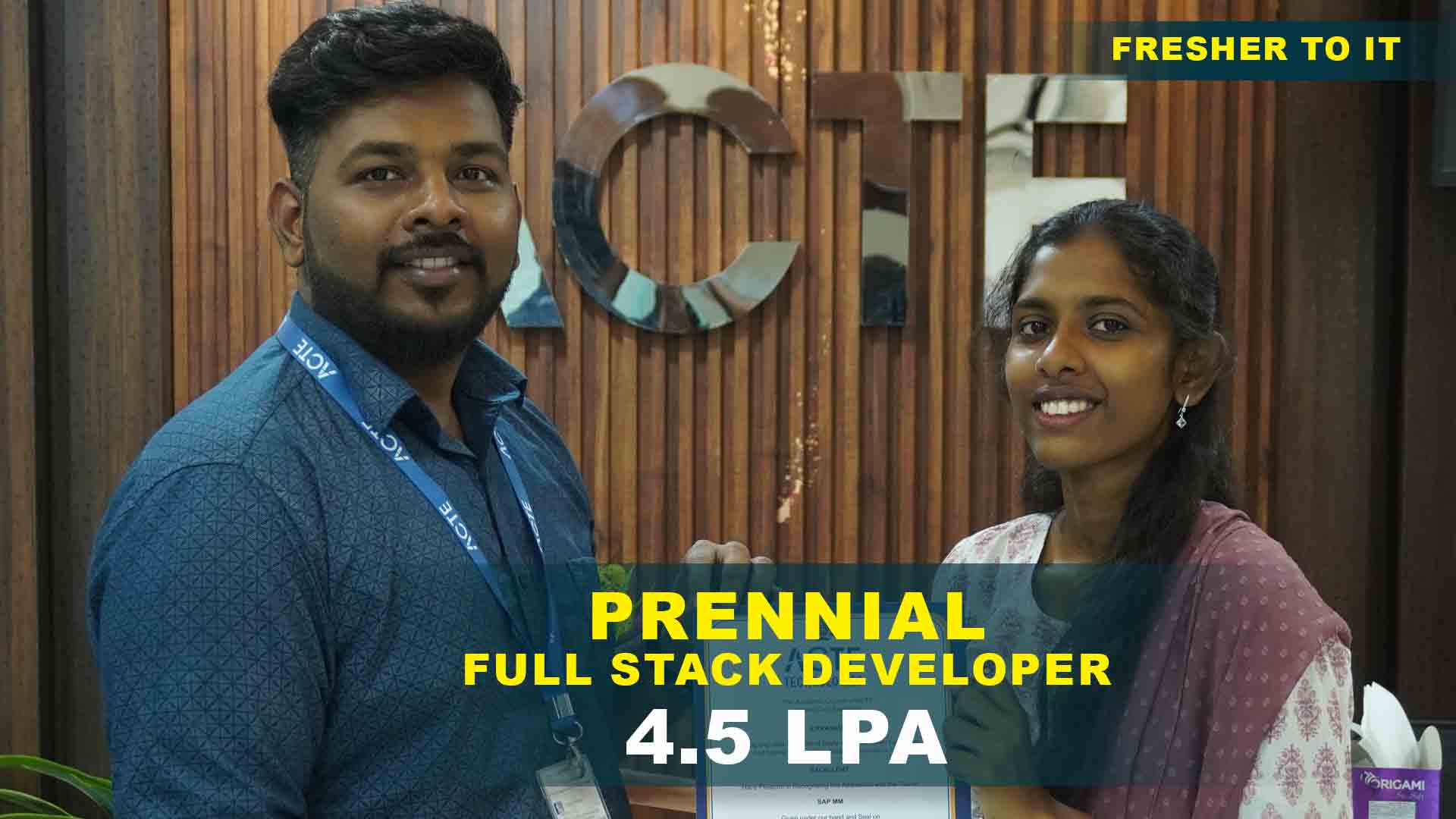
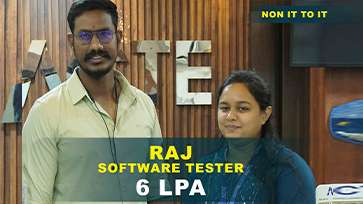
550+ Students Placed Every Month Be The Next!






















