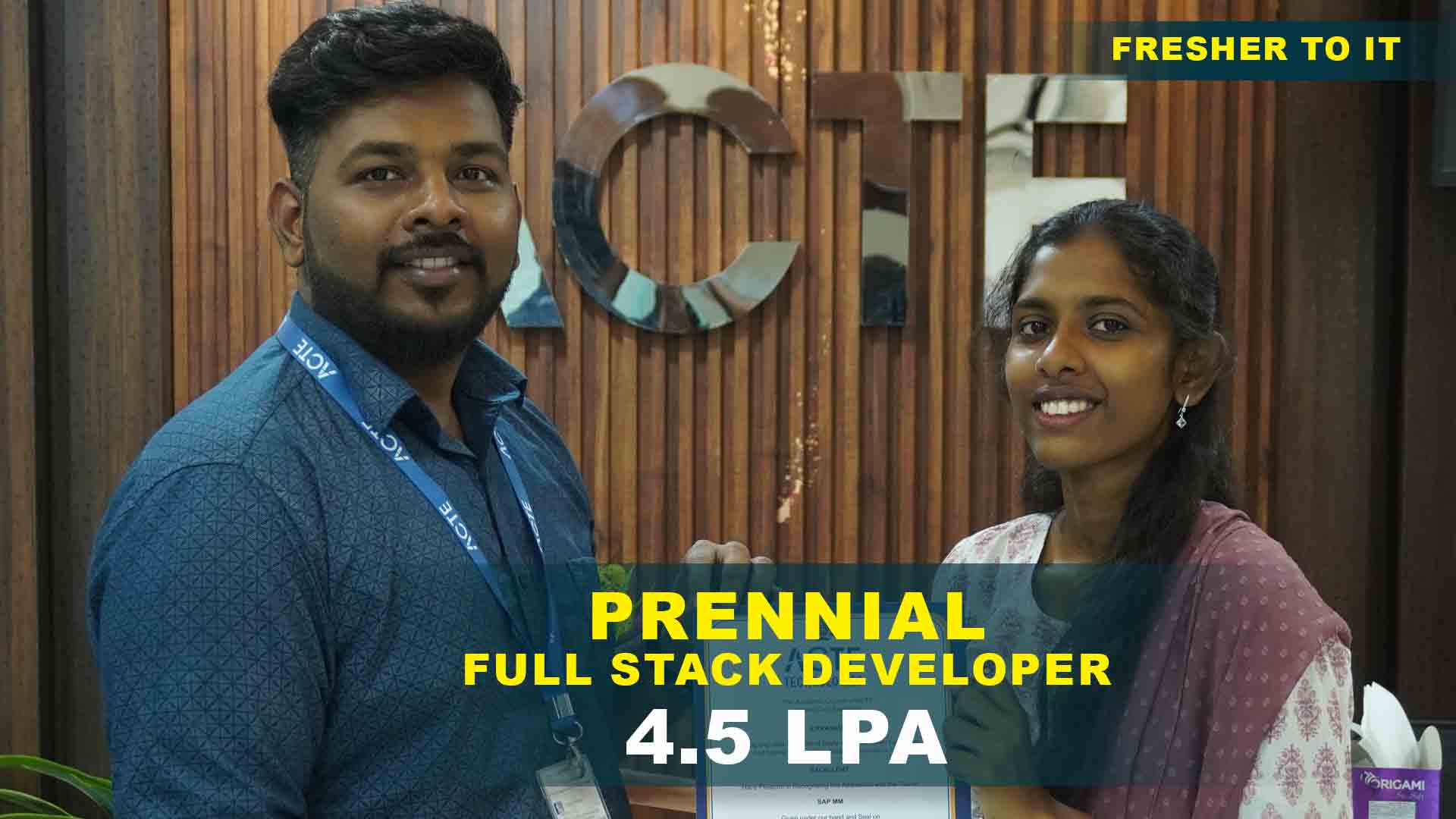
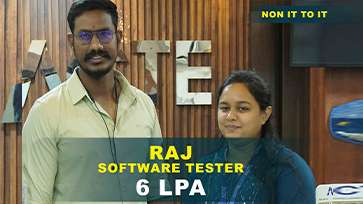
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculum Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
- Overview of Cyber Security Fundamentals
- Types of Hackers and Cybercrime Activities
- Cyber Security Frameworks and Policies
- Network Security Fundamentals
- Ethical Hacking Methodologies
- Configuring Secure Network Architectures
- Network Scanning and Vulnerability Testing
- Mitigating DDoS and Spoofing Attacks
- VPN and Encryption Concepts
- Footprinting and Reconnaissance
- Scanning Networks and Systems
- Post-Exploitation and Reporting
- Using Metasploit and Kali Linux Tools
- Privilege Escalation and Maintaining Access
- Secure Coding and Patching
- Web Application Firewalls (WAF)
- Penetration Testing Tools for Web Apps
- Web Application Vulnerabilities (OWASP Top 10)
- Cross-Site Scripting and SQL Injection
- Session Hijacking and Authentication Flaws
- Understanding Cloud Infrastructure Security
- Cloud Threat Models and Risk Mitigation
- Endpoint Protection Techniques
- Data Loss Prevention Strategies
- Zero Trust Security Models
- Incident Detection and Response Lifecycle
- Collecting and Preserving Digital Evidence
- Forensic Investigation Techniques
- Root Cause Analysis and Reporting
- Post-Incident Mitigation Plans
- Encryption Algorithms and Hashing
- Public Key Infrastructure (PKI)
- Digital Signatures and Certificates
- Data Encryption Tools and Standards
- Blockchain and Data Security Applications
- Secure Key Management Practices
- Introduction to ISO, GDPR, and NIST Standards
- Risk Assessment and Management Frameworks
- Governance, Risk, and Compliance (GRC) Tools
- Audit and Security Reporting Procedures
- Disaster Recovery and Business Continuity
- Design and Execute a Security Implementation Plan
- Penetration Testing and Vulnerability Assessment
- Compliance Reporting and Risk Mitigation Strategies
- Interview Preparation and Certification Guidance
Cyber Security Training Projects
Become a Cyber Security Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Password Strength Analyzer
Create a Python-based password strength checker to evaluate complexity, length, and special characters. Understand authentication fundamentals, encryption basics, and secure credential handling to build awareness of digital security practices.
