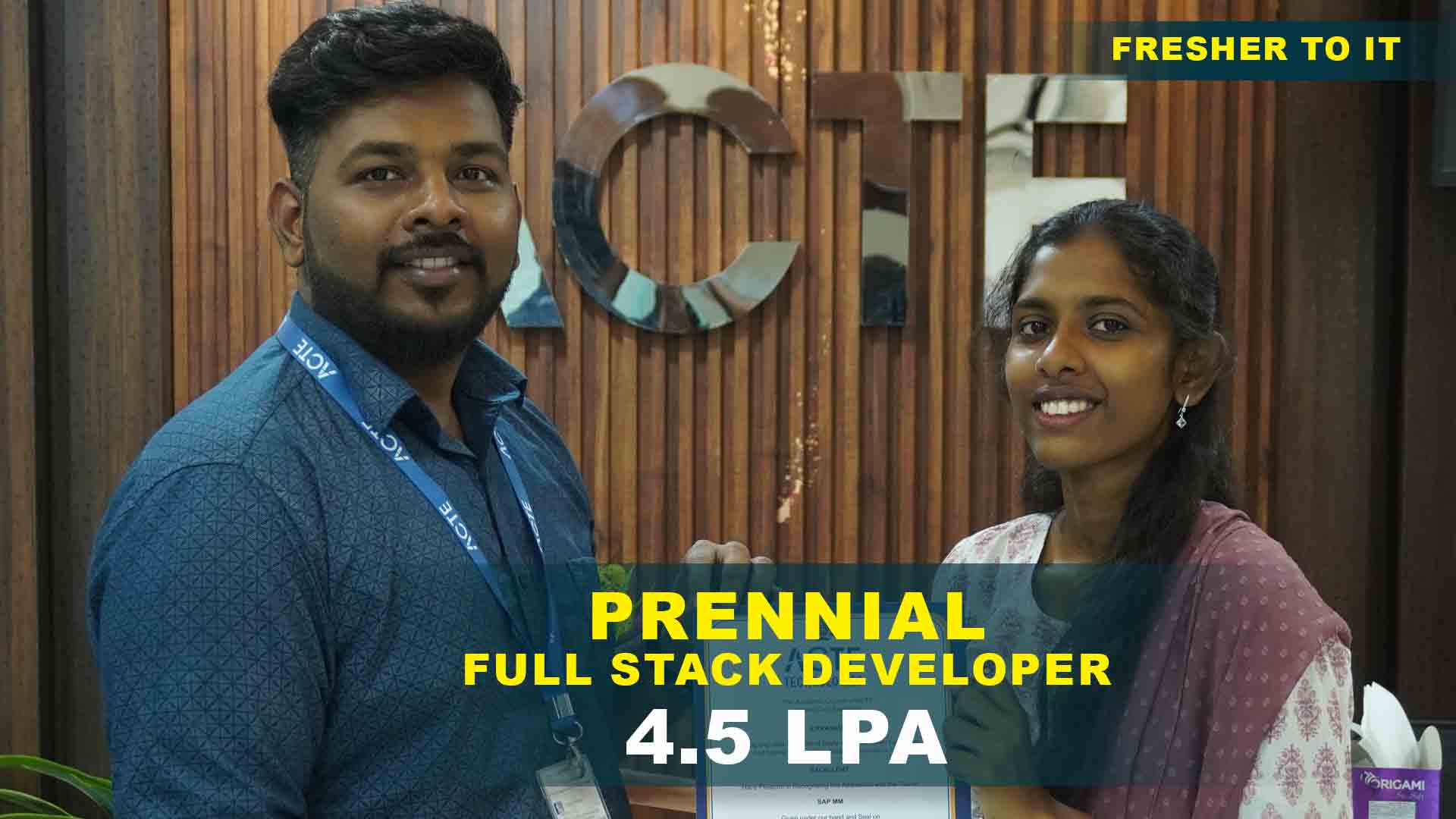
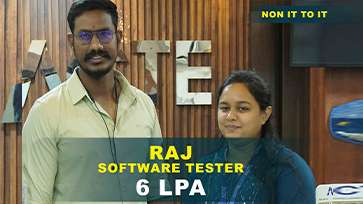
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculam Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
- Overview of Ethical Hacking and Security Domains
- Information Security Principles and CIA Triad
- Hacker Types, Phases, and Methodologies
- Legal and Ethical Aspects of Hacking
- Security Threats, Attacks, and Countermeasures
- Lab Setup for Ethical Hacking Practices
- Network Architecture and Protocols
- Footprinting and Reconnaissance Methods
- Scanning Networks for Open Ports and Services
- Network Mapping Tools and Techniques
- Banner Grabbing and OS Fingerprinting
- Password Cracking and User Account Exploitation
- Privilege Escalation Techniques
- Keylogging and Rootkit Deployment
- System Vulnerability Exploitation
- Understanding Web Architecture and HTTP
- SQL Injection and Cross-Site Scripting (XSS)
- Cross-Site Request Forgery (CSRF) and Insecure Direct Object Reference
- File Inclusion and Session Hijacking
- Web Server Security Configuration
- Web Application Firewalls and Testing
- Introduction to Malware and Its Types
- Creating and Analyzing Trojans
- Detecting and Removing Worms and Viruses
- Backdoor Creation and Countermeasures
- Sandbox Analysis and Reverse Engineering Basics
- Wireless Network Standards and Encryption
- WEP/WPA/WPA2 Cracking Techniques
- Wireless Sniffing and Packet Analysis
- Rogue Access Points and Evil Twin Attacks
- Psychological Principles of Manipulation
- Phishing, Vishing, and Pretexting Techniques
- Baiting and Tailgating Attacks
- Social Engineering Toolkit (SET) Usage
- Building Awareness and Employee Training
- Prevention and Defense Strategies
- Cloud Infrastructure and Vulnerabilities
- Cloud Hacking Tools and Techniques
- IoT Device Exploitation and Hardening
- Security in Smart Devices and Sensors
- Cloud Data Encryption and Identity Management
- Penetration Testing Lifecycle and Methodology
- Vulnerability Assessment Tools
- Exploit Development and Payload Delivery
- Red Team vs Blue Team Exercises
Ethical Hacking Training Projects
Become a Ethical Hacking Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Password Strength Checker
This beginner project helps learners understand the importance of strong passwords. Students develop scripts that evaluate password complexity and security. It introduces basic programming logic and string manipulation techniques. Learners explore common vulnerabilities like weak passwords. The project emphasizes preventive security practices. It builds a foundation for more advanced ethical hacking concepts.