Our Hiring Partners




Curriculum Designed By Experts
Expertly designed curriculum for future-ready professionals.
Industry Oriented Curriculum
An exhaustive curriculum designed by our industry experts which will help you to get placed in your dream IT company
-
30+ Case Studies & Projects
-
9+ Engaging Projects
-
10+ Years Of Experience
Ethical Hacking Training Projects
Become a Ethical Hacking Expert With Practical and Engaging Projects.
- Practice essential Tools
- Designed by Industry experts
- Get Real-world Experience
Basic Network Scanning
Use tools like Nmap to scan and map network devices and open ports. Understand how to interpret scan results to identify potential entry points.
Simple Password Cracking
Practice password cracking techniques using tools like John the Ripper on sample datasets. Learn about password strength and common vulnerabilities.
Social Engineering Awareness
Simulate phishing attempts and study human vulnerabilities in cybersecurity. Develop skills to recognize and defend against social engineering attacks.
Vulnerability Assessment Using Nessus
Conduct a vulnerability scan and generate reports on identified security risks. Prioritize vulnerabilities based on severity for effective mitigation.
Exploiting Web Application Vulnerabilities
Test and exploit SQL Injection and Cross-Site Scripting (XSS) vulnerabilities on test applications. Understand how attackers manipulate inputs.
Man-in-the-Middle Attack Simulation
Perform MITM attacks using tools like Ettercap in a controlled lab environment. Learn how encrypted traffic can be intercepted and analyzed .
Advanced Penetration Testing
Execute full penetration testing on a target system covering reconnaissance to exploitation. Document findings and suggest actionable remediation steps.
Malware Analysis and Reverse Engineering
Analyze suspicious files and understand malware behavior using sandboxing techniques. Gain insights into how malware evades detection..
Wireless Network Hacking
Crack WPA2 Wi-Fi networks and test wireless security using the Aircrack-ng suite. Explore methods to secure wireless networks against such attacks.
Career Support

Placement Assistance
Exclusive access to ACTE Job portal

Mock Interview Preparation
1 on 1 Career Mentoring Sessions
Career Oriented Sessions
Resume & LinkedIn Profile Building
Key Features

Practical Training

Global Certifications

Flexible Timing

Trainer Support

Study Material

Placement Support

Mock Interviews

Resume Building
Upcoming Batches
What's included

 Free Aptitude and
Technical Skills Training
Free Aptitude and
Technical Skills Training
- Learn basic maths and logical thinking to solve problems easily.
- Understand simple coding and technical concepts step by step.
- Get ready for exams and interviews with regular practice.

 Hands-On Projects
Hands-On Projects
- Work on real-time projects to apply what you learn.
- Build mini apps and tools daily to enhance your coding skills.
- Gain practical experience just like in real jobs.

 AI Powered Self
Interview Practice Portal
AI Powered Self
Interview Practice Portal
- Practice interview questions with instant AI feedback.
- Improve your answers by speaking and reviewing them.
- Build confidence with real-time mock interview sessions.

 Interview Preparation
For Freshers
Interview Preparation
For Freshers
- Practice company-based interview questions.
- Take online assessment tests to crack interviews
- Practice confidently with real-world interview and project-based questions.

 LMS Online Learning
Platform
LMS Online Learning
Platform
- Explore expert trainer videos and documents to boost your learning.
- Study anytime with on-demand videos and detailed documents.
- Quickly find topics with organized learning materials.
- Learning strategies that are appropriate and tailored to your company's requirements.
- Live projects guided by instructors are a characteristic of the virtual learning environment.
- The curriculum includes of full-day lectures, practical exercises, and case studies.

