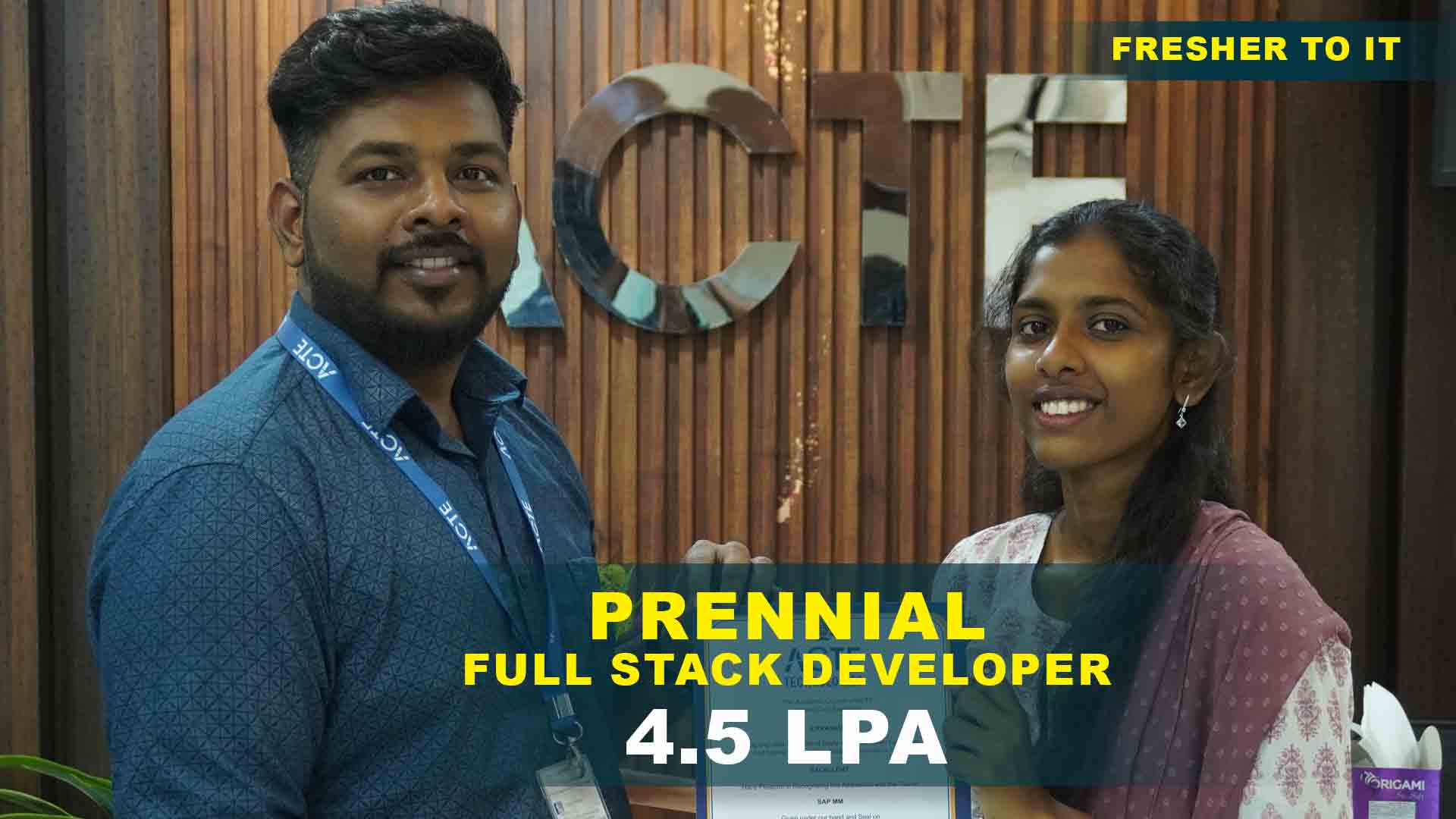
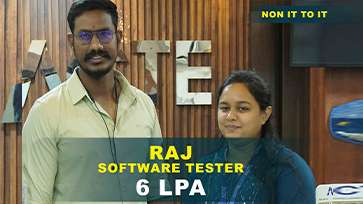
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculum Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
Cyber Security Training Projects
Become a Cyber Security Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Password Strength Checker
Develop a simple tool that evaluates password strength based on length, complexity, and character diversity. This helps users create stronger passwords.
Basic Encryption & Decryption Tool
Create a program that encrypts and decrypts text using simple encryption algorithms like Caesar Cipher or AES encryption for secure communication.
