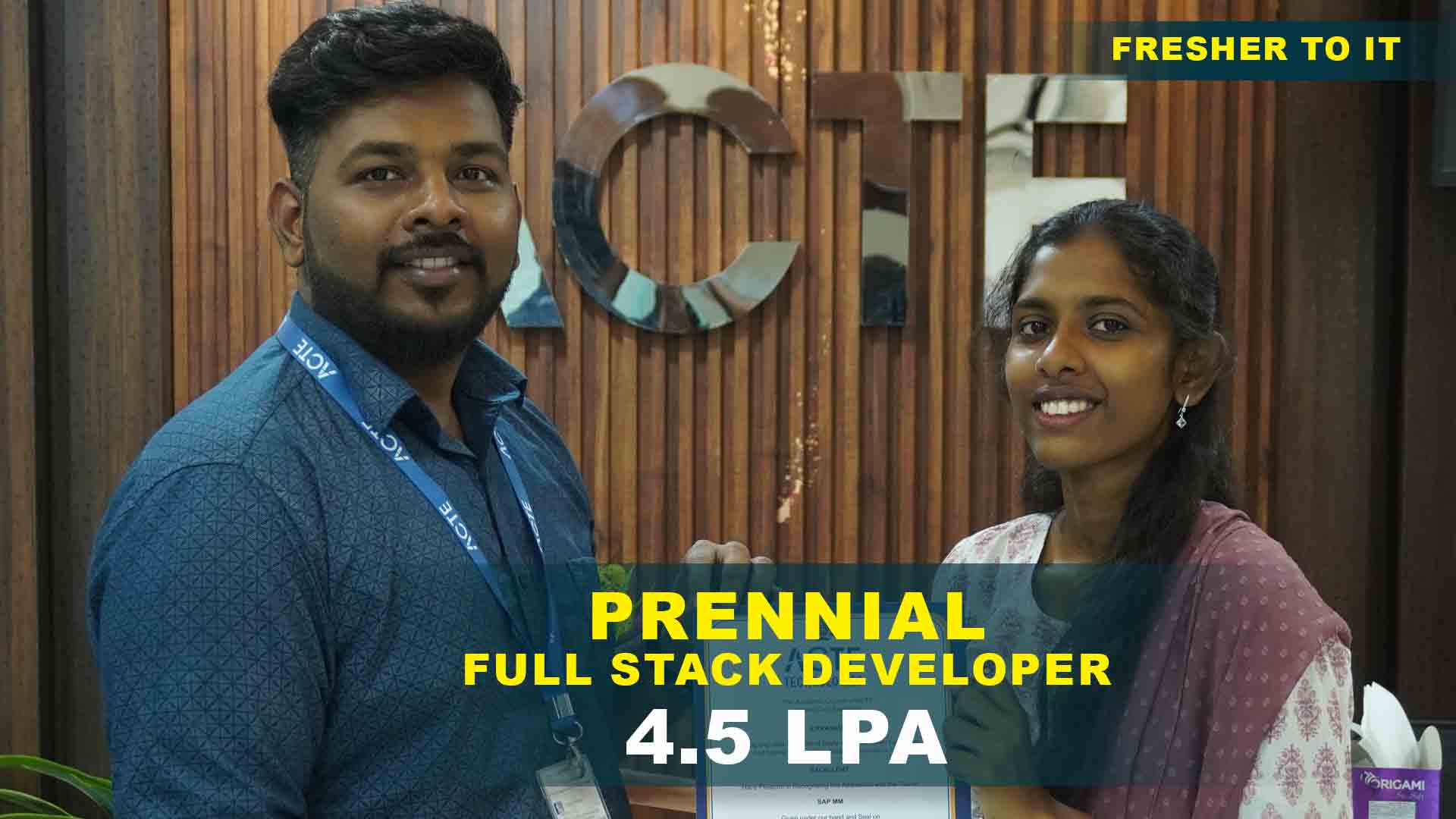
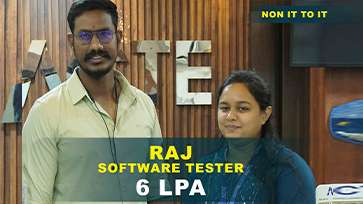
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculum Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
- Security architecture basics
- Threat landscape overview
- Risk management workflows
- Compliance basics
- ERP integration basics
- Advanced fundamentals
- TCP/IP basics
- Secure routing
- IDS/IPS setup
- Network monitoring
- Advanced networking strategies
- Symmetric encryption
- Asymmetric encryption
- Hashing techniques
- Digital certificates
- Advanced cryptography strategies
- Windows security basics
- Linux security workflows
- File system protection
- Advanced OS security
- Vulnerability scanning
- Exploitation basics
- Social engineering
- Reporting methods
- Security hardening
- Advanced penetration testing
- Cloud architecture basics
- SaaS security workflows
- Web application protection
- ERP integration workflows
- Advanced cloud security
- Incident detection
- Response workflows
- Evidence collection
- Forensic analysis
- Reporting methods
- Advanced incident strategies
- ISO standards basics
- GDPR workflows
- HIPAA compliance
- Audit workflows
- Risk assessment
- Advanced governance strategies
- Networking project
- Encryption project
- Ethical hacking project
- Cloud security project
- Incident response project
- End-to-end cyber security workflow
Cyber Security Projects
Become a Cyber Security Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Networking Security
Configure firewalls and VPNs. Practice secure routing and monitoring workflows for basic protection.