Basic Network Scanning
Students perform simple network scans to identify active devices and open ports. This project teaches the use of tools like Nmap and Netcat. Learners understand IP addressing, subnets, and network topology. The project introduces reconnaissance techniques used in penetration testing. Students gain hands-on experience in mapping network vulnerabilities. It sets the stage for advanced network security testing.
Simple Web Application Vulnerability Testing
Learners analyze a demo web application to identify common security issues. The project introduces SQL injection, XSS, and form input vulnerabilities. Students practice safe testing techniques in controlled environments. The project teaches how hackers exploit weak inputs. It emphasizes ethical responsibility and documentation. Learners develop critical thinking skills for vulnerability detection.
Advanced Penetration Testing Lab
This project involves setting up a virtual lab to simulate real-world network attacks. Students perform vulnerability assessments on multiple devices and servers. They use tools like Metasploit and Wireshark to detect weaknesses. The project emphasizes systematic testing and reporting. Learners gain experience in ethical exploitation and mitigation strategies. It builds confidence in handling enterprise-level security scenarios.
Wireless Network Hacking Simulation
Students explore security testing on Wi-Fi networks in a controlled lab. They learn about encryption types like WEP, WPA, and WPA2. The project demonstrates password cracking, network sniffing, and packet analysis. Learners understand securing wireless networks against attacks. The project highlights real-world vulnerabilities in wireless communications. It prepares learners for mobile and IoT security tasks.
Social Engineering Attack Simulation
This intermediate project focuses on testing human vulnerabilities in security. Students simulate phishing emails, pretexting, and other social engineering tactics. They learn to analyze human behavior and susceptibility. The project emphasizes the importance of training and awareness programs. Learners also explore ethical considerations and compliance requirements. It strengthens overall organizational security strategy knowledge.
