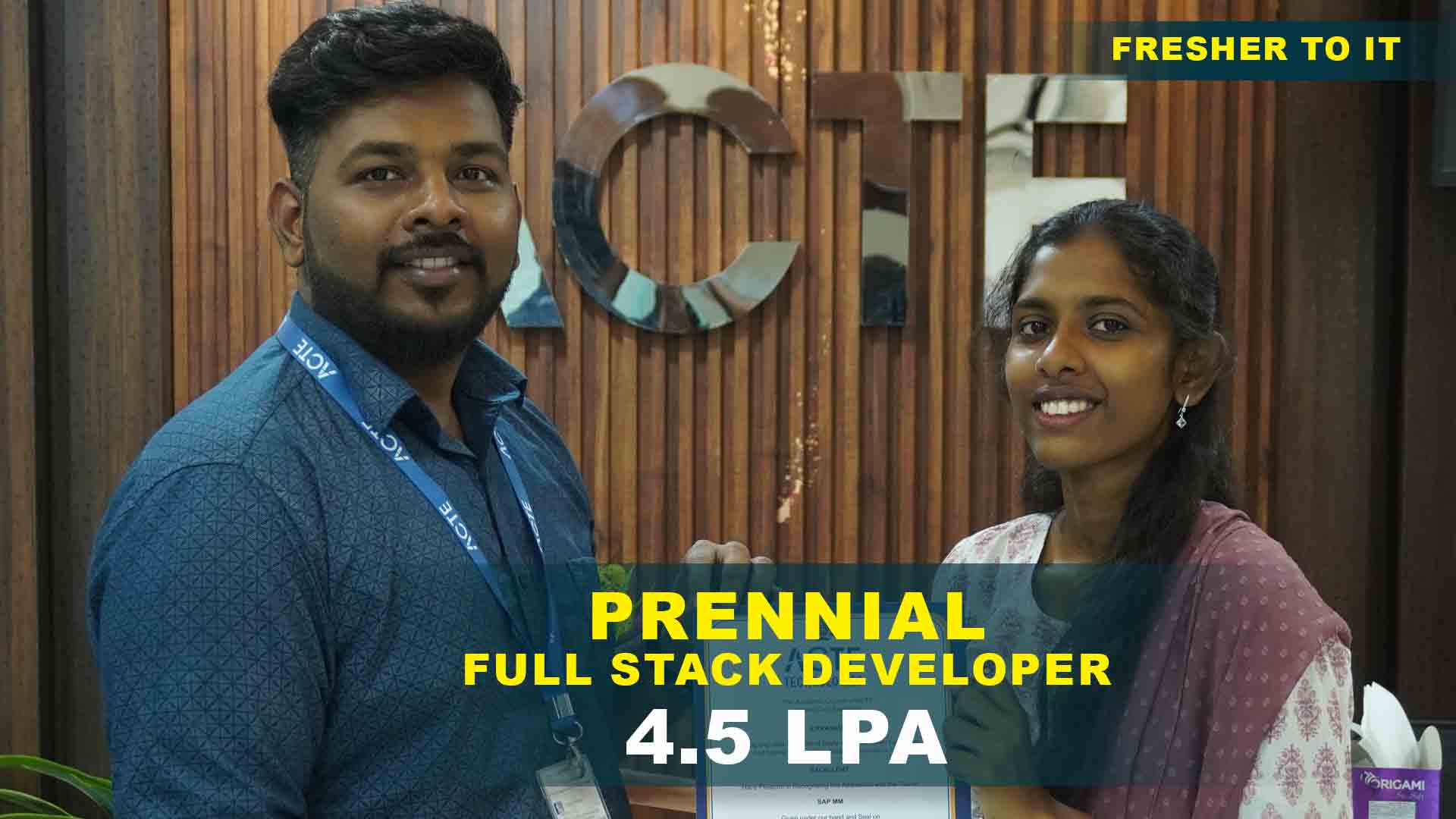
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculum Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
Ethical Hacking Training Projects
Become a Ethical Hacking Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Setting Up a Virtual Hacking Lab
Beginners should start by creating a secure and controlled environment using tools like VirtualBox, Kali Linux and Metasploitable.This helps in practicing ethical hacking techniques.
Basic Network Scanning with Nmap
Learn to use Nmap for discovering devices,scanning open ports,and identifying vulnerabilities in a controlled network. This project helps in understanding network techniques.
