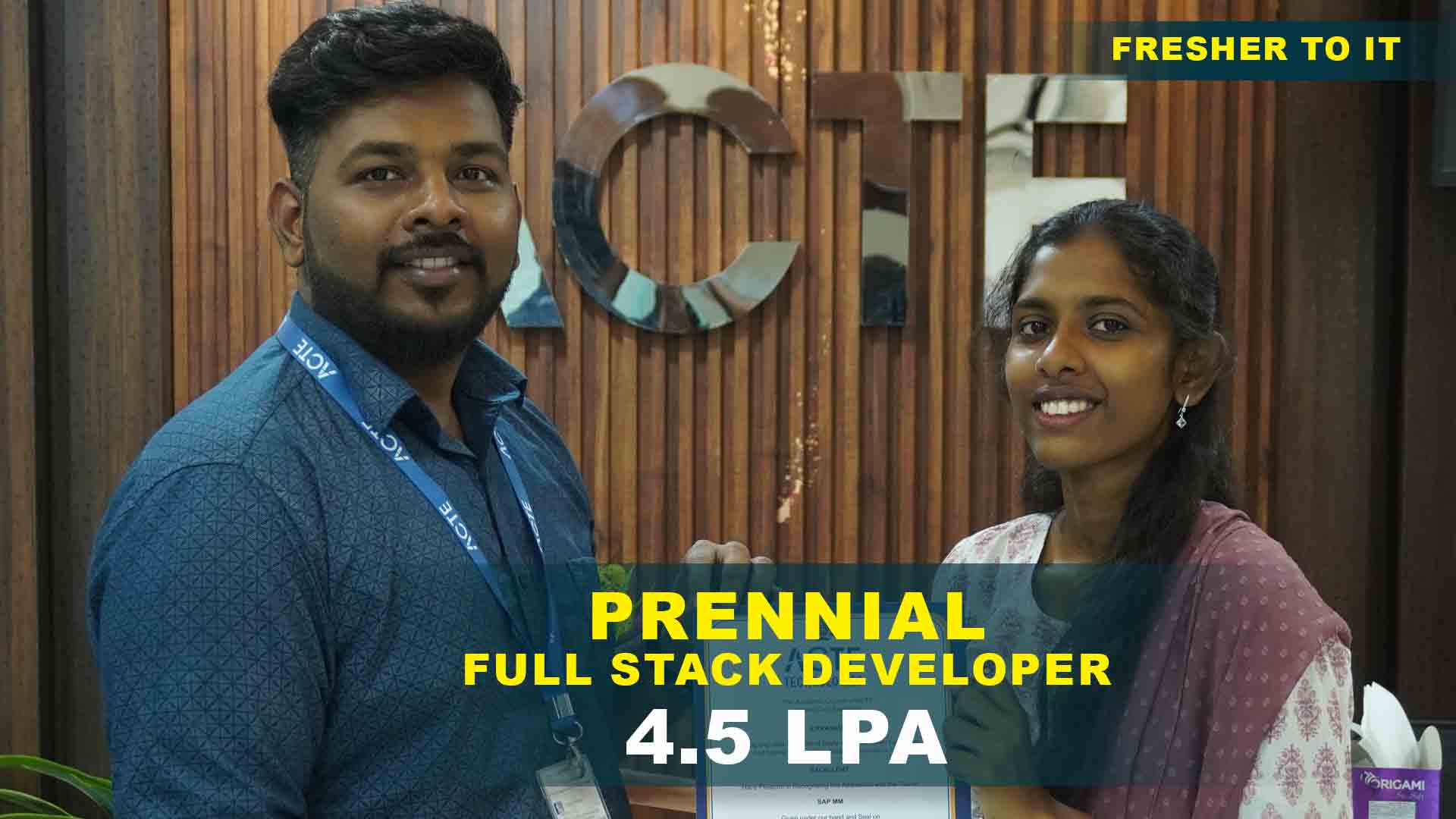
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculum Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
Cyber Security Training Projects
Become a Cyber Security Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Set Up a Home Firewall
To Create a basic task manager that lets users to add, remove, and mark tasks as complete. Also Utilize Express.js for the backend and MongoDB for efficient and scalable data storage.
Password Strength Analysis Tool
Build a weather app that fetches data from an API and displays it to users. Use Node.js for API requests and Express to manage the server efficiently.
Basic Network Scanning with Nmap
Create a real-time chat app using WebSocket, Node.js, integrating user authentication, chat rooms, message history for an interactive experience.
Network Traffic Analysis
Leverage network protocol analyzers like Wireshark to capture and examine network traffic. Analyze various protocols, packets, and potential security vulnerabilities within the traffic.
