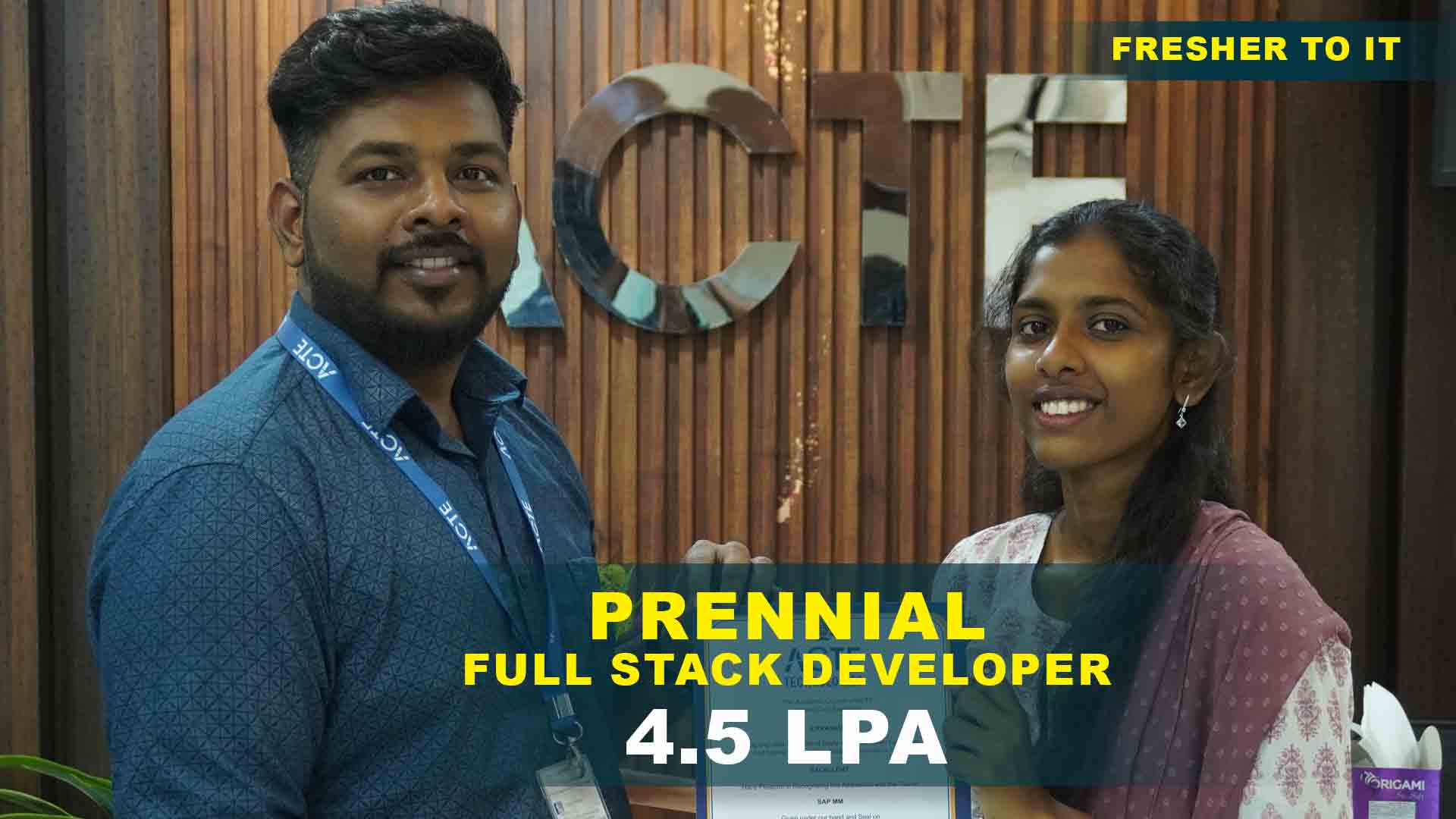
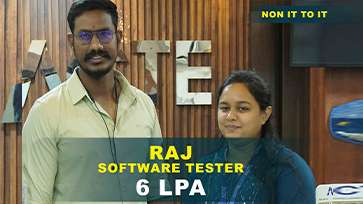
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculam Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
- Overview of CyberArk solutions and industry need
- Understanding Privileged Access Management (PAM) concepts
- Types of privileged accounts and security challenges
- CyberArk architecture components and deployment models
- Key features and capabilities of CyberArk Vault
- Use cases in modern enterprise environments
- Digital Vault architecture and installation process
- Understanding Password Vault Web Access (PVWA)
- Central Policy Manager (CPM) operations
- Privileged Session Manager (PSM) fundamentals
- SSH key management and secure credential rotation
- Privileged account discovery and mapping
- Password management & automated rotation policies
- Session recording and secure monitoring
- RDP, SSH, and database connection management
- User authentication & role-based access configuration
- Dual-control & workflow processes
- LDAP, RADIUS & MFA integration
- Privileged sessions control & secure tunneling
- Access auditing and reporting practices
- Backup and vault maintenance
- Advanced PSM configurations and plug-ins
- Privileged session troubleshooting & optimization
- Application identity management basics (AIM)
- REST API & automated integration
- Deploying CyberArk Browser Extension & plugins
- Introduction to CyberArk in hybrid and cloud environments
- Integrating CyberArk with AWS, Azure & GCP
- Secrets Manager and credential injection
- DevOps tool integration (Docker, Kubernetes, Jenkins)
- Monitoring CyberArk logs and audit tools
- Performance tracking and resource optimization
- Incident detection & troubleshooting strategies
- SIEM integration for centralized security monitoring
- Security standards & risk-based access control
- PAM migration strategy
- Upgrades & version management best practices
- Integrating legacy systems with CyberArk
- Multi-environment deployment and scaling
- Enterprise PAM deployment end-to-end
- Identity & access security framework creation
- CyberArk–SIEM integration & monitoring
- Automated credential lifecycle system
- Application authentication with AIM
CyberArk Training Projects
Become a Apache Spark Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Introduction to Privileged Access
Identify privileged accounts and understand their significance. Set up basic access policies in a controlled lab environment.
