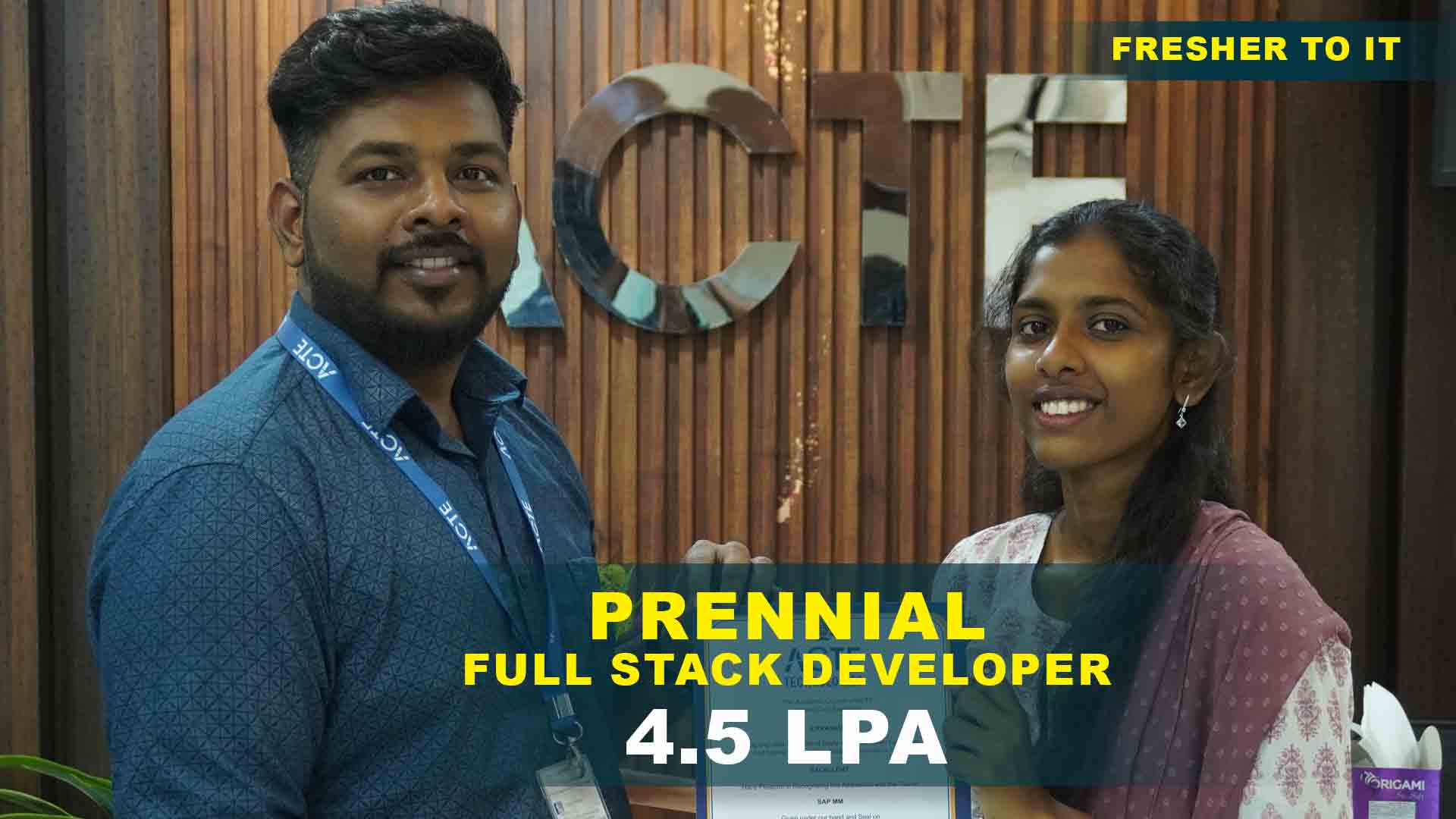
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculum Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
Ethical Hacking Training Projects
Become a Ethical Hacking Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Fundamentals of Ethical Hacking
Learn the basic principles of ethical hacking, cybersecurity concepts, and how security professionals identify vulnerabilities to protect systems and networks.
Vulnerability Assessment & Penetration Testing
Understand how to detect security weaknesses through vulnerability assessment and perform penetration testing using industry-standard ethical hacking tools.
Network Security & Threat Prevention
Gain practical knowledge in securing networks, identifying cyber threats, and applying effective strategies to prevent attacks and safeguard digital assets.
Security Monitoring & Threat Detection
Learn how to monitor systems and networks for suspicious activities, detect potential cyber threats, and maintain strong security across IT environments.
Ethical Hacking Tools & Techniques
Understand how to configure and use popular ethical hacking tools to identify vulnerabilities, perform security testing, and strengthen system defenses.