Cracking Simple Hashes with Hashcat
Beginners can use Hashcat to crack weak passwords stored in hash formats. This project demonstrates the importance of strong passwords and teaches password recovery techniques.
Penetration Testing of a WordPress Website
Conduct a security audit on a WordPress site using tools like WPScan to identify vulnerabilities, outdated plugins, and misconfigurations.
Man-in-the-Middle (MITM) Attack Simulation
Learn how attackers intercept communication between two parties by setting up an ARP spoofing attack using tools like Ettercap and Wireshark.
Social Engineering Attack Simulation
Create phishing emails and fake login pages (without malicious intent) to understand how attackers manipulate users into revealing sensitive information.
Developing a Custom Exploit with Metasploit
Create and modify exploits in the Metasploit framework to understand how vulnerabilities are exploited in penetration testing.
Advanced Web Application Security Testing
Conduct deep security testing on live web applications, covering topics like server misconfigurations, API security, and zero-day vulnerability exploitation.
Reverse Engineering and Malware Analysis
Analyze malware samples using tools like IDA Pro and Ghidra to understand their behavior, structure, and mitigation techniques.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Ethical Hacking Training Overview
Ethical Hacking Program Course in Indira Nagar with Career Paths
Ethical hacking Class in Indira Nagar opens doors to various cybersecurity roles, making it a lucrative career path for IT professionals. Ethical hackers can work as Penetration Testers, Security Analysts, Cybersecurity Consultants, Incident Responders, and Vulnerability Assessors. With experience, they can advance into roles like Security Architects, Red Team Experts, or Chief Information Security Officers (CISOs). Ethical hackers are in high demand across industries such as finance, healthcare, government, and technology, ensuring strong job stability and competitive salaries.
The Requirements for Ethical Hacking Course Training in Indira Nagar
- Technical Knowledge-Understanding of operating systems (Windows, Linux, macOS),Networking fundamentals (TCP/IP, firewalls, VPNs, etc.),Programming knowledge (Python, Bash, C, or Java)
- Security and Ethical Mindset-Awareness of cybersecurity laws and ethical guidelines,Strong problem-solving and analytical skills,Ability to think like a hacker to identify vulnerabilities
- Hands-on Experience & Certifications-Practical exposure to penetration testing tools (Metasploit, Nmap, Wireshark)Certifications like CEH (Certified Ethical Hacker), OSCP (Offensive Security Certified Professional), or CISSP (Certified Information Systems Security Professional) enhance career prospects
Reasons to Consider Enrolling in Ethical Hacking Programming in Indira Nagar
With cyber threats increasing daily, organizations need skilled ethical hackers to safeguard sensitive data and infrastructure. Enrolling in an ethical hacking developement path in Indira Nagar helps individuals develop hands-on skills to identify security loopholes, conduct penetration testing, and prevent cyber attacks. Ethical hacking is a high-paying, in-demand career with multiple job opportunities worldwide. Additionally, ethical hackers play a crucial role in protecting businesses from financial losses, data breaches, and cybercrimes, making it a rewarding and impactful profession.
Techniques and Trends in Ethical Hacking Development in Indira Nagar
- AI & Machine Learning in Cybersecurity- AI-powered systems analyze transaction patterns to detect fraudulent activities in financial services, e-commerce, and banking,Machine learning models classify and detect malware based on patterns, behaviors, and signatures without relying on traditional rule-based methods.
- Zero Trust Security Model-A security framework that assumes no user or device should be trusted by default, even if inside the network,Every access request is continuously verified based on identity, device security, location, and behavior before granting access.
- Bug Bounty and Ethical Hacking Programs-Companies offer monetary rewards to ethical hackers for identifying and responsibly disclosing security vulnerabilities in their systems, helping to improve cybersecurity,A bug bounty program is a cybersecurity initiative where companies reward ethical hackers for discovering and reporting security vulnerabilities in their systems.
The Most Recent Ethical Hacking Tools
Ethical hackers use a variety of advanced tools to identify and exploit vulnerabilities. Some of the most recent and popular tools include Metasploit, a powerful penetration testing framework; Burp Suite, widely used for web application security testing; and Wireshark, a network protocol analyzer. Other trending tools include Aircrack-ng for wireless security testing, SQLmap for database vulnerability exploitation, and John the Ripper for password cracking. As cyber threats evolve, new tools are constantly developed to enhance security testing capabilities.
