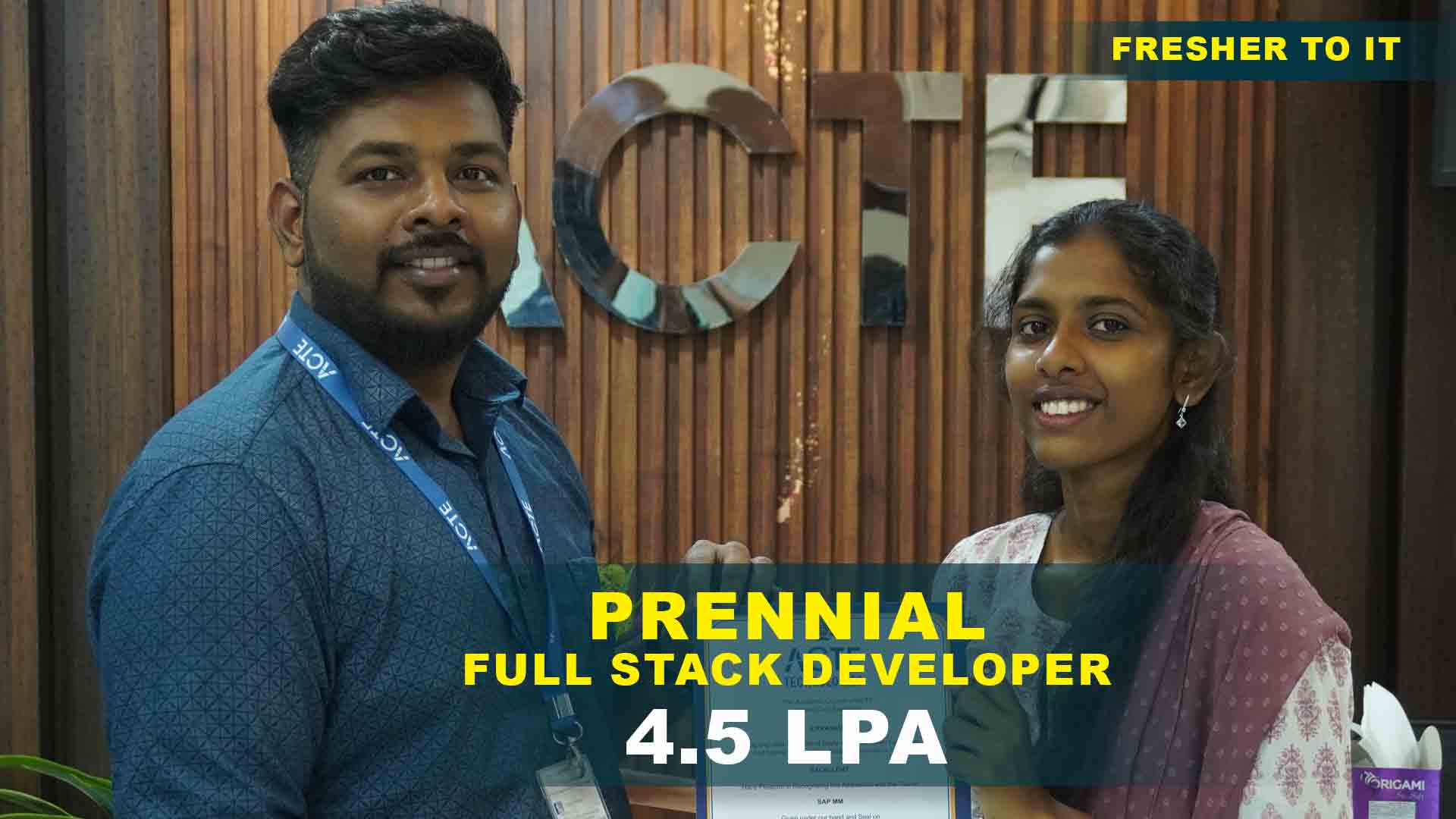
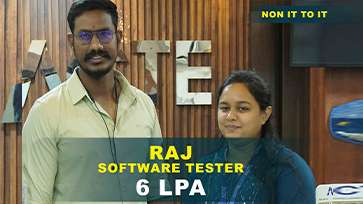
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculum Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
Cyber Security Training Projects
Become a Cyber Security Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Password Strength Checker
Build a simple application that evaluates password strength based on criteria like length, use of special characters, and common patterns.
