong security, conduct detailed audits, and help apply solutions to reduce cyber risks effectively.
Network Security Engineer
Build secure network setups using firewalls and VPNs while maintaining controls and reducing vulnerabilities across IT systems.
Malware Analyst / Reverse Engineer
Break down malware to learn how it works, create detection patterns, and support development of anti-malware tools and systems.
Incident Responder / SOC Analyst
Handle active threats within SOCs, manage alerts, analyze intrusions, and take quick steps to stop, contain, and prevent breaches.
Skill to Master
Vector Illustration Mastery
Pen Tool Expertise
Typography & Text Effects
Logo Design & Branding
Color Theory & Gradients
Shape Building & Pathfinder Tool
Pattern & Texture Design
Image Tracing & Vectorizing Artwork
Working with Brushes & Effects
Layer & Object Management
Exporting & File Optimization
UI/UX & Web Design Elements
Tools to Master
Selection Tool (V)
Pen Tool (P)
Shape Builder Tool
Pathfinder Panel
Type Tool
Gradient Tool
Eyedropper Tool
Artboard Tool
Image Trace Tool
Brushes & Pencil Tool
Layers Panel
Export & Save Options
Learn from certified professionals who are currently working.

Training by
Ravi Kumar, having 12 yrs of experience
Specialized in: Ethical Hacking, Penetration Testing, Red Teaming, Network Security, and Cyber Forensics.
Note: Ravi Kumar is a seasoned cybersecurity expert with over a decade of hands-on experience in ethical hacking, vulnerability assessments, and threat mitigation. He has trained security teams across finance, telecom, and defense sectors, helping them stay ahead of evolving cyber threats through real-time simulation labs and practical defense strategies.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Ethical Hacking Certification

Earning a Ethical Hacking training Institute in Siruseri validates your expertise in cybersecurity, vulnerability assessment, and penetration testing. With increasing cyber threats across industries, this certification significantly improves your job prospects in IT security, network defense, and information assurance domains.
While certification can guarantee a job, Ethical Hacking Training in Siruseri gives you in-depth technical training, lab simulations, and job preparation support—sharpening your competitive edge in cybersecurity roles.
You don’t need a formal degree, but basic knowledge of networking, operating systems, and system administration is recommended for success in both training and certification exams.
Yes. The course includes lab-based learning on topics such as network scanning, password cracking, exploiting vulnerabilities, and simulating cyberattacks—ensuring you build practical, real-time skills.
Frequently Asked Questions
- Yes. Projects include scanning for open ports, exploiting misconfigurations, and simulating real-world attack vectors in a secure environment.
- Experience the Ethical Hacking Certification course in Siruseri structure and tools
- Interact with the trainer and clarify your questions
- Absolutely. ACTE offers 100% Ethical Hacking Placement in Siruseri with resume building, mock interviews, and connections to over 400+ cybersecurity recruiters.
- Certified ethical hackers with 8+ years of experience
- Proficient in red teaming, SOC operations, and penetration testing
- Provide mentorship and real-world security training
You’ll receive an Ethical Hacking Training Institute in Siruseri Completion Certificate from ACTE, along with preparation for global certifications like CEH (Certified Ethical Hacker).
)