Vulnerability Scanning
Conduct a vulnerability assessment in a test environment using tools such as OpenVAS or Nessus. Generate a report and rank vulnerabilities according to their risk levels.
Basic Incident Response Plan
Create and document an incident response plan for a fictional organization, detailing procedures for detecting, mitigating, recovering from security incidents effectively.
Custom Intrusion Detection System (IDS)
Configure and maintain a firewall on your home router or a virtual machine to restrict unauthorized traffic and define specific rules for allowing permitted services.
Security Information and Event Management (SIEM) Implementation
Develop a simple tool to evaluate password strength based on length, complexity, and common patterns, using programming languages like Python.
Penetration Testing of a Web Application
Learn Nmap for network discovery and port scanning. Document the process, explore various scan types, and analyze insights for a comprehensive understanding.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Cyber Security Training Overview
Goals are achieved in a Cyber Security Course in HSR Layout
Students enrolled in a Advanced Cyber Security Training Institute in HSR Layout achieve several key goals, such as understanding various cyber threats and their impacts, developing essential skills in network security and ethical hacking, managing and implementing security tools and protocols, and creating effective security policies. They also gain expertise in incident response and risk management to enhance the protection of information systems against potential threats.
Future works for Cyber Security Training for Beginners
- Artificial Intelligence and Machine Learning: AI and machine learning are increasingly being used to detect and respond to threats in real time. These technologies can analyze large volumes of data to identify patterns and anomalies that could indicate a security breach.
- Quantum Computing: Quantum computers have the potential to undermine current encryption methods, but they also promise to introduce more secure encryption techniques. Preparing for this technological shift will be crucial for the future of cybersecurity.
- Zero Trust Architecture: The Zero Trust approach is based on the principle that trust should never be assumed, whether inside or outside an organization. Access to resources requires verification, and this model may become the new standard for cybersecurity practices.
- Blockchain Technology: While blockchain is widely known for its use in cryptocurrency, it also has potential applications for enhancing data security and integrity through decentralized, tamper-proof records.
- Cybersecurity Automation: As cyber threats grow more sophisticated, automation will play a key role in quickly detecting and responding to incidents. Automated systems will handle routine tasks, freeing up human resources for more complex challenges.
- Security for IoT Devices: As Internet of Things (IoT) devices become more prevalent, ensuring their security and protecting the data they generate will present significant challenges. Future security solutions will need to address the specific vulnerabilities unique to IoT.
New Cyber Security frameworks Program in HSR Layout
Best cybersecurity Course Training in HSR Layout include the U.S. Department of Defense's Cybersecurity Maturity Model Certification (CMMC) for defense contractors, the latest ISO/IEC 27001:2022 standard for information security management, and the updated NIST Cybersecurity Framework (CSF) Version 2.0, which emphasizes supply chain risk management and privacy. Additionally, the MITRE ATT&CK® Framework offers insights into adversary tactics, and Zero Trust Architecture (ZTA) focuses on continuous access verification. A framework for GDPR compliance and Secure Access Service Edge (SASE) is evolving to address data protection and integrated security needs in cloud environments, while the CIS Controls Version 8 highlights key security priorities.
Trends and Techniques used in Cyber Security Certification Course in HSR Layout
- Artificial Intelligence and Machine Learning: AI and ML are enhancing threat detection and response capabilities by enabling faster and more accurate analysis of large data sets, helping to identify patterns, anomalies, and potential risks more effectively than traditional methods.
- Extended Detection and Response (XDR): XDR offers a comprehensive approach to threat detection and response across multiple security layers—network, endpoint, server, and email security—providing integrated visibility and automated response mechanisms.
- Threat Hunting: Proactive threat hunting involves actively searching for indicators of malicious activity within a network, rather than depending solely on automated alerts. This method seeks to identify and address threats before they lead to significant damage.
- Cloud Security: As cloud computing becomes more widespread, securing cloud environments has become crucial. Key strategies include identity and access management (IAM), cloud-native security solutions, and continuous vulnerability and configuration monitoring.
Cyber Security Uses
Ethical Hacking and Cyber Security Training Program in HSR Layout is crucial for protecting digital assets and infrastructure from a range of threats, including viruses, cyberattacks, and data breaches. It ensures the privacy of individuals and organizations, safeguards sensitive data, and maintains the availability and integrity of systems. Cybersecurity supports secure communication, regulatory compliance, and public trust in digital interactions and technologies by defending against unauthorized access, data loss, and system disruptions through methods like encryption, access controls, threat detection, and incident response.