Network Traffic Monitoring
Analyze live network traffic using Wireshark or similar tools. Practice packet inspection, IP tracking, and network scanning to identify suspicious activities and understand transmission patterns, strengthening analytical and observation skills.
Malware Analysis Simulation
Explore malware behavior in sandbox environments to learn how malicious files affect systems. Practice isolation, signature-based detection, and reporting to strengthen problem-solving, risk assessment, and awareness of real-world cyber threats.
Firewall Configuration and Testing
Configure a network firewall and apply access control policies to manage inbound and outbound traffic securely. Gain hands-on experience with intrusion prevention tools and strengthen understanding of perimeter defense mechanisms for enterprise networks.
Phishing Detection System
Develop a phishing email detection model using machine learning. Collect datasets, train classifiers, and identify malicious links to understand AI’s role in cybersecurity while improving skills in data preprocessing, analysis, and pattern recognition.
Secure Web Application Design
Build a small web application and secure it against common vulnerabilities by applying HTTPS, input validation, and encryption standards. Emphasize OWASP Top 10 principles to bridge development with cybersecurity concepts and strengthen online system security awareness.
Penetration Testing Simulation
Perform ethical hacking on virtualized systems using tools like Metasploit and Nmap. Identify vulnerabilities, document exploit paths, and strengthen offensive security skills while learning patching strategies — ideal for learners pursuing ethical hacking careers.
Threat Intelligence Dashboard
Build an integrated dashboard using SIEM tools like Splunk or ELK Stack. Analyze logs, visualize cyber threats, and monitor incidents to develop skills in real-time defense operations, data analytics, and security automation for enterprise cybersecurity.
Cloud Security Architecture
Design a secure cloud infrastructure on AWS or Azure by configuring IAM roles, firewalls, and encryption policies. Learn compliance, multi-layer security, and access control to protect cloud-based systems and data, preparing for advanced cloud security roles.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Cyber Security Training Overview
Reasons to Consider Enrolling in Cyber Security Course in Anna Nagar
Learners gain confidence through practical modules in ethical hacking, network defense, and risk management. By enrolling in the Cyber Security Training in Anna Nagar, students bridge academic learning with workplace expectations. Practical exercises and projects guarantee that knowledge translates into real‑world applications. The training also develops adaptability, creativity, and problem‑solving abilities. Learners are introduced to firewalls, intrusion detection systems, and monitoring dashboards for enhanced productivity. By the end of the course, participants will have measurable progress and a portfolio of completed projects. This block highlights the transformation from beginner to capable cyber security professional.
Overview of the Most Recent Cyber Security Tools
- Intrusion Detection Systems: Monitor networks for malicious activity. This training ensures readiness for real-world enterprise projects.
- Encryption Utilities: Secure sensitive data with advanced cryptographic methods. Training equips learners with adaptability and analytical confidence.
- Cloud Security Platforms: Protect hybrid deployments and cloud applications. The Cyber Security Placement in Anna Nagar builds career confidence and technical assurance.
- Threat Intelligence Tools: Analyze vulnerabilities and predict risks. Training empowers learners with risk management and organizational resilience.
- Monitoring Dashboards: Track system health and compliance metrics. Training strengthens productivity, reporting expertise, and enterprise efficiency.
Techniques and Trends Observed in Cyber Security Certification in Anna Nagar
Modern workplace trends are integrated into the curriculum, ensuring learners remain future‑ready. Students are introduced to advanced features such as AI‑driven threat detection, zero‑trust frameworks, and cloud‑native security. Essential skills such as vulnerability assessment, compliance auditing, and penetration testing are emphasized alongside technical expertise. The program ensures learners remain competitive in rapidly evolving IT environments. By mastering these skills, students contribute meaningfully to productivity and innovation. Continuous learning is encouraged to stay aligned with future developments. Learners also gain exposure to integration with enterprise systems and global compliance frameworks. The Cyber Security Certification in Anna Nagar validates technical assurance and compliance readiness.