Encryption Basics
Implement symmetric and asymmetric encryption. Apply hashing techniques to secure sensitive data.
OS Security
Apply patches and configure access control. Strengthen operating system security with simple workflows.
Ethical Hacking
Perform vulnerability scans and exploitation. Document findings and apply security hardening techniques.
Cloud Security
Secure SaaS applications and APIs. Configure workflows for hybrid and multi-cloud environments.
Incident Response
Detect and respond to simulated attacks. Collect evidence and perform forensic analysis.
End-To-End Workflow
Execute a complete cyber security project. Integrate networking, encryption, and incident response.
Compliance Implementation
Apply ISO, GDPR, and HIPAA standards. Monitor workflows and prepare audit-ready reports.
Penetration Testing
Conduct advanced penetration tests. Deliver detailed reports and recommend mitigation strategies.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Cyber Security Training Overview
Goals Accomplished by Cyber Security Course in Pondicherry
The Cyber Security Training in Pondicherry helps learners understand how security frameworks ensure scalability and reliability in enterprise systems. Participants gain clarity on how cyber security reduces manual effort in managing threats and vulnerabilities. The training explains how cyber security supports compliance with organizational standards. Learners also understand how cyber security improves transparency across departments. Practical examples show how cyber security enhances monitoring and reporting. The program highlights how integration with ERP and CRM platforms strengthens enterprise workflows. Learners build confidence in handling firewalls, intrusion detection, and encryption. The section emphasizes how cyber security supports decision-making by providing accurate insights. By the end, participants recognize the goals accomplished through cyber security training. This foundation prepares them for certification and placement opportunities.
Future Career Opportunities Emerging from Cyber Security Placement in Pondicherry
- Security Analyst: Learners apply cyber security skills to monitor enterprise systems. They reduce manual effort and improve usability. This role supports digital transformation.
- Penetration Tester: Participants analyze workflows and create cyber security-based solutions. They design environments that improve productivity. Testers document processes for compliance.
- Network Security Engineer: Learners connect cyber security with enterprise systems. Integration ensures smooth data flow and reporting. This strengthens enterprise solutions.
- Support Consultant: Professionals assist teams in troubleshooting cyber security issues. They provide guidance on maintaining secure environments. Consultants also train end-users.
- Certification-Oriented Roles: Completing the program prepares learners for Cyber Security Certification course. Certification adds credibility and opens specialized positions. Employers value certified expertise.
New Frameworks Introduced in Cyber Security Certification in Pondicherry
The Cyber Security Certification in Pondicherry introduces learners to frameworks that reflect industry changes. Participants study modern models that improve scalability and performance. The training explains how new features support integration with cloud-based systems. Learners gain exposure to modular approaches that simplify administration. Security frameworks are also covered to ensure compliance with organizational policies. Learners practice using tools that support analytics and reporting. The program highlights how advancements meet business demands. Practical exercises show how these frameworks are applied in real projects. Learners finish with a clear view of how updates shape cyber security strategies. This section ensures participants stay current with industry standards.
Trends and Essential Skills Related to Cyber Security Placement in Pondicherry
- Industry Demand: Organizations increasingly seek cyber security professionals. Learners with these skills find placement opportunities growing steadily. This makes Cyber Security Placement in Pondicherry more relevant.
- Technical Skills: Employers look for strong knowledge of firewalls, encryption, and intrusion detection. Learners must understand integration, configuration, and troubleshooting. These skills are tested during placement interviews.