Basic Firewall Setup
Set up a personal firewall on your computer or a home network using tools like UFW (Uncomplicated Firewall) or Windows Firewall.
Network Scanning with Nmap
Use Nmap to scan your home network, identifying devices and open ports. Document your findings and explore the implications.
Log Analysis Tool
Create a tool that parses and analyzes log files (e.g., from web servers) to identify suspicious activity or patterns.
Vulnerability Assessment
Use tools like OpenVAS or Nessus to conduct a vulnerability assessment of a small network. Document vulnerabilities and suggest remediation.
Create a Honeypot
Set up a honeypot to attract and monitor malicious traffic. Analyze the data collected to understand attack patterns.
Intrusion Detection System (IDS)
Develop or configure an IDS using Snort or Suricata to monitor network traffic for suspicious activities and generate alerts.
Security Incident Response Plan
Create a comprehensive incident response plan for a fictional organization, detailing steps for identification, containment, eradication, and recovery.
Web Application Security Testing
Conduct a thorough security assessment of a web application using tools like Burp Suite. Identify vulnerabilities and propose fixes.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Cyber Security Training Overview
What goals are achieved in a Cyber Security Course?
Students who take a cybersecurity course accomplish a number of important objectives, including learning about different cyber threats and their effects, gaining valuable skills in network security and ethical hacking, managing and implementing security tools and protocols, and designing efficient security policies. In order to better safeguard information systems from possible dangers, they also acquire proficiency in incident response and risk management.
Future works for Cyber Security
- Artificial Intelligence and Machine Learning: AI and machine learning will increasingly be used to detect and respond to threats in real time. These technologies can analyze vast amounts of data to identify patterns and anomalies that may indicate a security breach.
- Quantum Computing: Quantum computers have the potential to break current encryption methods, but they also promise to create new, more secure encryption techniques. Preparing for this shift will be crucial for future cybersecurity.
- Zero Trust Architecture: The Zero Trust approach operates under the tenet that no one should be trusted by default, both inside and outside the business. Verification is a prerequisite for resource access, and it may end up becoming the norm for cybersecurity practices.
- Blockchain Technology: Blockchain technology has potential uses beyond cryptocurrency, such as improving data quality and security through decentralized, tamper-proof records.
- Cybersecurity Automation: As cyber threats become more sophisticated, automation will play a key role in quickly identifying and responding to incidents. Automated systems can handle repetitive tasks and free up human resources for more complex issues.
- Security for IoT Devices: With the proliferation of Internet of Things (IoT) devices, securing them and the data they generate will be a significant challenge. Future security solutions will need to address IoT's unique vulnerabilities.
What new Cyber Security frameworks are there?
The U.S. DoD's Cybersecurity Maturity Model Certification (CMMC) for defence contractors, the most recent ISO/IEC 27001:2022 standard for information security management, and the revised NIST Cybersecurity Framework (CSF) Version 2.0, which expands on supply chain risk management and privacy, are examples of new cybersecurity frameworks. Furthermore, the MITRE ATT&CK® Framework provides information about adversary strategies, and Zero Trust Architecture (ZTA) stresses ongoing access validation. A framework for GDPR compliance and Secure Access Service Edge (SASE) is evolving to handle data protection and integrated security demands in cloud environments, while the CIS Controls Version 8 centres on priority security measures.
Trends and Techniques used in Cyber Security
- Artificial Intelligence and Machine Learning: Threat detection and response capabilities are being improved with the usage of AI and ML. Compared to conventional methods, they can analyze enormous amounts of data faster and more accurately to spot patterns, anomalies, and possible dangers.
- Extended Detection and Response (XDR): XDR provides a unified approach to threat detection and response across various security layers—network, endpoint, server, and email security—offering integrated visibility and automated responses.
- Threat Hunting: Proactive threat hunting involves actively searching for signs of malicious activity within a network rather than relying solely on automated alerts. This technique aims to identify and mitigate threats before they cause significant damage.
- Cloud Security: Securing cloud settings has become essential with the migration to cloud computing. Among the methods are identity and access management (IAM), cloud-native security solutions, and ongoing vulnerability and configuration monitoring.
Cyber Security Uses
In order to defend digital assets and infrastructure from various dangers, such as viruses, cyberattacks, and data breaches, cybersecurity is essential. It helps preserve privacy for people and organizations, protects sensitive data, and guarantees the availability and integrity of systems. Secure communication, regulatory compliance, and public confidence in digital interactions and technologies are all supported by cybersecurity, which protects against unauthorized access, data loss, and system disruptions through the use of techniques like encryption, access controls, threat detection, and incident response.