Phishing Awareness Website
Design a website that educates users on common phishing attacks by simulating real-world phishing scenarios and teaching how to identify suspicious.
Intrusion Detection System
Develop a system that monitors network traffic and detects suspicious activities using basic anomaly detection techniques.
Secure Authentication System
Create a multi-factor authentication (MFA) system using passwords, OTPs, or biometric authentication to strengthen user access security.
Malware Analysis Sandbox
Design a secure environment where you can analyze malware behavior, track changes to files, and detect potential threats in a controlled system.
Penetration Testing Framework
Create an automated penetration testing tool that scans web applications and networks for vulnerabilities, similar to Metasploit or Kali Linux tools.
AI-Powered Cyber Threat Detection
Use machine learning algorithms to build a system that detects and classifies cybersecurity threats in real time, improving response time against attacks.
Blockchain-Based Secure Transactions
Implement a blockchain system to provide secure, tamper-proof financial transactions, ensuring data integrity in digital banking.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Cyber Security Training Overview
Cyber Security Training in OMR with Career Paths
A Cyber Security Training Institute in OMR has diverse career opportunities across multiple industries, including IT, finance, healthcare, government, and defense. With increasing cyber threats and data breaches, organizations actively seek cybersecurity professionals to protect sensitive information. Career paths include Ethical Hacker, Security Analyst, Incident Responder, Penetration Tester, Cyber Forensics Expert, and Security Consultant. Advanced roles such as Chief Information Security Officer (CISO) and Cyber Security Architect require expertise in security strategy, risk management, and compliance. The demand for cybersecurity experts is growing, offering high salaries and job stability. Professionals can work in corporate security teams, government agencies, or as independent consultants specializing in cloud security, IoT security, and AI-driven threat analysis.
The Requirements for Cyber Security Certification in OMR
- Technical Knowledge: Understanding of network security, operating systems, and encryption techniques. Familiarity with Linux, Windows, and macOS security configurations.
- Cybersecurity Certifications: Certified Ethical Hackerr (CEH), CompTIA Security+, Certified Information Systems Security Professionalnal (CISSP), Offensive Security Certified Professional (OSCP)
- Hands-on Experience: Practical knowledge of penetration testing, vulnerability assessment, and incident response. Exposure to cybersecurity tools like Wireshark, Metasploit, Nmap, and Burp Suite.
- Analytical and Problem-Solving Skills: Ability to detect, analyze, and mitigate security threats. Understanding of security policies and compliance regulations (GDPR, ISO 27001, HIPAA).
- Ethical Mindset: Adherence to ethical hacking guidelines and responsible disclosure policies. Strong commitment to protecting data privacy and security.
Enrolling in Cyber Security Training in OMR
Cyber Security Placement in OMR is a high-demand field with increasing job opportunities and competitive salaries. As cyber threats evolve, companies across various industries invest in cyber defense measures, making cybersecurity professionals essential. Enrolling in a cybersecurity course gives you access to expert-led training, hands-on labs, and real-world case studies that help build practical skills. The industry offers job flexibility, allowing professionals to work in-office, remotely, or as freelancers and security consultants. Cybersecurity careers also provide continuous learning opportunities, as new vulnerabilities and security technologies emerge regularly. Whether you are a beginner or an IT professional looking to specialize, a cybersecurity course can help you transition into this dynamic and well-paying career path.
Techniques and Trends in Cyber Security Certification in OMR
- Artificial Intelligence & Machine Learning in Security: AI-driven threat detection and behavioral analysis for identifying cyberattacks. Automated malware analysis to reduce incident response time.
- Cloud Security Solutions: Securing cloud-based platforms like AWS, Azure, and Google Cloud. Implementing Zero Trust Architecture to prevent unauthorized access.
- Ethical Hacking & Penetration Testing: Simulating cyberattacks to identify and patch vulnerabilities. Using tools like Metasploit, Nmap, and Burp Suite for penetration testing.
- Blockchain for Cyber Security: Decentralized security solutions for tamper-proof transactions. Implementing blockchain-based authentication systems.
- IoT (Internet of Things) Security: Protecting smart devices from cyber threats. Implementing secure firmware updates and network segmentation.
The Most Recent Cyber Security Placement in OMR with Tools
The Cyber Security Training Institute in OMR is constantly evolving, introducing new tools to combat advanced threats and cyberattacks. Wireshark is widely used for network traffic analysis, helping security professionals identify suspicious activities. Metasploit is an essential penetration testing tool used for simulating attacks and uncovering vulnerabilities. Burp Suite is a leading web application security tool for finding and fixing security loopholes in websites. Nmap (Network Mapper) helps professionals scan networks for open ports and security risks. For security event management, Splunk provides real-time insights into system logs and cybersecurity threats. Snort is an open-source intrusion detection system (IDS) that monitors network traffic for malicious activities. As cyber threats become more sophisticated, security tools continue to evolve, ensuring organizations stay ahead of hackers and protect sensitive data.
