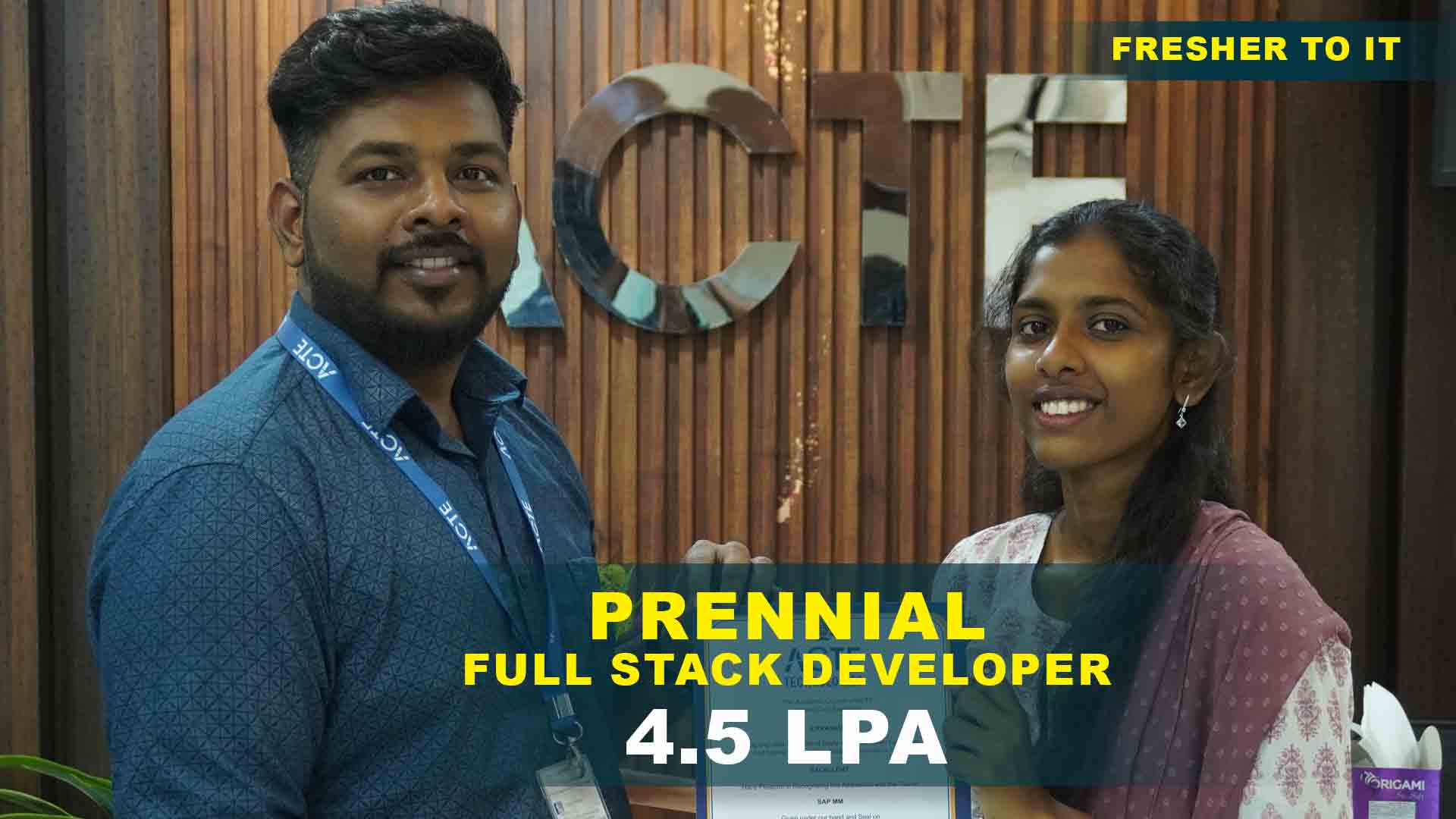
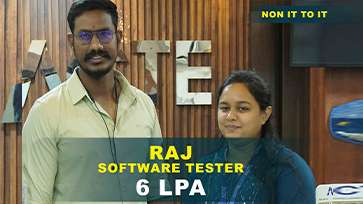
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculam Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
Ethical Hacking Training Projects
Become a Ethical Hacking Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Cracking Passwords
Use tools like Hashcat to break simple password hashes and discover the importance of coming up with strong passwords.