Career Opportunities After Cyber Security
Security Analyst
A security analyst monitors and defends against cyberattacks on an organization's IT infrastructure. To find and reduce risks, they perform vulnerability assessments, handle security tools.
Penetration Tester (Ethical Hacker)
To identify weaknesses in an organization's systems before malevolent hackers can exploit them, penetration testers, also known as ethical hackers, mimic cyberattacks on the systems.
Security Engineer
A Security Engineer designs and implements robust security systems to protect an organization’s network and data. They configure security infrastructure, such as firewalls and intrusion detection systems.
Incident Responder
Cybercrime investigators are held accountable for managing and reducing cybersecurity-related reservations. coordinating actions to respond activities in the meantime implementing to bring back normal daily activities.
Security Architect
An establishment's safe information technology system is created and designed by an information security architect. They create protective structures and plans, evaluate threats, and incorporate improvements to security.
Chief Information Security Officer (CISO)
A company's chief information security officer, or CISO, is responsible for developing and implementing the information security plan that will protect digital assets and ensure data integrity.
Skill to Master
Risk Assessment
Incident Response
Network Security
Vulnerability Management
Cryptography
Threat Analysis
Regulatory Compliance
Security Policy Development
Ethical Hacking
Security Awareness Training
Forensic Analysis
Problem-Solving
Tools to Master
Wireshark
Nmap
Metasploit
Snort
Burp Suite
Kali Linux
Splunk
OpenVAS
LastPass
AWS Security Hub
CrowdStrike Falcon
Cisco Umbrella
Learn from certified professionals who are currently working.

Training by
Rajiv , having 10 yrs of experience
Specialized in: Cryptography, Data Protection, Secure Communication, and Encryption Algorithms.
Note: Rajiv specializes in cryptography and knows a great deal about safe communication protocols and encryption algorithms. His background in privacy and data security guarantees that students will fully comprehend the process of implementing secure cryptography techniques to safeguard confidential data.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Cyber Security Certification

Although it doesn’t guarantee work, having a cyber security certification dramatically increases your chances of finding employment. Employers will find you more appealing as a candidate because it showcases your expertise in cybersecurity.
Yes, you are allowed to seek multiple Cyber Security course certifications. In fact, pursuing various certifications can be advantageous as it will enable you to gain expertise in different areas of cybersecurity and enhance your overall skill set.
Yes, many Cyber Security certification exams can be taken online. These exams are often administered with remote proctoring, which allows you to take the test from your location while being monitored by a proctor via a secure online platform. This option provides flexibility and convenience.
Acquiring a Cyber Security certification only sometimes necessitates real-world experience, but having it can be highly beneficial. Many entry-level certifications, such as CompTIA Security+, are designed for individuals who may need more hands-on experience, though practical experience can enhance your understanding and performance.
If earning an ACTE Cyber Security Certification fits your demands and fulfils your career ambitions, the time and financial investment will be worthwhile. The cybersecurity skills and knowledge that come with the ACTE certification may help you develop your career and have more earning potential.
Frequently Asked Questions
- Indeed, it's usually possible to attend a demo session before enrolling in a course. You can meet the teacher, get a sneak peek at the course material, and observe how the material is taught. It's a terrific approach to ensure you have all the information you need to make an informed decision before committing to the course.
- ACTE instructors are experienced professionals with extensive expertise in their respective fields. They are industry veterans skilled in various domains, such as cyber security, data science, and cloud computing. Their backgrounds typically include years of practical experience, relevant certifications, and a strong track record of teaching and mentoring students. Their goal is to provide high-quality, hands-on training that equips learners with the skills needed to excel in their careers.
- Absolutely. Many organizations, including ACTE, provide placement aid as part of their training programs. Common components of this help include creating a résumé, being ready for interviews, using job search techniques, and having access to a network of contacts in the field. The goal of placement assistance is to ease the transition of recent graduates into professional jobs by helping them find appropriate employment possibilities.
- Completion Certificate
- Professional Certification
- Certification of Achievement
- In professional and technical programs, students often engage in real-world projects or case studies to gain practical experience. Higher education degrees may include capstone projects involving accurate data or clients. Internships and co-op programs also offer opportunities to work on live projects. Online or self-paced courses might consist of practical assignments or simulations, though the extent can differ. Checking the course details will clarify the inclusion of live projects.
)