Career Opportunities After Cyber Security
Security Analyst
A security analyst monitors and safeguards IT infrastructure, conducts vulnerability assessments, manages security tools, investigates incidents, performs audits, and responds to cyber threats and breaches.
Penetration Tester (Ethical Hacker)
Ethical hackers conduct simulated cyberattacks to identify vulnerabilities, evaluate systems, networks, and applications, and deliver comprehensive reports to enhance security defenses.
Security Engineer
A Security Engineer designs and deploys security systems to protect networks and data. They configure firewalls, intrusion detection, and enforce security policies to prevent cyber threats.
Incident Responder
An incident responder manages cybersecurity incidents, coordinates response efforts, restores operations, investigates breaches, and assesses attack scope, playing a crucial role in security management.
Security Architect
A Security Architect designs and builds secure IT infrastructures, develops security frameworks, assesses risks, and integrates security solutions to create a resilient environment against cyber threats.
Chief Information Security Officer (CISO)
The CISO designs and enforces security strategies to safeguard digital assets, ensure data integrity, manage risks, oversee compliance, and establish security policies.
Skill to Master
Network Security Management
Threat Detection and Response
Vulnerability Assessment
Penetration Testing
Cryptography
Incident Management
Security Policy and Compliance
Security Architecture and Design
Forensic Analysis
Risk Management
Security Awareness Training
Security Tool Proficiency
Tools to Master
Nmap (Network Mapper)
Wireshark
Metasploit Framework
Nessus
Burp Suite
Snort
Kali Linux
Splunk
OpenVAS (Open Vulnerability Assessment System)
IDA Pro (Interactive DisAssembler)
Cuckoo Sandbox
LogRhythm
Learn from certified professionals who are currently working.

Training by
Rajiv , having 10 yrs of experience
Specialized in: Cryptography, Data Protection, Secure Communication, and Encryption Algorithms.
Note: Rajiv specializes in cryptography and knows a great deal about safe communication protocols and encryption algorithms. His background in privacy and data security guarantees that students will fully comprehend the process of implementing secure cryptography techniques to safeguard confidential data.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Cyber Security Certification

While a cybersecurity certification doesn’t guarantee employment, it significantly enhances your chances of securing a job. It demonstrates your expertise in cybersecurity, making you a more attractive candidate to employers. However, factors like hands-on experience, specific employer needs, and the overall job market also play a role in getting hired.
Yes, you can pursue multiple cybersecurity course certifications. In fact, earning various certifications can be beneficial as it allows you to build expertise in different areas of cybersecurity, expanding your overall skill set. Certifications can cover a wide range of topics, from foundational knowledge to specialized skills in fields like ethical hacking, cloud security, or risk management.
Yes, many Cyber Security Certification Course in HSR Layout exams are available online. These exams are typically administered with remote proctoring, allowing you to take the test from your own location while being monitored by a proctor through a secure online platform. This offers flexibility and convenience. However, it’s important to review the specific certification provider’s requirements and procedures for online exams to ensure you meet all necessary technical and environmental conditions for a seamless testing experience.
Obtaining a cybersecurity certification does not always require real-world experience, but it can be highly advantageous. Many entry-level certifications, like CompTIA Security+, are designed for individuals with limited hands-on experience, though practical experience can improve your understanding and performance. Advanced certifications, such as CISSP or CISM, often recommend or require prior field experience, as they address more complex concepts and responsibilities.
Frequently Asked Questions
- Yes, it's often possible to attend a demo session before enrolling in a course. This allows you to meet the instructor, preview the course material, and see how the content is delivered. It’s a great way to gather all the information you need to make an informed decision before committing to the course.
- Experienced Professionals: ACTE instructors are seasoned experts with extensive experience in Cyber Security Training for Beginners.
- Industry Experts: They possess diverse skills in cybersecurity, data science, and cloud computing.
- Hands-On Knowledge: Many have years of practical experience, relevant certifications, and a strong teaching background.
- Effective Mentors: They focus on delivering high-quality, practical training to help learners build essential career skills.
- Absolutely. Many organizations, including ACTE, offer placement assistance as part of their training programs. This support typically includes resume building, interview preparation, job search strategies, and access to a network of industry contacts. The aim of placement assistance is to help recent graduates transition smoothly into professional roles by connecting them with suitable employment opportunities.
- Certificate of Completion
- Professional Qualification
- Certificate of Accomplishment
- In professional and technical programs, students frequently work on real-world projects or case studies to gain hands-on experience. Higher education degrees may feature capstone projects that involve real data or actual clients. Internships and co-op programs also provide opportunities to work on live projects. Online or self-paced courses may include practical assignments or simulations, though the level of involvement can vary. Reviewing the course details will help clarify whether live projects are included.
)