Requirements Needed for a Cyber Security Training Course
- Basic IT Knowledge: Familiarity with operating systems and networking concepts. The Cyber Security Course in Anna Nagar ensures readiness for enterprise projects.
- Programming Awareness: Understanding of scripting languages like Python or PowerShell enhances automation. Training equips learners with adaptability and analytical confidence.
- Security Concepts: Awareness of encryption and compliance policies supports data protection. The Cyber Security Certification in Anna Nagar builds technical assurance and compliance readiness.
- Analytical Skills: Ability to interpret logs and optimize system performance. Training empowers learners with risk management and organizational resilience.
- Problem‑Solving: Ability to debug and resolve technical issues effectively. Training strengthens productivity, reporting expertise, and enterprise efficiency.
Goals Achieved Through Cyber Security Training and Potential Career Paths
Learners benefit from the program by progressing into advanced career roles. Opportunities include security analyst, penetration tester, and compliance auditor. In this context, Cyber Security Training in Anna Nagar ensures career confidence and enterprise readiness. The program highlights advanced certifications to validate expertise. Networking and mentorship opportunities are emphasized to accelerate career development. By following these pathways, learners achieve sustained success and long‑term career stability. With the Cyber Security Placement in Anna Nagar, participants evolve from mastering fundamentals to guiding teams and driving organizational efficiency. Learners also gain exposure to enterprise‑level projects that prepare them for global opportunities. This block ensures learners are prepared for both career advancement and lifelong learning.
Career Opportunities After Cyber Security Training
Ethical Hacker (Penetration Tester)
Conducts simulated cyberattacks to identify vulnerabilities. Uses tools like Kali Linux and Metasploit to enhance security and provides detailed reports with actionable recommendations.
Security Analyst
Monitors networks and systems for unusual activities. Analyzes logs, detects breaches, coordinates incident response, and ensures compliance with security standards.
Network Security Engineer
Designs and implements secure network architectures. Configures firewalls, VPNs, and intrusion detection systems to maintain integrity and resilience against threats.
Cyber Forensics Expert
Investigates digital crimes and retrieves critical data. Analyzes digital footprints, prepares forensic reports, and supports law enforcement and legal processes.
Cloud Security Specialist
Secures cloud infrastructure with encryption, IAM policies, and compliance measures. Monitors applications, prevents unauthorized access, and collaborates.
Security Consultant
Advises companies on best practices and risk mitigation. Conducts audits, implements compliance standards, trains staff, and provides expert insights to strengthen defenses.
Skills to Master
Network Security
Ethical Hacking
Vulnerability Assessment
Penetration Testing
Incident Response
SIEM Management
Threat Intelligence
Data Encryption
Risk Management
Compliance Auditing
Cloud Security
Digital Forensics
Tools to Master
Kali Linux
Metasploit Framework
Burp Suite
Wireshark
Nessus
Splunk SIEM
OpenVAS
Nmap
Snort IDS/IPS
AWS Security Hub
IBM QRadar
ELK Stack
Learn from certified professionals who are currently working.

Training by
Priya, having 13 yrs of experience
Specialized in: Cyber Security domains: Ethical Hacking, Threat Analysis, and Incident Response Training.
Note: Priya is recognized for simplifying advanced cybersecurity concepts and delivering real-time, hands-on defense strategy sessions.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Cyber Security Training Certification

- Validates your expertise in ethical hacking and defense mechanisms.
- Boosts credibility in IT security and data protection roles.
- Opens global career opportunities in cybersecurity.
- Enhances practical knowledge through live projects.
Provides in-depth understanding of network defense, risk management, and data security. Enhances employability with hands-on exposure to real-world hacking simulations and compliance frameworks.
Employers prioritize certified professionals for roles requiring advanced technical defense and security compliance skills.
Basic understanding of networks, operating systems, and programming is beneficial. Prior experience in IT or system administration can help but is not mandatory.
- Understand certification objectives
- Practice hands-on labs regularly
- Review real-world attack case studies
- Attempt mock exams
Yes, candidates can register and complete official certifications online or through authorized testing centers in Anna Nagar. Remote proctored options are also available for flexibility.
- Basic IT infrastructure understanding
- Knowledge of operating systems
- Interest in ethical hacking and defense
- Analytical problem-solving approach
- Willingness to practice hands-on labs
Absolutely. With the rising number of cyber threats and security breaches, skilled professionals are in high demand. The course offers strong placement support, industry-recognized certification, and lucrative career opportunities across industries.
Frequently Asked Questions
- No, the course is designed for both beginners and professionals interested in cybersecurity.
- You’ll learn ethical hacking, network defense, incident response, and compliance frameworks.
- Students receive guidance on project completion, resume building, and mock interviews.
- Yes, an industry-recognized Cyber Security certification is awarded post-assessment.
- Yes, cybersecurity offers vast job opportunities across IT, banking, government, and cloud security industries.
)