Advanced Exploit Development
Learners develop proof-of-concept exploits to identify zero-day vulnerabilities. The project teaches reverse engineering, binary analysis, and memory exploitation. Students work in controlled environments to understand complex attack vectors. It emphasizes secure coding and prevention strategies. Learners gain hands-on skills in vulnerability discovery. The project prepares students for advanced penetration testing roles.
Web Application Security Testing with Burp Suite
This advanced project involves performing end-to-end security testing on complex web applications. Students use Burp Suite to intercept requests, analyze responses, and identify vulnerabilities. The project teaches advanced techniques like session hijacking, CSRF, and server misconfigurations. Learners understand detailed reporting and mitigation strategies. It enhances skills in enterprise web security assessment.
Network Defense and Incident Response
Students learn to detect, analyze, and respond to network intrusions in real time. The project involves configuring IDS/IPS systems, firewalls, and SIEM tools. Learners simulate attacks and implement containment strategies. The project emphasizes threat intelligence and proactive defense. It prepares learners for security operations and incident response roles. Advanced monitoring and reporting techniques are highlighted.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Ethical HackingOverview
Reasons to Consider Enrolling in Ethical Hacking Training in Anna Nagar
Enrolling in Ethical Hacking Training equips learners with the knowledge and tools to secure digital environments. The course covers penetration testing, vulnerability assessment, and cyber threat analysis. Students gain hands-on experience using industry-standard tools and techniques. Training emphasizes ethical practices, compliance, and real-world security scenarios. Learners develop problem-solving and analytical skills crucial for cybersecurity roles. The program is designed by experienced ethical hackers and security professionals. Placement guidance and project mentorship are provided. Completing this training prepares learners for challenging and rewarding careers in cybersecurity.
Techniques and Trends Observed in Ethical Hacking Course in Anna Nagar
- Penetration Testing Methodologies : Learners follow structured frameworks to identify and exploit vulnerabilities. This approach ensures systematic assessment and reporting. It builds expertise in ethical hacking and compliance.
- Red Team vs Blue Team Exercises : Students experience attack (Red) and defense (Blue) scenarios. These exercises improve practical understanding of offensive and defensive techniques. They prepare learners for real-world cybersecurity challenges.
- Advanced Threat Intelligence : Training emphasizes monitoring emerging threats and zero-day vulnerabilities. Learners gain skills to analyze malware and network anomalies. This trend helps organizations proactively mitigate risks.
- Cloud Security Testing : Ethical hacking now extends to cloud environments and virtualized infrastructure. Learners explore securing AWS, Azure, and other platforms. It ensures protection of modern enterprise data assets.
- IoT and Mobile Security : Courses include testing Internet of Things and mobile devices. Students learn to identify vulnerabilities in connected devices and mobile applications. This trend addresses the growing need for end-to-end digital security.
Overview of the Most Recent Ethical Hacking Tools
Modern ethical hacking tools enhance security assessment and threat detection. Nmap is widely used for network scanning and reconnaissance. Wireshark helps in monitoring network traffic and analyzing packets. Metasploit provides a framework for exploit development and penetration testing. Burp Suite enables comprehensive web application security testing. John the Ripper and Hashcat are used for password cracking exercises. Nessus and OpenVAS provide vulnerability scanning and reporting features. Kali Linux offers a complete suite of ethical hacking and security tools. These tools collectively support thorough testing, analysis, and mitigation strategies in cybersecurity.
Requirements Needed for Ethical Hacking Certification in Anna Nagar
- Basic Computer and Networking Knowledge : Understanding of TCP/IP, DNS, and OSI model is essential. It helps in network mapping, scanning, and threat analysis.
- Familiarity with Operating Systems : Knowledge of Linux and Windows operating systems is required. Learners can execute commands, manage services, and analyze system logs effectively.
- Programming Skills : Basic scripting knowledge in Python, Bash, or JavaScript enhances exploit creation and automation. It improves analytical and problem-solving capabilities.
- Analytical and Logical Thinking : Learners must identify patterns, trace vulnerabilities, and propose solutions. Strong reasoning skills ensure accuracy in penetration testing.
- Interest in Cybersecurity and Ethical Practices : A curious and responsible mindset drives deeper learning and ethical adherence. Learners gain practical exposure while respecting legal boundaries.