Career Opportunities After Ethical Hacking
Ethical hacker
Penetration testers,referred to as ethical hackers,examine the security of an organization's IT infrastructure by simulating cyberattacks. They find vulnerabilities and suggest security fixes using programs .
Analyst for Cybersecurity
A cybersecurity analyst keeps an eye out for security flaws in an organization's networks, systems, and apps. To stop cyberattacks, they assess risks, create security procedures, and put defences in place.
Consultant for Security
Security threats and create customised security plans collaborate with various businesses.To improve an organization's cybersecurity posture,they carry out compliance audits,risk assessments.
Forensic Investigator Digital
Cybercrime analysis, data recovery,and hacker tracking are the areas of expertise for digital forensic investigators.To look into security incidents,they collaborate with government organisations and law enforcement.
Red Team Expert
Red Team experts assess an organization's defences against threats by simulating actual cyberattacks. They carry out sophisticated penetration testing, social engineering techniques, and adversary attack simulations.
Security Engineer
Security engineers are responsible for designing, implementing, and managing security measures to protect an organization's digital infrastructure. They configure firewalls, encryption techniques, and secure networks.
Skill to Master
Networking & Security Fundamentals
Programming & Scripting Skills
Linux & Windows Security
Web Application Security
Penetration Testing
Malware Analysis
Social Engineering
Wireless & IoT hacking
Cryptography & Encryption Techniques
Cloud Security
Digital Forensics
Ethical Hacking Tools & Frameworks
Tools to Master
Nmap
Metasploit
Burp Suite
Wireshark
Nikto
Aircrack-ng
Hydra
John the Ripper
Maltego
Kali Linux
Hashcat
SQLmap
Learn from certified professionals who are currently working.

Training by
Dharshini , having 7+ yrs of experience
Specialized in:Penetration Testing, Vulnerability Assessment, Network Security, Web Application Security, and Ethical Hacking Tools.
Note: Dharshini is a seasoned cybersecurity expert with extensive hands-on experience using tools like Metasploit, Burp Suite, and Nmap. She has a track record of discovering and addressing security vulnerabilities in complex systems, and she is committed to assisting students in understanding both the practical and theoretical sides of ethical hacking.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Ethical Hacking Certification

Pursuing an ethical hacking certification in Indira Nagar validates your expertise in cybersecurity, penetration testing, and network security. It enhances your credibility as a cybersecurity professional and makes you a preferred candidate for security-related job roles.
Prerequisites vary depending on the certification you choose. Some entry-level ethical hacking certifications, like CEH, require basic IT security knowledge, while advanced certifications, such as OSCP, demand hands-on experience with penetration testing tools.
Real-world experience is not mandatory, but it significantly enhances your understanding of cybersecurity threats and solutions. Many certification courses provide hands-on labs and simulated environments where you can practice ethical hacking techniques.
Yes, ACTE Ethical Hacking Training Certification is a valuable investment for individuals looking to build a career in cybersecurity. The course offers comprehensive training, hands-on labs, real-world hacking scenarios, and expert mentorship to equip you with the necessary skills.
Frequently Asked Questions
Yes, we offer a free demo session to help you understand the course structure, teaching methodology, and trainer expertise. This session will give you insights into the syllabus, practical training approach, and the career benefits of ethical hacking.
- Our instructors are certified ethical hackers and cybersecurity professionals with years of industry experience. They have worked in top organizations, handling real-world security challenges and penetration testing projects.
- We provide career guidance, resume-building support, and mock interview sessions.
- We connect students with over 500+ hiring partners for job opportunities.
- Get hands-on experience through internships and live projects.
- Help in showcasing your skills through a strong portfolio and certifications.
After completing the course, you will receive an industry-recognized Ethical Hacking Certification from ACTE. This certification validates your expertise in cybersecurity, penetration testing, and vulnerability assessment. Additionally, the training prepares you for globally recognized certifications such as CEH (Certified Ethical Hacker), OSCP (Offensive Security Certified Professional), and CISSP (Certified Information Systems Security Professional).
- Yes, hands-on learning is a key focus of our course.
- Real-world cybersecurity challenges – Work on live security assessments, penetration testing, and ethical hacking projects.
- Industry-based case studies – Solve real-time hacking scenarios to gain practical knowledge.
- Practical application of tools – Use tools like Metasploit, Burp Suite, Nmap, Wireshark, and Aircrack-ng to develop hands-on skills.
)