Phishing Simulation
Write a fake email to get knowledge about social engineering techniques and how to recognize them.
Vulnerability Scanning
Use programs like Nessus or OpenVAS to locate common vulnerabilities on a local network.
Compile Your Results into a Professional Report
Perform a penetration test in a controlled environment and record your results.
Network Sniffing
Record and examine network traffic using Wireshark, paying particular attention to unencrypted data flow.
Construct a Honeypot
Place a honeypot to draw in attackers and observe how they operate while examining the information gathered.
Automated Vulnerability Assessment Tool
Write a unique script to scan and report vulnerabilities for certain networks or applications.
Blue Team against Red Team Exercises
To evaluate offensive and defensive security strategies in a controlled environment, build up a simulated cyberattack.
Exploit Development
Learn to develop exploits for certain vulnerabilities and test them in a laboratory environment to gain a deeper understanding of the physics involved.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Ethical Hacking Training Overview
Ethical Hacking Programmer’s Potential Career Paths
Specialized programmers in ethical hacking can pursue a multitude of career paths, each with unique opportunities and challenges.Penetration testers assist companies in strengthening their defenses by mimicking assaults to find weaknesses in systems and networks. Security consultants use their knowledge to help businesses create strong security plans and protect their digital assets. To manage and lessen the consequences of cyberattacks and enable enterprises to promptly recover and limit damage, incident responders are essential. Security analysts keep an eye on and evaluate security systems, interpreting signals and putting preventative measures in place to fend off possible attacks. Malware experts also explore the subtleties of harmful software, observing its actions and developing countermeasures to lessen and stop its effects.
What Are the Requirements for an Ethical Hacking Training ?
- Fundamental IT and Networking Knowledge: Understanding the fundamentals of ethical hacking requires a good knowledge of computer networks, operating systems, and common IT concepts.
- Knowing Programming Languages: Being able to write scripts and identify vulnerabilities requires knowledge of programming languages like Python, JavaScript, or C++.
- Understanding of Security Fundamentals: Gaining an understanding of the fundamentals of cybersecurity, such as risk management, authentication, and encryption, is essential to comprehending ethical hacking tactics.
- Access to Applicable Software and Tools: For practical experience and simulations, students should have access to programs and resources like as Nmap, Wireshark, Burp Suite, and virtual machines.
- Dedicated to Ethical Practices: A strong ethical foundation and adherence to legal criteria are necessary for the ethical hacking to be used in a responsible and professional manner.
Reasons to Consider Enrolling in an Ethical Hacking Training
For people who want to work in cybersecurity, enrolling in an ethical hacking Training has various benefits. Because cyberattacks are becoming more sophisticated, there is a growing need for qualified experts who can successfully safeguard important data and systems. By enrolling in an ethical hacking Training , which gives you meaningful, hands-on experience with the newest tools and techniques utilized in the field, you may learn information and abilities that you can apply in authentic situations. Many programs also offer certification upon completion, which might improve your reputation and increase your chances of landing a job in a cutthroat field. Being up to date on industry advancements places you at the forefront of cybersecurity methods and innovations, which is an immense benefit.
Techniques and Trends in Ethical Hacking Development
- Automated Penetration Testing: Using automated tools and frameworks to find vulnerabilities and run penetration tests more quickly and effectively.
- Behavioral analytics: Examining user behavior trends to spot anomalies and potential security threats before they materialize into breaches.
- Red Teaming and Blue Teaming: Using offensive security techniques to imitate assaults and defensive security techniques to bolster defenses and reaction plans.
- Integration of AI and Machine Learning: Machine learning and AI algorithms are used to improve threat detection, automate responses, and forecast upcoming assaults.
