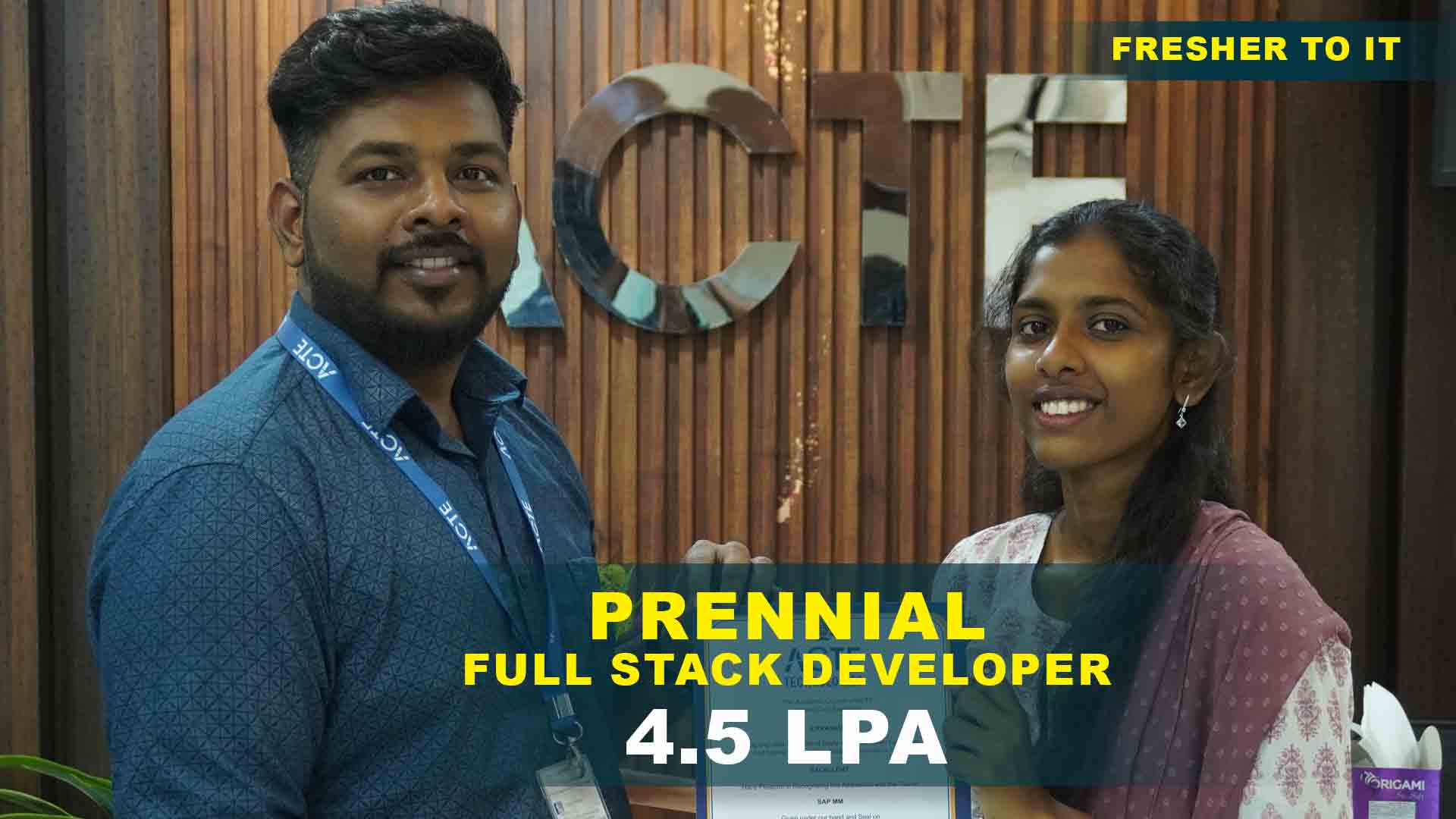
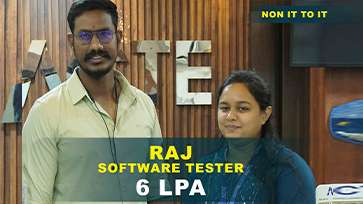
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculam Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
Ethical Hacking Training Projects
Become a Ethical Hacking Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Basic Network Scanning
Use tools like Nmap to perform network scans and identify active devices, open ports, and services on a local network.
