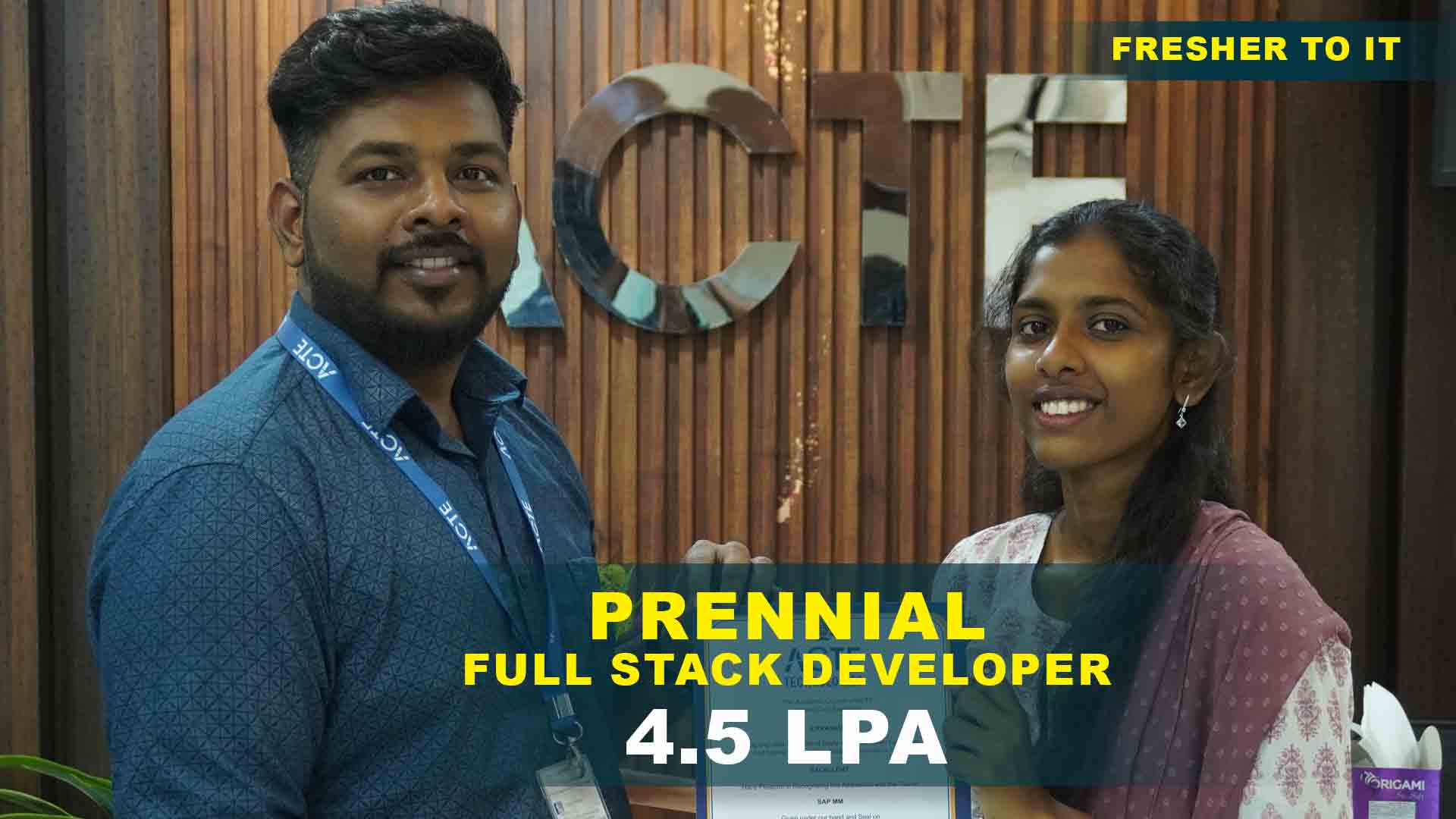
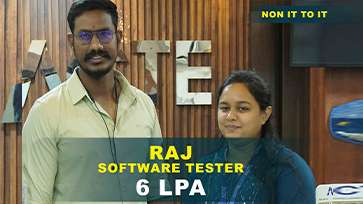
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculam Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
CyberArk Training Projects
Become a CyberArk Expert With Practical and Real-Time Privileged Access Management Projects.