Security Analysis & Issue Resolution
Develop the ability to analyze security risks, troubleshoot vulnerabilities, and apply effective solutions to protect systems from cyber attacks.
Ethical Hacking Practical Project
Work on a hands-on cybersecurity project where you perform vulnerability scanning, security testing, and apply ethical hacking techniques to secure systems.
Enterprise Security Implementation
Gain experience implementing security practices in enterprise environments, focusing on protecting networks, applications, and sensitive organizational data.
End-to-End Cybersecurity Project
Complete a full cybersecurity project that includes threat identification, penetration testing, risk assessment, and implementing effective security solutions.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Ethical Hacking TrainingOverview
Benefits Gained From Ethical Hacking Course in Pondicherry
Ethical Hacking Placement Certification Provides Strong Knowledge Of Cybersecurity Threats And Defense Mechanisms. It Helps Professionals Understand How Hackers Exploit System Vulnerabilities. Learners Gain Hands-On Experience With Security Tools And Testing Techniques. The Training Improves Analytical And Problem-Solving Skills. It Enhances Awareness Of Network And Web Application Security Risks. Certified Ethical Hackers Are Highly Valued In IT Industries. The Course Opens Opportunities In Government, Banking, And Corporate Sectors. It Supports Career Growth In Cybersecurity And Information Security Roles. Ethical Hacking Skills Help Protect Sensitive Organizational Data. Overall, It Builds A Secure And Rewarding Career Path In The Digital World.
Emerging Future Trends In Ethical Hacking Placement in Pondicherry
- AI-Powered Cybersecurity Tools :Training Now Includes Artificial Intelligence-Based Threat Detection. Students Learn How AI Identifies Unusual Network Behavior. Automation Tools Improve Vulnerability Scanning Speed. AI-Based Malware Analysis Is Becoming Popular. Prepares Learners For Next-Generation Security Roles.
- Cloud Security And Cloud Penetration Testing :Focus On Securing AWS, Azure, And Google Cloud Platforms. Training Covers Cloud Misconfiguration Testing. Students Learn Identity And Access Management Security. Cloud Data Protection Strategies Are Included. Demand Is Growing With Cloud Adoption.
- IoT Security Testing :Courses Include Security Testing For Smart Devices. Covers Vulnerabilities In Connected Systems. Hands-On Practice With IoT Attack Simulations. Focus On Firmware And Network Exploits. Important Due To Smart Device Growth.
- Mobile Application Security :Training Covers Android And iOS Security Testing. Focus On Identifying App Vulnerabilities. Students Learn Secure API Testing. Mobile Malware Analysis Basics Are Introduced. Growing Need With Increase In Mobile Apps.
- Bug Bounty And Ethical Disclosure Programs :Students Learn Responsible Vulnerability Disclosure. Introduction To Global Bug Bounty Platforms. Hands-On Practice In Reporting Security Flaws. Helps Build Real-World Cybersecurity Portfolios. Creates Freelance And Global Earning Opportunities.
Latest Advancements In Ethical Hacking Certification in Pondicherry
Modern Ethical Hacking Course Certifications Include Advanced Penetration Testing Labs. Real-Time Cyber Attack Simulations Are Integrated Into Training. Cloud And Hybrid Security Modules Are Added To Curriculum. Courses Cover The Latest OWASP Top 10 Vulnerabilities. Advanced Tools Like Metasploit And Burp Suite Are Widely Used. Malware Analysis And Digital Forensics Basics Are Introduced. Training Includes Live Capture The Flag (CTF) Challenges. Security Automation And Scripting Techniques Are Taught. Emphasis Is Given To Compliance And Data Privacy Laws. Overall, Courses Are Designed To Match Global Cybersecurity Standards.
Main Concepts Behind Ethical Hacking Placement Programs In Pondicherry
- Industry-Oriented Curriculum :Programs Are Designed Based On Current Cybersecurity Needs. Focus On Practical Tools And Real-Time Labs. Covers Network, Web, And Cloud Security. Aligns With Industry Certification Standards. Prepares Students For Technical Interviews.
- Hands-On Lab Practice :Dedicated Lab Environment For Ethical Testing. Simulated Cyber Attack Scenarios. Practice On Vulnerable Applications. Improves Technical Confidence. Bridges Theory And Real-World Practice.
- Certification Preparation :Guidance For Global Security Certifications. Mock Tests And Exam-Oriented Training. Covers Important Security Domains. Helps Validate Professional Skills. Boosts Employability In Cybersecurity.
- Placement Assistance Support :Resume Building And LinkedIn Optimization. Mock Interviews With Technical Experts. Job Referrals Through Industry Connections. Soft Skills And Communication Training. Continuous Career Guidance Support.
- Real-Time Project Exposure :Work On Live Security Assessment Projects. Conduct Vulnerability Analysis Reports. Practice Ethical Disclosure Methods. Team-Based Security Audits. Build Strong Practical Experience For Jobs.