Password Cracking
Implement a simple password-cracking script using tools like John the Ripper or Hashcat to understand how hashing algorithms and password strength work.
Vulnerability Scanning
Set up a vulnerability scanner like OpenVAS to identify common vulnerabilities on a test system or virtual machine.
Web Application Penetration Testing
Conduct a penetration test on a web application using tools like Burp Suite or OWASP ZAP to find and exploit common vulnerabilities such as XSS, CSRF, and directory traversal.
Network Sniffing and Analysis
Use Wireshark to capture and analyze network traffic, identifying potential security issues or unusual patterns in a test network.
Creating a Vulnerable VM for Testing
Set up a vulnerable virtual machine using tools like Metasploitable to practice various exploitation techniques and security assessments.
Advanced Penetration Testing
Perform a comprehensive penetration test on a real-world application or network environment, including enumeration, exploitation, and post-exploitation phases.
Exploit Development
Develop and test your exploits for known vulnerabilities, creating proof-of-concept code to understand the intricacies of exploit development and the security implications.
Advanced Malware Analysis
Analyze complex malware samples using tools like IDA Pro or Ghidra. Reverse engineer the malware to understand its behavior, communication, and impact.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Ethical Hacking Training Overview
Ethical Hacking Programmer’s Potential Career Paths
A programmer skilled in ethical hacking can work in a variety of fulfilling professions, such as penetration testing (finding and taking advantage of security flaws in systems to improve protection), security analysis (keeping an eye out for and combating cyberattacks), incident response (handling and minimizing security breaches), and security consulting (advising companies on the best ways to safeguard their information assets). Professional roles include Chief Information Security Officer (CISO), in charge of the entire security policy and strategy, and Security Architect, in charge of creating robust security infrastructure designs. These roles use their experience in risk management, threat analysis, and vulnerability evaluation to safeguard businesses from cyberattacks.
What Are the Requirements for an Ethical Hacking Training?
- Basic IT Knowledge: Understanding fundamental IT concepts, including networking, operating systems (especially Linux and Windows), and common protocols.
- Familiarity with Programming: Basic knowledge of programming or scripting languages such as Python, JavaScript, or Bash can be beneficial.
- Networking Skills: Understanding network fundamentals, including TCP/IP, DNS, and firewalls, is crucial for identifying and exploiting network vulnerabilities.
- Cybersecurity Fundamentals: Knowledge of basic cybersecurity principles and concepts, such as encryption and authentication, is helpful.
Reasons to Consider Enrolling in Ethical Hacking Training
Your ability to recognize and fix security flaws will increase with enrollment in an ethical hacking training, which will benefit any company that deals with cybersecurity issues. It provides practical expertise with the newest instruments and methodologies to safeguard systems from cyberattacks. In addition, the course can improve your chances of landing a job in cybersecurity, which is in great demand, and help you remain ahead of the curve in a subject that is changing quickly by offering you credentials validating your knowledge.
Techniques and Trends in Ethical Hacking Development
- Penetration Testing: Simulating attacks to find and fix vulnerabilities in systems, networks, and applications before malicious hackers can exploit them.
- Social Engineering: Testing human factors and organizational policies to assess employees' susceptibility to phishing and other deceptive tactics.
- AI and Machine Learning: Leveraging AI-driven tools for threat detection, automated vulnerability scanning, and advanced analytics to identify complex attack patterns.
- Cloud Security: Addressing cloud computing environments' unique challenges and vulnerabilities, including misconfigurations and data breaches.
The Most Recent Ethical Hacking Tools
These are some of the most recent ethical hacking tools: Nmap, which has been updated with improved scanning capabilities for network discovery and vulnerability assessment; Cobalt Strike, a tool for advanced threat emulation and red teaming with improved command and control features; Shodan, a search engine for locating internet-connected devices and evaluating their security; and Burp Suite, a comprehensive platform for web application security testing with advanced features for vulnerability scanning and exploitation.