- Practice Core PAM Tools & Vault Configuration
- Designed by Industry Security Experts
- Gain Real-World Enterprise Implementation Experience
Privileged Account Onboarding
Learn how to onboard Windows, Linux, and database accounts into CyberArk Vault. Configure platforms and policies for secure password. Understand Safe creation and access control.
Password Policy & Rotation
Configure password complexity rules and automatic rotation policies. Implement reconciliation accounts and exclusive access controls. Manage service accounts securely.
Privileged Session Management
Configure PSM for RDP and SSH connections. Enable session monitoring and recording. Understand session isolation and live termination. Generate audit logs and compliance reports.
Application Access Manager Integration
Integrate CyberArk with enterprise applications. Configure Credential Provider and REST API access. Secure application-to-database credentials. Implement DevOps secrets management practices.
CyberArk Privilege Cloud Deployment
Understand Privilege Cloud architecture and deployment model. Integrate with AWS and Azure environments. Secure hybrid infrastructures. Apply cloud-based privileged access best practices.
Access Workflow & Dual Control
Configure access request and approval workflows. Implement dual control mechanisms. Assign Safe permissions and role-based access. Monitor user activity and generate compliance.
High Availability & Disaster Recovery
Configure Vault HA and Disaster Recovery setup. Perform backup and restore procedures. Understand replication and failover strategies. Apply security hardening techniques for enterprise.
Zero Trust & MFA Integration
Implement Zero Trust access strategies. Integrate Multi-Factor Authentication (MFA). Connect with LDAP and Active Directory. Strengthen enterprise identity and privileged access security.
End-to-End PAM Implementation Project
Design and deploy a complete CyberArk infrastructure. Onboard accounts, configure policies, and secure sessions. Integrate with cloud and on-prem systems.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

CyberArk Training in Trichy Overview
Benefits gained from CyberArk Training in Trichy
CyberArk Course in Trichy helps learners master Privileged Access Management (PAM) concepts through real-time enterprise projects. Students gain hands-on experience in managing privileged accounts, configuring Safes, implementing password rotation policies, and securing remote sessions using PSM. The training covers Vault configuration, Privilege Cloud deployment, and integration with Active Directory and cloud platforms like AWS and Azure. Learners also implement access control workflows and compliance monitoring to protect critical IT infrastructure. Practical exposure ensures candidates can secure enterprise environments, prevent insider threats, and meet regulatory standards effectively.
Emerging future trends in CyberArk Certification in Trichy
- Zero Trust Security Model : Implements strict identity verification and least-privilege access.Enhances enterprise security posture against insider and external threats.
- Cloud Privileged Access Management : Secures cloud workloads and hybrid environments.Supports Privilege Cloud deployments and SaaS-based PAM solutions.
- DevSecOps & Secrets Management : Integrates CyberArk with CI/CD pipelines and container platforms.Protects application credentials and API secrets.
- Advanced Threat Analytics : Monitors privileged sessions and detects anomalous behavior.Enables proactive security risk mitigation.Provides real-time alerts and detailed audit reports to strengthen compliance.
- Compliance & Audit Automation : Generates automated reports for SOX, PCI-DSS, and GDPR.Helps organizations maintain regulatory compliance efficiently.
Latest advancements in CyberArk course in Trichy
Modern CyberArk Training with Placement focus on advanced Vault configuration, platform customization, Privileged Session Management (PSM), and Application Access Manager (AAM). Learners explore Privilege Cloud architecture, REST API integration, and high availability deployment models. The curriculum includes disaster recovery planning, security hardening, performance tuning, and enterprise-level implementation strategies. Real-time labs simulate production environments for hands-on learning. Certification-oriented guidance prepares candidates for CyberArk Administrator and PAM Engineer roles.
Main concepts behind CyberArk Placement in Trichy
- Vault & Safe Management Mastery Learn to configure Safes, platforms, and policies.Practice enterprise-level privileged account onboarding.Gain hands-on experience in access control management.
- Password & Session Management Implement automated password rotation and session recording.Work on real-time PSM and CPM configuration scenarios.
- Cloud & Hybrid Security Integration Integrate CyberArk with AWS, Azure, and Active Directory.Configure secure privileged access for hybrid infrastructures.
- Security & Compliance Implementation Enforce access control policies and audit logging.Prepare compliance-ready security reporting.. Implement risk-based authentication and continuous monitoring.
