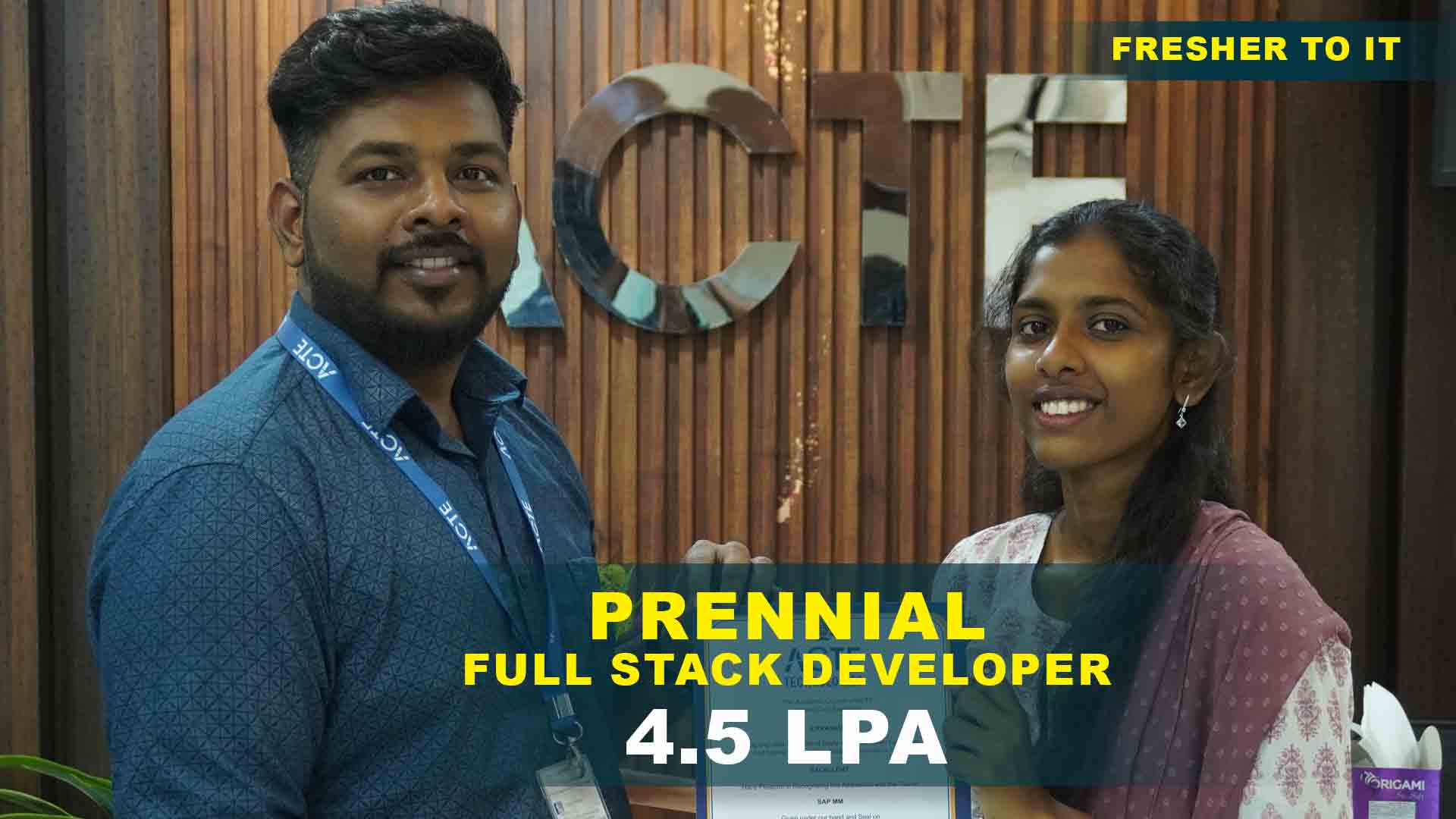
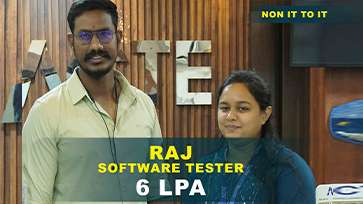
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculam Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
Cyber Security Training Projects
Become a Cyber Security Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Personal Computer Security Assessment
Analyze and evaluate the security settings of a personal computer. Identify vulnerabilities such as weak passwords, outdated software, and misconfigured firewalls. Learn basic security controls.
Network Vulnerability Scan
Perform a vulnerability scan on a test network using tools like Nmap or Nessus. Identify open ports, services, and security gaps. Understand foundational network security principles.
Password Strength Analyzer
Create a system or script to evaluate password strength and enforce security policies. Understand authentication risks and best practices for secure password management.
Small Business Network Security Setup
Design and implement security measures for a small business network, including firewall configuration, VLANs, and user access controls. Build practical network security skills.
Web Application Vulnerability Testing
Perform vulnerability assessments on a sample web application. Identify SQL injection, XSS, and other common threats. Enhance knowledge of secure coding and web security practices.
Incident Response Simulation
Simulate a security incident including detection, analysis, and mitigation. Prepare incident reports and develop response strategies to improve real-world readiness.
Penetration Testing of Enterprise Network
Conduct a full penetration test on a simulated enterprise environment. Identify vulnerabilities and recommend remediation strategies.
Advanced Malware Reverse Engineering
Reverse engineer sophisticated malware to understand its behavior, payloads, and propagation methods. Build in-depth malware analysis expertise.
SIEM Implementation
Deploy and configure a Security Information and Event Management (SIEM) system. Monitor, detect, and respond to security incidents in real time
)















 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
 Hands-On Projects
Hands-On Projects
 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
 Interview Preparation
For Freshers
Interview Preparation
For Freshers
 LMS Online Learning
Platform
LMS Online Learning
Platform