Career Opportunities After Ethical Hacking
Penetration Tester
Penetration testers, also known as ethical hackers, simulate cyberattacks on systems, networks, and apps to find vulnerabilities.
Security Analyst
An analyst of security systems and data monitors potential risks and breaches and responds accordingly by monitoring.
Security Consultant
A security consultant advises firms on using best practices to safeguard information systems from cyber-attacks.
Incident Responder
An incident responder must manage and mitigate cyberattacks, reducing security incidents like data breaches.
Ethical Hacker (Red Team Specialist)
Someone who initiates a cyberattack to find and exploit security flaws in a company’s networks and systems.
Vulnerability Assessor
An organization can find security flaws and threats by having a vulnerability manager evaluate its systems.
Skill to Master
Penetration Testing
Vulnerability Assessment
Network Security
Social Engineering
Incident Response
Malware Analysis
Cryptography
Web Application Security
Ethical Hacking Tools
Forensic Analysis
Risk Management
Security Policies and Procedures
Tools to Master
Nmap
Metasploit Framework
Burp Suite
Wireshark
John the Ripper
Nessus
Aircrack-ng
Kali Linux
OWASP ZAP (Zed Attack Proxy)
Netcat
Hydra
Cobalt Strike
Learn from certified professionals who are currently working.

Training by
Arun , having 12 yrs of experience
Specialized in: Network Penetration Testing, Web Application Security, Social Engineering, and Vulnerability Assessment.
Note: Arun is a seasoned, ethical hacker and security consultant with extensive experience identifying and mitigating security vulnerabilities. His hands-on approach and deep knowledge of tools like Metasploit and Burp Suite make him an excellent resource for students seeking practical, real-world hacking skills and security strategies.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Ethical Hacking Certification

You can drastically improve your career prospects in cybersecurity by gaining a reputation in the industry, expanding your earning potential, and finding various job options by obtaining an ethical hacking certification. Along with keeping you informed about the newest security developments, it gives you the fundamental skills you need for penetration testing and vulnerability assessment.
Although obtaining an Ethical Hacking certification can help you land a job and showcase your abilities to prospective employers, it is not a guarantee. Because the cybersecurity industry is competitive, recruiting decisions frequently consider several criteria, such as experience, transferable abilities, and cultural fit.
Exam requirements for Ethical Hacking certifications can change based on the particular certification. A basic familiarity with operating systems, networking, and fundamental security concepts is often advised. Some certificates, such as CompTIA Security+, may require relevant job experience in cybersecurity or IT or previous certifications.
Yes, you can take many of the certification examinations for ethical hacking online, which gives you flexibility and convenience. Several certification providers, such as EC-Council and CompTIA, offer remote proctoring services, which let you take the exam from home or another secure place.
Although it’s not always necessary, having real-world experience might help you grasp the material and do better on the test for an Ethical Hacking certification. To fully comprehend the subject matter, many certifications require you to have some degree of real-world IT or cybersecurity experience.
Obtaining the ACTE Ethical Hacking Certification might be well worth your time and money if you want to advance your reputation and understanding of cybersecurity. In-depth instruction, practical training, and exposure to real-world scenarios are typically provided, all of which can benefit your professional development.
Frequently Asked Questions
- Classroom Training
- Online Live Training
- Self-Paced eLearning
- Blended Learning
- On-Demand Training
- Corporate Training
- You can make up a missed class by watching video lectures or using the course materials online. The majority of programs provide tools to assist you in staying on course, like lecture notes, videos that have been recorded, and additional materials. If you have questions or need clarification, you can also contact your teacher or fellow students.
- If you have any more questions, you should use the email address or contact form that the school has supplied to contact the support staff or course coordinator. They can answer particular queries, give you in-depth information, and advise you on any worries you might have. Many applications also provide live chat or phone support, so you may obtain the information you need right away.
- Visit the ACTE Website
- Search for the Course
- Select the Course
- Register Online
- Contact ACTE
- Receive Confirmation
- Indeed, lecture notes, session recordings, and supplemental materials are typically available online. You can locate and examine all pertinent materials at your convenience on most courses' digital platforms or learning management systems (LMS). This allows you to study whenever it's convenient and review the material again if necessary.
)