- Enterprise Deployment & Troubleshooting Deploy high availability and disaster recovery setups.Gain hands-on experience in resolving real-time enterprise issues.
Real-time projects completed recently in CyberArk Certification Course
CyberArk Placement in Trichy prepares learners for roles such as CyberArk Administrator, PAM Engineer, Security Engineer, and Cloud Security Specialist. Professionals gain expertise in implementing privileged access workflows, securing administrative accounts, managing session monitoring, and deploying Privilege Cloud solutions. The course enables candidates to work in IT services, banking, healthcare, and enterprise organizations requiring strong access control mechanisms. With comprehensive hands-on practice and project exposure, learners become industry-ready to manage enterprise-grade privileged access environments effectively.
Career Opportunities After Cyberark Training
CyberArk Administrator
Manages CyberArk Vault, Safes, and platform configurations. Responsible for onboarding privileged accounts, configuring password policies, and maintaining system health. Ensures secure privileged access.
Privileged Access Management (PAM) Engineer
Implements and supports CyberArk solutions including PSM, CPM, and Privilege Cloud. Integrates CyberArk with Active Directory, cloud platforms, and enterprise applications to secure privileged credentials.
CyberArk Implementation Specialist
Deploys and configures CyberArk infrastructure in enterprise environments. Handles Vault installation, DR setup, high availability configuration, and security hardening based on compliance standards.
Application Security Engineer (AAM)
Integrates CyberArk Application Access Manager (AAM) with enterprise applications. Secures secrets for DevOps pipelines, APIs, and containerized environments. Implements REST API.
Cloud Security Engineer
Manages CyberArk Privilege Cloud deployments. Secures AWS and Azure privileged accounts. Implements cloud-based PAM strategies aligned with Zero Trust principles.Ensures continuous monitoring.
CyberArk Support Engineer
Provides operational support for CyberArk components. Troubleshoots password rotation, session management, and access control issues. Monitors logs and ensures compliance reporting.
Skill to Master
Privileged Account Onboarding
Safe & Access Management
Password Policy Configuration
CPM & PSM Configuration
Session Monitoring & Recording
Application Access Manager (AAM)
Privilege Cloud Deployment
LDAP & Active Directory Integration
Disaster Recovery & High Availability
Vault Backup & Restore
Security Hardening & Compliance
Zero Trust & MFA Integration
Tools to Master
Digital Vault
PVWA (Privileged Vault Web Access)
Central Policy Manager (CPM)
Privileged Session Manager (PSM)
Application Access Manager (AAM)
Credential Provider (CP)
Conjur Secrets Manager
Privilege Cloud
PrivateArk Client
Password Upload Utility (PUU)
REST API Integration
PTA (Privileged Threat Analytics)
Learn from certified professionals who are currently working.

Training by
Ram, having 12+ yrs of experience
Specialized in: CyberArk Privileged Access Management (PAM), Password Vault, PSM, CPM, Privilege Cloud, and DevSecOps Integration.
Note: Ram is highly experienced in implementing and managing enterprise-level CyberArk solutions. He specializes in securing privileged accounts, configuring vault policies, automating password rotation, and integrating CyberArk with cloud and on-premise infrastructures to enhance organizational security and compliance.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

CyberarkCertification

Yes, you will receive industry-recognized CyberArk certification Course guidance upon successful completion. With rising cybersecurity threats and strict compliance requirements.
CyberArk professionals earn competitive salaries depending on experience and certification level. PAM Engineers and Security Specialists are highly valued in both Indian and global markets.
CyberArk is one of the leading PAM solutions used by global enterprises. With structured training and real-time lab practice, learners can confidently deploy, manage, and troubleshoot.
Frequently Asked Questions
- Yes, we offer classroom training, online instructor-led sessions, and corporate training for CyberArk.
- The CyberArk course duration typically ranges from 4 to 6 weeks.
- Includes hands-on labs, real-time enterprise projects, and certification-focused preparation.
- We provide placement assistance including resume preparation, mock interviews, and job referrals.
- Yes, students work on real-time projects such as privileged account onboarding, password rotation automation, session monitoring configuration.
- Yes, interview preparation sessions are included as part of the training.We conduct mock interviews, provide real-time scenario-based questions.
)