Career Opportunities After Cyber Security Training
Cyber Security Analyst
A Cyber Security Analyst is responsible for monitoring, detecting, and preventing cyber threats within an organization. They analyze security risks, conduct vulnerability assessments, and implement security measures to safeguard sensitive data.
Ethical Hacker
An Ethical Hacker, also known as a Penetration Tester, identifies and exploits security weaknesses in networks, applications, and systems to assess an organization’s security posture. Using tools like Metasploit, Burp Suite, and Nmap.
Incident Response Specialist
An Incident Response Specialist plays a crucial role in mitigating and recovering from cyber incidents such as data breaches, ransomware attacks, and phishing attempts. They investigate security breaches, analyze logs, and use forensic tools to track.
Security Architect
A Security Architect designs and builds secure IT infrastructures for organizations . They develop security policies , frameworks, and protocols to protect against cyber threats. Their responsibilities include risk assessment , encryption implementation , and security software development.
Cyber Forensics Investigator
A Cyber Forensics Investigator specializes in analyzing cybercrime incidents, data breaches, and fraud cases. They collect and examine digital evidence from computers, mobile devices, and networks to trace hackers, recover lost data, and support legal investigations.
Cloud Security Engineer
A Cloud Security Engineer is responsible for securing cloud-based environments like AWS, Microsoft Azure, and Google Cloud Platform (GCP). Their job includes implementing cloud security controls, encryption protocols, and identity management solutions to protect data stored in the cloud.
Skill to Master
Network Security
Ethical Hacking
Risk Assessment
Incident Response
Digital Forensics
Cloud Security
Cryptography
Malware Analysis & Reverse Engineering
Security Compliance
Web Application Security
Cyber Threat Intelligence
SIEM
Tools to Master
Wireshark
Metasploit
Burp Suite
Nmap
Kali Linux
Snort
Splunk
John the Ripper
Aircrack-ng
FTK
OSSEC
OpenVAS
Learn from certified professionals who are currently working.

Training by
Manoj, having 7 yrs of experience
Specialized in: Cyber Security Risk Assessment, Ethical Hacking, Incident Response, and Cloud Security.
Note: Manoj is a certified cybersecurity expert known for his expertise in penetration testing, digital forensics, and vulnerability assessments. He has worked with top organizations to strengthen security frameworks, prevent cyber threats, and train professionals in advanced cybersecurity techniques.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Cyber Security Certification

While some cybersecurity certifications Training are designed for beginners, others require professional experience. Certifications like CISSP, OSCP (Offensive Security Certified Professional), and CISM (Certified Information Security Manager) require candidates to have several years of hands-on experience in cybersecurity roles.
Yes, Job Guarantee a job. Advantage Practical Knowledge Matters, Internships & Projects Helps the Networking & Continuous Learning
Cybersecurity certification prerequisites depend on the type of certification. Entry-level certifications such as CompTIA Security+ and EC-Council’s CEH do not require prior experience and are suitable for beginners. However, advanced certifications like CISSP and CISM require several years of professional experience in information security.
Frequently Asked Questions
Yes! Here’s what you need to know about ACTE demo sessions Free Demo Available, Expert-Led Session, Interactive Q&A, Hands-on Preview
- Industry Experts
- Certified Professionals
- Hands-on Learning Approach
- Mentors & Career Coaches
- Yes, ACTE provides comprehensive placement support for all cybersecurity course students. The program includes resume preparation, interview coaching, and mock tests to help candidates secure jobs in the industry. ACTE has strong partnerships with over 500+ hiring companies, ensuring that students get opportunities in top IT firms, cybersecurity consultancies, and government agencies.
- Upon successful completion of the ACTE Cyber Security Training, students receive a recognized certification that validates their skills in cybersecurity.
- This certification demonstrates expertise in ethical hacking, penetration testing, network security, and risk management, making candidates eligible for job roles like Cyber Security Analyst, Ethical Hacker, and Security Consultant.
- Yes! ACTE emphasizes real-world cybersecurity training by offering live projects that simulate actual security challenges faced by industries. Students get to work on penetration testing, vulnerability assessments, and security audits using tools like Wireshark, Metasploit, and Burp Suite.
)