Ethical Hacking CourseOverview
Uses of Ethical Hacking Training in Madurai
Ethical Hacking Training Course in Madurai equips learners with skills to identify and fix security vulnerabilities in computer systems and networks. This training is essential for protecting organizations against cyber threats, data breaches, and malicious attacks. Ethical hackers simulate cyberattacks to strengthen defenses, ensuring systems are robust and compliant with security standards. The course also builds awareness of real-world cyber risks faced by enterprises. Learners gain hands-on experience to proactively secure digital infrastructures.
Industry Projects of Ethical Hacking Certification in Madurai
- Basic Networking & Security Knowledge: A fundamental understanding of TCP/IP, DNS, HTTP, firewalls, VPNs, and IDS/IPS is necessary for ethical hacking. Knowledge of network vulnerabilities and security measures helps in penetration testing and security assessments. This foundation enables learners to analyze network traffic effectively. It also helps identify loopholes in enterprise network architectures.
- Proficiency in Programming: Understanding programming languages like Python, C, Java, Bash scripting, and PowerShell is essential for automating security testing and analyzing vulnerabilities. Web-based ethical hacking requires familiarity with JavaScript, PHP, and SQL for identifying web application flaws. Programming skills improve automation efficiency. They also help in writing custom exploit scripts and tools.
- Problem-Solving & Analytical Skills: Ethical hackers must think like cybercriminals to anticipate threats and devise countermeasures. Strong analytical skills are necessary to interpret security reports, troubleshoot vulnerabilities, and design security policies. This mindset helps in predicting attack patterns. It also supports faster incident response and remediation.
- Ethical & Legal Awareness: Ethical hacking Trainer must comply with cyber laws and ethical hacking guidelines such as GDPR, HIPAA, and ISO 27001. Understanding the Computer Fraud and Abuse Act (CFAA) and Digital Millennium Copyright Act (DMCA) helps professionals operate within legal boundaries. Legal awareness protects professionals from violations. It ensures responsible and authorized security testing practices.
About Ethical Hacking Training in Madurai
Ethical Hacking Training in Madurai covers key topics such as penetration testing, threat modeling, cryptography, and cyber law. The course combines theory with practical labs using tools like Kali Linux, Metasploit, and Wireshark. It prepares learners to think like hackers ethically, identifying weaknesses and improving security posture effectively. With an increase in the frequency and sophistication of cyberattacks, ethical hacking professionals are now more important than ever in maintaining the integrity, confidentiality, and availability of data. The training also emphasizes real-time attack simulations. This helps learners understand modern threat landscapes in depth.
Skills in Ethical Hacking Training Course in Madurai
- Penetration Testing & Red Teaming: Ethical hackers use penetration testing (pen testing) techniques to simulate real-world attacks on networks, applications, and hardware. Red teaming is an advanced technique where ethical hackers act as adversaries to test an organization's cyber defenses. These practices help uncover hidden vulnerabilities. They also improve an organization’s overall security maturity.
- Social Engineering Attacks: Cybercriminals exploit human psychology using techniques like phishing emails, vishing (voice phishing), pretexting, and baiting. Ethical hackers must understand these tactics to train employees and develop countermeasures. This knowledge helps reduce human-based security risks. It strengthens organizational awareness and security culture.
- AI & Machine Learning in Cybersecurity: AI-based security tools analyze vast amounts of data to detect anomalies, malware behavior, and phishing attempts. Ethical hackers must learn AI-driven threat intelligence and automated security testing to stay ahead of cybercriminals. AI improves detection accuracy and speed. It enables proactive threat prediction and response.
- Cloud Security & Ethical Hacking: With businesses migrating to cloud platforms like AWS, Azure, and Google Cloud, ethical hackers focus on cloud misconfiguration assessments, API security testing, and container security. Cloud penetration testing ensures compliance with security frameworks like ISO 27017 and NIST. Cloud security skills are critical for modern IT environments. They help protect scalable and distributed infrastructures.
Company Role Opportunities in Ethical Hacking Course in Madurai
Graduates of Ethical Hacking Certification in Madurai find roles as penetration testers, security analysts, cybersecurity consultants, and incident responders. Companies across IT, finance, government, and defense sectors seek these professionals to safeguard digital assets, conduct security audits, and ensure compliance with data protection laws. The demand for ethical hackers continues to rise globally. These roles offer strong career growth and competitive salaries.
Career Opportunities After Ethical Hacking
Penetration Tester
Conduct simulated cyberattacks to identify vulnerabilities in systems and networks, providing detailed reports to strengthen security. They help organizations stay one step ahead of potential attackers.
Security Analyst
Monitor security systems, analyze threats, and respond to security breaches to protect organizational data. They play a critical role in day-to-day threat detection and prevention
Cybersecurity Consultant
Advise businesses on best practices for securing their critical digital assets and help develop comprehensive security policies. They tailor customized solutions based on each client’s infrastructure and specific needs.
Network Security Engineer
Design and implement network security measures, including firewalls and intrusion detection systems. They ensure data flows securely across all devices and platforms.
Incident Response Specialist
Lead investigations and effectively manage responses to cyber incidents and data breaches. They act quickly to minimize damage and restore critical operations.
Malware Analyst
Analyze malicious software to understand its behavior and develop defenses against threats.They provide insights that help improve antivirus and threat intelligence systems.
Skill to Master
Network Security Fundamentals
Penetration Testing Techniques
Vulnerability Assessment
Ethical Hacking Methodologies
Kali Linux Proficiency
Exploit Development
Exploit Development
Cryptography Basics
Web Application Security
Social Engineering Tactics
Malware Analysis
Security Tools Usage
Tools to Master
Kali Linux
Metasploit Framework
Wireshark
Nmap
Burp Suite
John the Ripper
Aircrack-ng
Nessus
OWASP ZAP
Netcat
SQLmap
Maltego
Learn from certified professionals who are currently working.