Password Vault Setup
Configure CyberArk Vault for storing and managing credentials securely. Learn access controls and basic management operations.
Basic Account Monitoring
Monitor privileged account activity using CyberArk tools. Generate simple audit reports to ensure compliance.
Privileged Account Automation
Automate password rotation and account management tasks. Implement scheduled updates for selected privileged accounts.
Session Monitoring & Recording
Configure session recording for privileged user activities. Analyze recordings to detect policy violations or unusual actions.
Access Control Policy Implementation
Define and enforce access policies for different roles and departments. Test policies to ensure proper segregation of duties.
CyberArk Integration Project
Integrate CyberArk with enterprise applications and services. Ensure secure communication and credential management across platforms.
Threat Detection & Incident Simulation
Simulate potential insider threats and misuse of privileged accounts. Implement alerts and response strategies to mitigate risks.
Capstone Privileged Account Security Project
Combine vault setup, automation, monitoring, and policy enforcement. Demonstrate end-to-end CyberArk management and security best practices.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

CyberArk Overview
Benefits gained from CyberArk Training in Maraimalai Nagar
- Master Privileged Access Management (PAM): Learn to secure and manage privileged accounts across enterprise systems. Protect critical assets and reduce the risk of insider threats effectively.
- Hands-On Lab Experience: Gain practical skills by configuring, monitoring, and auditing CyberArk solutions. Simulate real-world scenarios to manage privileged credentials securely.
- Industry-Recognized Certification: CyberArk certification validates expertise in PAM and enterprise security. Enhances employability and credibility with organizations worldwide.
- Enhanced Security Knowledge: Understand password vaulting, session management, and access control policies. Develop skills to prevent unauthorized access and maintain compliance standards.
- Integration with Enterprise Systems: Learn to integrate CyberArk with Active Directory, cloud platforms, and applications. Ensure consistent security policies across hybrid and on-premise environments.
- Risk Mitigation and Compliance: Gain knowledge of regulatory frameworks like GDPR, HIPAA, and ISO 27001. Learn strategies to maintain audit readiness and enforce cybersecurity policies.
Latest Advancements in CyberArk Certification in Maraimalai Nagar
CyberArk training now includes advanced Privileged Access Management (PAM) solutions integrated with AI-driven identity analytics. Modern modules focus on securing privileged access across hybrid and multi-cloud infrastructures. Automated password rotation, session recording, and real-time monitoring have been enhanced with intelligent threat prediction. CyberArk Privilege Cloud and Secure Cloud Access are included for cloud-native identity protection. Training highlights Just-In-Time (JIT) access models for reducing attack surface and credential exposure. Hands-on labs cover advanced integrations with DevOps pipelines, APIs, and secrets management tools.
Emerging Future Trends in CyberArk Course in Maraimalai Nagar
- Cloud Privileged Access Management: Secure privileged accounts in cloud and hybrid environments using CyberArk. Enable enterprises to control access and monitor privileged activity remotely.
- AI-Driven Threat Detection: Integration of AI for detecting unusual privileged account activities. Helps proactively identify insider threats and potential breaches.
- Automation in Credential Management: Automate password rotations, access approvals, and session monitoring. Reduces manual errors and strengthens overall security posture efficiently.
- DevSecOps Integration: Embed CyberArk within DevOps pipelines for secure automation workflows. Protect secrets, API keys, and credentials in continuous delivery environments.
- Privileged Access Analytics: Leverage analytics to track usage patterns and identify suspicious activities. Supports risk-based decision-making and improves governance across systems.
Main Concepts Behind CyberArk Training in Maraimalai Nagar
CyberArk training focuses on securing and managing privileged accounts across enterprise IT environments. Core concepts include password vaulting, credential rotation, and secure session management. Learners understand privilege escalation risks, access governance, and least-privilege enforcement. Training covers configuration of CyberArk components such as PVWA, CPM, PSM, and Vault Server. Students learn to monitor privileged sessions, generate audit reports, and enforce compliance policies. It prepares professionals to implement Privileged Access Management (PAM) strategies in real enterprise systems.