Real-Time Projects Completed Recently In Ethical Hacking Placements
Ethical Hacking Training with Placement students Recently Completed Full Network Penetration Testing Projects In Lab Environments. Web Application Security Audits Based On OWASP Standards Were Successfully Conducted. Vulnerability Scanning And Risk Assessment Reports Were Prepared For Simulated Corporate Systems. Wireless Network Security Testing Projects Were Executed Using Ethical Tools. Cloud Security Misconfiguration Assessments Were Performed In Practice Labs. Mobile Application Security Testing Projects Were Completed With API Analysis. Social Engineering Awareness Simulations Were Conducted For Educational Purposes. Basic Malware Analysis Projects Were Executed In Controlled Sandboxes. Incident Response And Log Analysis Case Studies Were Practiced. These Projects Helped Students Gain Real-Time Experience And Placement Opportunities In Cybersecurity Roles.
Career Opportunities After Ethical Hacking Training
Ethical Hacker
Ethical Hackers identify security vulnerabilities in systems and networks. They perform authorized penetration testing to help organizations strengthen cybersecurity and protect sensitive data.
Penetration Tester
Penetration Testers simulate cyberattacks to evaluate the security of applications, networks, and systems. They analyze weaknesses and recommend solutions to improve overall security.
Cybersecurity Analyst
Cybersecurity Analysts monitor networks and systems for threats. They investigate security incidents, analyze risks, and implement protective measures to safeguard digital infrastructure.
Security Operations Center (SOC) Analyst
SOC Analysts continuously monitor security events and respond to cyber threats. They use advanced tools to detect suspicious activity and ensure organizational security.
Network Security Engineer
Network Security Engineers design and implement security measures to protect networks from cyberattacks. They configure firewalls, monitor traffic, and maintain secure network environments.
Information Security Consultant
Information Security Consultants advise organizations on improving their cybersecurity strategies. They assess risks, design security frameworks, and implement best practices to protect critical data.
Skill to Master
Fundamentals of Ethical Hacking
Network Security Concepts
Vulnerability Assessment Techniques
Penetration Testing Methods
Password Cracking & Authentication Attacks
Web Application Security
Malware Analysis & Threat Detection
Wireless Network Security
System Security Monitoring
Incident Response & Risk Management
Security Tools & Ethical Hacking Frameworks
Critical Thinking & Cybersecurity Problem Solving
Tools to Master
Ethical Hacking Fundamentals
Cybersecurity Frameworks & Practices
Network Security & Penetration Testing
Web Application Security Testing
Data Protection & Security Controls
Vulnerability Scanning & Assessment
Cybersecurity Monitoring Tools
Threat Detection & Incident Response
Security Operations & Risk Management
System Security Analysis & Optimization
Ethical Hacking Tools & Simulations
Secure Deployment & Security Best Practices
Learn from certified professionals who are currently working.

Training by
Aravind Raj,having 12 yrs of experience
Specialized in: Cybersecurity Operations, Cloud Security, Malware Analysis, Digital Forensics, And Incident Response
Note: Aravind Raj Is Known For His Strong Expertise In Real-Time Threat Detection And His Ability To Prepare Students For Global Cybersecurity Certifications.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Ethical HackingCertification

Ethical Hacking Helps You Understand How Cyber Attacks Happen And How To Prevent Them. It Builds Strong Knowledge In Network, Web, Ethical Hacking Placement Certification And System Security.
The Main Goal Is To Train Students To Identify Security Weaknesses Before Hackers Exploit Them. Ethical Hacking Course Certifications it Aims To Develop Practical Skills Through Real-Time Labs And Simulations.
The Course Aims To Build A Strong Foundation In Cybersecurity Concepts. Ethical Hacking Training with Placement it Focuses On Practical Penetration Testing And Security Assessment Skills.
Frequently Asked Questions
- Yes, The Ethical Hacking Course Offers Both Classroom And Online Training Options. Ethical Hacking Placement Certification students Can Choose Flexible Batch Timings Based On Their Availability. Practical Lab Sessions Are Included In Both Modes.
- The Course Typically Ranges From 1 To 3 Months Based On The Learning Mode.
- Fast-Track And Weekend Batches Are Available For Working Professionals.
- Duration May Vary Depending On Advanced Modules And Certification Preparation.
- Yes, Students Work On Industry-Relevant Security Testing Projects And Real-Time Lab Scenarios. Ethical Hacking Placement in Pondicherry these Projects Help Build Practical Skills And Professional Confidence.
- Resume Building And Profile Optimization Support Is Provided.
- Mock Interviews And Technical Assessment Sessions Are Conducted.
- Eligible Candidates Are Referred To Hiring Companies Through Placement Assistance.
- Yes, The Course Includes Interview Preparation Support Such As Technical Q&A Sessions, Mock Interviews, Ethical Hacking Certification in Pondicherry And Career Guidance To Help You Succeed In Job Interviews.
)