- Analytical Thinking: Placement success depends on problem-solving ability. Learners must analyze workflows and suggest improvements. Analytical skills show readiness for real-world challenges.
- Communication Skills: Clear reporting and teamwork are essential. Learners must explain cyber security outcomes to managers and users. Good communication improves placement chances.
- Adaptability: Employers value professionals who adapt to new tools. Learners must show flexibility in learning updated frameworks. Adaptability ensures long-term career growth.
Applications and Uses of Cyber Security Course in Pondicherry
The Cyber Security Training in Pondicherry connects security knowledge with practical business applications. Learners see how cyber security reduces manual effort in managing enterprise infrastructure. The training explains how cyber security supports compliance and audit processes. Participants study how cyber security improves customer service workflows. Real-world examples show how cyber security reduces downtime during attacks. Learners also explore how cyber security integrates with ERP and CRM platforms. The program highlights uses in reporting and analytics. Applications in finance, healthcare, manufacturing, and IT services are also discussed. Learners finish with a broad view of how cyber security supports multiple industries. This section ties technical learning to everyday business needs.
Career Opportunities After Cyber Security Training
Cyber Security Analyst
Monitors threats, detects vulnerabilities, and responds to incidents. Ensures enterprise systems remain secure and compliant.
Network Security Engineer
Configures firewalls, VPNs, and IDS/IPS systems. Protects networks from unauthorized access and cyber threats.
Ethical Hacker
Performs penetration testing and vulnerability assessments. Provides reports and recommends mitigation strategies.
Cloud Security Specialist
Secures cloud platforms, SaaS applications, and APIs. Implements hybrid and multi-cloud security workflows.
Compliance Officer
Applies ISO, GDPR, and HIPAA standards. Monitors governance workflows and prepares audit-ready documentation.
Incident Response Specialist
Detects, analyzes, and responds to cyber attacks. Collects forensic evidence and strengthens organizational resilience.
Skills to Master
Networking Security
Encryption Workflows
Cryptography Techniques
OS Hardening
Ethical Hacking
Penetration Testing
Cloud Security
Application Protection
Incident Response
Forensic Analysis
Compliance Monitoring
Troubleshooting
Tools to Master
Wireshark
Nmap
Kali Linux
Metasploit
Burp Suite
Nessus
Splunk
SIEM tools
Cloud consoles
Security configuration utilities
Audit tools
Workflow automation scripts
Learn from certified professionals who are currently working.

Training by
Karthik, having 12 yrs of experience
Specialized in: Networking Security, Ethical Hacking, Cloud Security, Compliance, Incident Response.
Note: Karthik is recognized for his practical teaching style and success in guiding learners to master Cyber Security with clear, hands-on outcomes.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Cyber Security Certification

The exam focuses on network defense, ethical hacking, risk management, and compliance with global security standards.
Yes, the Cyber Security Course in Pondicherry provides practical exposure to threat detection and vulnerability analysis using real-time labs.
- Scenario-driven penetration testing tasks
- Case studies on enterprise risk management
- Mock exams simulating certification conditions
- Peer reviews for collaborative evaluation
- Employers value certified professionals for enterprise-level expertise.
- Consulting firms prefer certified staff for compliance and audits.
- Security teams rely on certified professionals for defense strategies.
- IT service providers demand certification for cyber resilience projects.
Yes, the certification aligns with global standards in cybersecurity and evolving frameworks for cloud and AI-driven defense.
The certification usually takes 8–10 weeks depending on learner progress.
- Placement services connect learners with security-focused employers
- Career guidance prepares candidates for cybersecurity interviews
- Alumni networks assist with referrals
- Local hiring events provide direct recruitment opportunities
- Digital guides on cybersecurity modules
- Practice tests simulating exam conditions
- Instructor-led sessions explaining advanced topics
- Online forums for peer-to-peer learning
Frequently Asked Questions
- The Cyber Security Training Course emphasizes cloud security advancements Zero-trust frameworks are integrated into practical sessions.
- Learners receive mentoring sessions. Instructor-led feedback ensures continuous improvement.
- Yes, placement assistance is provided to eligible learners. Employer tie-ups ensure direct hiring opportunities.
- SIEM dashboards
- Penetration testing utilities
- Compliance modules
- Yes, the Cyber Security Certification Course integrates real-time projects. Projects are designed to validate practical cybersecurity skills.
)