Real-Time Projects Completed Recently in CyberArk Placement in Maraimalai Nagar
Recent projects include implementing CyberArk Enterprise Password Vault for secure storage of privileged credentials. Students configured and deployed Privileged Session Manager (PSM) to monitor and record high-risk access activities. Hands-on projects involved automated password rotation and policy configuration for critical enterprise accounts. Learners integrated CyberArk with Active Directory and cloud platforms to secure multi-domain access. Simulation tasks included securing third-party vendor access and privileged remote session workflows. End-to-end PAM deployment projects demonstrated compliance reporting, auditing, and risk-based access control.
Career Opportunities After CyberArk Training
CyberArk Administrator
Manage privileged accounts, configure policies, and monitor sessions. Ensure enterprise assets remain secure from insider and external threats.
Privileged Access Consultant
Advise organizations on implementing CyberArk solutions effectively. Assist in designing policies and maintaining compliance with regulations.
Security Engineer (PAM Focus)
Implement and maintain enterprise privileged access controls. Integrate PAM solutions with cloud and on-premise applications securely.
Identity and Access Management (IAM) Specialist
Focus on user authentication, authorization, and identity lifecycle management.
DevSecOps Engineer
Embed security into CI/CD pipelines and DevOps workflows. Protect secrets, credentials, and infrastructure throughout development cycles.
Compliance and Risk Analyst
Monitor privileged account usage for regulatory compliance and risk mitigation. Generate audit reports and ensure enterprise security policies.
Skills To Master
Identity & Access Management (IAM)
Privileged Access Security
CyberArk Vault Administration
Password & Session Management
Security Policy Implementation
Compliance & Audit Management
Application & Database Security
Threat Detection & Risk Mitigation
Integration with SIEM Tools
Automation & Scripting (PowerShell, Python)
Cloud Security & Privileged Accounts
Incident Response & Troubleshooting
Tools To Master
CyberArk Privileged Access Security (PAS)
CyberArk Vault
Privileged Session Manager (PSM)
Password Vault Web Access (PVWA)
Central Policy Manager (CPM)
CyberArk Discovery & Audit (DNA)
Threat Analytics Dashboard
SIEM Integration Tools
APIs for Automation
CyberArk Endpoint Privilege Manager
Active Directory Integration
Secure Cloud Connectors
Learn from certified professionals who are currently working.

Training by
Meena, having 13+ yrs of experience
Specialized in: Privileged access management, Vault administration, and enterprise security integrations
Note: Meena is recognized for her expertise in managing privileged accounts, implementing security best practices, and helping learners secure enterprise-level systems confidently.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

CyberArkCertification

- Validates expertise in privileged access management and secure account handling.
- Enhances employability in cybersecurity and identity management roles.
- Demonstrates knowledge in Vault administration and policy enforcement.
Yes, multiple certifications are available depending on the role. Popular certifications include CyberArk Defender, CyberArk Sentry, and CyberArk Trustee.
- CyberArk Administrator
- Privileged Access Security Engineer
- Security Consultant (Identity & Access Management)
- Vault & Session Manager
- Compliance & Audit Specialist
- Enterprise Security Analyst
Yes, pursuing multiple certifications is fully encouraged. Professionals can gain expertise across Vault administration, privileged session management, and enterprise integrations. Multiple certifications enhance career opportunities and show versatility in enterprise security solutions.
- Admin roles managing privileged accounts and Vault infrastructure.
- Security analyst roles monitoring session activity and access events.
- Consultant positions guiding organizations on IAM and privileged access policies.
Yes, many institutes in Coimbatore offer CyberArk training programs with local exam options. Exams may follow global certification standards or be tailored for placement-oriented training.
While prior experience is helpful, it is not mandatory. Training programs include hands-on labs, Vault simulations, and session monitoring exercises. These practical activities prepare learners to confidently handle real-world CyberArk scenarios, helping even beginners secure placements.
- Privileged account security expertise is highly demanded across enterprises.
- Certification improves career growth and credibility.
- Hands-on labs prepare learners for real-time Vault and session management.
- Institutes offer free demo sessions online or in-person.
- You can register on their website or contact the coordinator to experience the course structure and teaching methodology.
- Vault administration
- Privileged access security
- Enterprise identity management
Yes, institutes provide placement support including resume preparation, mock interviews, and access to job portals. Students are connected with companies looking for CyberArk-skilled professionals.
Yes, the course offers recognized certifications that validate your CyberArk skills. These certifications are widely accepted by IT organizations and improve career prospects in identity and access management roles.
Absolutely. The program includes practical labs, Vault configuration exercises, privileged session monitoring workshops, and automation practice. This ensures learners gain real-world experience in enterprise security scenarios.
)