Training by
Maya, having 7+ yrs of experience
Specialized in: Penetration Testing, Vulnerability Assessment, Network Security, Web Application Security, and Ethical Hacking Tools.
Note: Maya is a seasoned cybersecurity expert with extensive hands-on experience using tools like Metasploit, Burp Suite, and Nmap. She has a track record of discovering and addressing security vulnerabilities in complex systems.
Premium Training at Best Price
Affordable, Quality Training for Freshers to Launch IT Careers & Land Top Placements.
What Makes ACTE Training Different?
Feature
ACTE Technologies
Other Institutes
Affordable Fees
Competitive Pricing With Flexible Payment Options.
Higher Fees With Limited Payment Options.
Industry Experts
Well Experienced Trainer From a Relevant Field With Practical Training
Theoretical Class With Limited Practical
Updated Syllabus
Updated and Industry-relevant Course Curriculum With Hands-on Learning.
Outdated Curriculum With Limited Practical Training.
Hands-on projects
Real-world Projects With Live Case Studies and Collaboration With Companies.
Basic Projects With Limited Real-world Application.
Certification
Industry-recognized Certifications With Global Validity.
Basic Certifications With Limited Recognition.
Placement Support
Strong Placement Support With Tie-ups With Top Companies and Mock Interviews.
Basic Placement Support
Industry Partnerships
Strong Ties With Top Tech Companies for Internships and Placements
No Partnerships, Limited Opportunities
Batch Size
Small Batch Sizes for Personalized Attention.
Large Batch Sizes With Limited Individual Focus.
LMS Features
Lifetime Access Course video Materials in LMS, Online Interview Practice, upload resumes in Placement Portal.
No LMS Features or Perks.
Training Support
Dedicated Mentors, 24/7 Doubt Resolution, and Personalized Guidance.
Limited Mentor Support and No After-hours Assistance.
We are proud to have participated in more than 40,000 career transfers globally.

Ethical HackingCertification

Yes, there are several globally recognized certifications in Ethical Hacking. These include Certified Ethical Hacker, Offensive Security Certified Professional, CompTIA Security+, and GIAC Penetration Tester.
While it guarantee a job, an Ethical Hacking Training with Certification greatly boosts your chances by validating your skills and making you stand out to employers.
Yes you can take the Ethical Hacking Training with Certification exam online, Convenient and Flexible Schedule your test at a time that suits you, without needing to travel to a test center.
Yes, ACTE’s Ethical Hacking Training Course in Madurai is a valuable investment. The course includes hands-on training with real-world tools, expert instruction, and placement support.
Frequently Asked Questions
- Yes, the course starts from basics, making it ideal for beginners with no prior cybersecurity experience.
- IT professionals
- Students
- Software developers
- System admins
- Ethical Hacker
- Penetration Tester
- Security Analyst
- Cybersecurity Consultant
- Yes, you will receive a certificate from ACTE upon completing the Ethical Hacking course successfully.
- Live projects are assigned based on current cybersecurity threats and tools, involving tasks like vulnerability scanning, network testing, and web application security audits under instructor guidance.
)