Goals Achieved Through Ethical Hacking Placement in Anna Nagar and Potential Career Paths
Through Ethical Hacking Training, learners acquire the ability to identify, exploit, and mitigate cybersecurity threats. The course develops expertise in penetration testing, vulnerability assessment, and network security. Students gain practical experience using the latest tools and techniques in ethical hacking. They learn to implement security policies, conduct audits, and respond to incidents effectively. The training enhances analytical, problem-solving, and technical skills. Graduates become equipped to secure web applications, networks, and cloud environments. The program opens career opportunities in cybersecurity, consulting, and IT security operations. Completing the course positions learners as professional ethical hackers in the industry.
Career Opportunities After Ethical Hacking Training
Ethical Hacker / Penetration Tester
Ethical Hackers assess systems for vulnerabilities and exploit weaknesses in a controlled manner. They prepare detailed reports and recommend mitigations. The role requires knowledge of hacking tools and security frameworks. It is essential for proactive organizational defense.
Cybersecurity Analyst
Analysts monitor networks and systems to detect and respond to security incidents. They analyze threats, logs, and alerts for potential breaches. The role emphasizes risk assessment and mitigation strategies. Cybersecurity Analysts are crucial for maintaining enterprise security.
Security Consultant
Security Consultants advise organizations on protecting digital assets. They perform assessments, implement security policies, and recommend improvements. The role requires expertise across networks, applications, and compliance standards.
Network Security Engineer
Engineers design and maintain secure network infrastructure. They configure firewalls, VPNs, and intrusion detection systems. The role emphasizes threat prevention, monitoring, and response. Network Security Engineers are vital for enterprise defense. Their expertise ensures business continuity.
Incident Response Specialist
Specialists investigate, contain, and remediate security breaches. They implement strategies to minimize downtime and data loss. The role requires analytical and technical skills for quick response. It is critical in cybersecurity operations centers (SOC).
Malware Analyst / Reverse Engineer
Malware Analysts dissect malicious software to understand its behavior and origin. They develop countermeasures and report findings. The role requires reverse engineering, coding, and forensic expertise. Analysts protect organizations from emerging digital threats
Skill to Master
Network Scanning
Vulnerability Assessment
Penetration Testing
System Hacking
Web Application Security
Malware Analysis
Wireless Network Hacking
Social Engineering
Incident Response
Cloud and IoT Security
Cyber Threat Intelligence
Ethical Hacking Reporting
Tools to Master
Kali Linux
Metasploit Framework
Burp Suite
Wireshark
Nmap
Aircrack-ng
Nessus
OWASP ZAP
Hydra
John the Ripper
Maltego
Shodan
Learn from certified professionals who are currently working.

Training by
Vikram S, having 12+ yrs of experience
Specialized in: Network Security, Penetration Testing, and Cyber Defense Solutions.
Note: Vikram S. is known for his practical teaching approach and his ability to simplify complex hacking techniques into real-world cybersecurity practices.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Ethical HackingCertification

Enhances cybersecurity knowledge and hands-on penetration testing skills. Provides career opportunities in high-demand cybersecurity roles. Offers exposure to the latest hacking tools and techniques.
You gain real-world exposure to security analysis, ethical hacking simulations, and certification support that improves your professional credibility.
While certification strengthens your resume, job placement depends on your technical proficiency and project performance. The course prepares you for interviews and portfolio building.
Basic knowledge of networking, operating systems, and programming is recommended. Familiarity with cybersecurity concepts helps during assessments.
- Practice with penetration testing tools.
- Complete mock tests and sample projects.
- Review case studies on real-world attacks.
Yes, exams are available locally through authorized centers and online platforms. The assessment includes theoretical and practical components.
- Willingness to engage in real-time lab exercises.
- Interest in cybersecurity and forensics.
- Familiarity with operating systems.
Absolutely. With the growing need for cybersecurity experts, Ethical Hacking certification opens global career opportunities, enhancing job readiness and long-term professional growth.
Frequently Asked Questions
- No prior experience is needed; beginners can start with networking basics before moving to penetration testing.
- Ethical hacking
- Vulnerability testing
- Malware analysis
- Security defense
- Students complete practical projects.
- Build technical documentation.
- Receive mentorship for showcasing cybersecurity achievements.
- Yes, a recognized Ethical Hacking certification is provided upon completing all modules and projects.
- Yes, ethical hackers are in demand across industries such as IT, finance, telecom, and government for securing systems and networks.
)