- Zero Trust Architecture: Putting into practice a zero-trust security strategy that requires constant user and device authentication since it assumes that all network communication is unreliable.
The Most Recent Ethical Hacking Tools
- Nmap: A network scanning program that provides a wealth of information about network hosts and services. It is used for network discovery and vulnerability detection.
- Burp Suite: An all-inclusive online vulnerability detector that facilitates finding and taking advantage of holes in web applications.
- Metasploit Framework: The open-source penetration testing platform Metasploit Framework comes with a range of tools, payloads, and vulnerabilities for doing security assessments.
- Cobalt Strike: A paid adversary emulation program with sophisticated post-exploitation and threat simulation capabilities for penetration testing.
Career Opportunities After Ethical Hacking
Penetration Tester
In order to identify vulnerabilities before malicious hackers do, penetration testers—also referred to as ethical hackers—attack an organization's networks, systems.
Security Consultant
They evaluate current security protocols, pinpoint possible threats, and create all-encompassing security plans customized to the demands of the company.
Incident Responder
Responding emergency personnel to cybersecurity emergencies are responsible for controlling and mitigating the effects of intrusions and attacks.
Security Analyst
Security analysts monitor the network and systems of a company for any signs of anomalous activity or security breaches.
Malware Analyst
The study and analysis of dangerous software to comprehend its behavior, source, and consequences is the area of expertise for malware analysts.
Security Architect
In order to guarantee that all systems and networks are safe, security architects develop and execute secure IT infrastructures for businesses.
Skill to Master
Vulnerability Assessment
Penetration Testing
Network Security
Malware Analysis
Cryptography
Ethical Hacking Tools
Security Policy Development
Incident Response
Social Engineering
Forensic Analysis
Risk Management
Regulatory Compliance
Tools to Master
Nmap
Metasploit Framework
Burp Suite
Wireshark
Nessus
Aircrack-ng
Hydra
John the Ripper
OWASP ZAP
Kali Linux
Maltego
Cobalt Strike
Learn from certified professionals who are currently working.

Training by
Ravi , having 7+ yrs of experience
Specialized in:Ethical Hacking Tools, OSINT (Open Source Intelligence), Social Engineering, and Red Team Operations.
Note: Ravi is passionate about teaching the latest hacking tools and techniques. He engages students with hands-on labs and real-life hacking scenarios, ensuring they gain practical skills necessary for ethical hacking roles.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Ethical Hacking Certification

Getting certified in ethical hacking may improve your cybersecurity abilities, increase your employability, and give you a thorough grasp of how to defend networks against hostile assaults.
Although having a qualification greatly increases your employability, employment is not guaranteed. A mix of certificates, experience, and talents is frequently sought for by employers.
Certification-specific requirements differ. While some may imply prior experience or credentials in general IT or cybersecurity, others may demand a baseline understanding of networking, security, or programming.
You can take exams remotely with the help of online exam choices offered by several credential organizations. For more information, contact the relevant certifying body.
Although it’s not always necessary, practical experience is often helpful. It aids in solidifying the knowledge you’ve gained and gets you ready for real-world situations you could encounter in the workplace.
Any certification’s worth, including ACTEs, is contingent upon your professional objectives and the degree of industry recognition of the credential. Examine the program’s track record, employment placement percentage, and alumni reviews to see whether it fits your goals.
Frequently Asked Questions
- Classroom Training
- Online Training
- Self-Paced Learning
- Bootcamps/Workshops
- A lot of educational institutions provide lessons that you may see later on recordings of the ones you missed. To make up for the information missed, some may even provide the opportunity to join a different batch.
- You should get in touch with the customer care or support staff of the training provider by phone, chat, or email. Typically, their website includes contact details.
- Usually, you may register for the course online by completing a form and paying for it on Acte's website.
- As an alternative, you might be able to register in person at a nearby branch or contact them directly for help.
- Yes, using a learning management system (LMS) or a comparable platform, the majority of training providers provide online access to course materials, including video lectures, slides, assignments, and supplementary resources.
)



